trolatunt - 22% Detection Rate *
Did you just stumble upon a download or a file on your computer that is digitally signed by trolatunt? Some of the security products refers to the detected files as Trolatunt.B88 and Adware.Win32.BrowseFox.BB. The detection rate for the trolatunt files collected here is 22%. Please read on for more details.
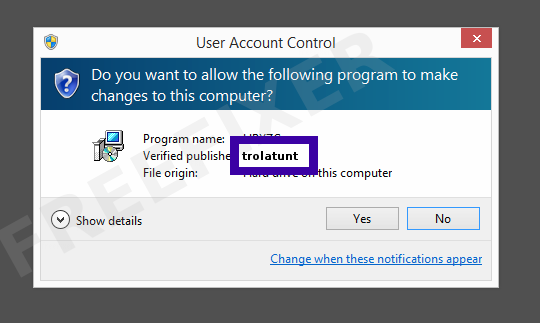
You will typically see trolatunt when double-clicking to run the file. The publisher name is then displayed as the "Verified publisher" in the UAC dialog as the screenshot shows:
You can also view the trolatunt certificate with the following steps:
- Open Windows Explorer and locate the trolatunt file
- Right-click on the file and select Properties
- Click the Digital Signatures tab
- Click on the View Certificate button
Here's a screenshot of a file digitally signed by trolatunt:
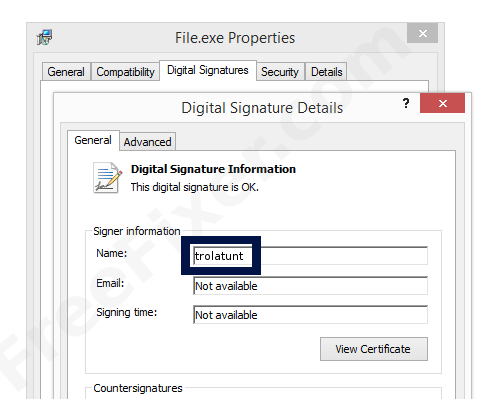
As you can see in the screenshot above, Windows states that "This digital signature is OK". This means that the file has been published by trolatunt and that no one has tampered with the file.
If you click the View Certificate button shown in the screenshot above, you can view all the details of the certificate, such as when it was issued, who issued the certificate, how long it is valid, and so on. You can also see the address for trolatunt, such as the street name, city and country.
VeriSign Class 3 Code Signing 2010 CA has issued the trolatunt certificates. You can also see the details of the issuer by clicking the View Certificate button shown in the screengrab above.
trolatunt Files
The following are the trolatunt files I have collected, thanks to the FreeFixer users.
Scanner and Detection Names
Here is the detection names for the trolatunt files. I've grouped the detection names by each scanner engine. Thanks to VirusTotal for the scan results.
| Scanner | Detection Names |
|---|---|
| AVG | BHO.YAB, Trolatunt.B88, BrowseFox.F, AdPlugin.CWT |
| AVware | Yontoo (fs), Adware.SwiftBrowse, Trojan.Win32.Generic!BT |
| Ad-Aware | Gen:Variant.Adware.BHO.Agent.4, Adware.SwiftBrowse.CO, Adware.NetFilter.E |
| Agnitum | PUA.Agent!, Trojan.BPlug!, PUA.Yotoon!, Riskware.Agent! |
| AhnLab-V3 | Adware/Win32.SwiftBrowse, Trojan/Win64.SwiftBrowse, PUP/Win32.BrowseFox |
| AntiVir | APPL/BrowseFox.Gen2 |
| Antiy-AVL | GrayWare[AdWare:not-a-virus]/Win32.Agent, Trojan/Win32.TSGeneric, GrayWare[AdWare:not-a-virus]/Win32.Kranet, GrayWare[AdWare:not-a-virus]/Win64.Agent |
| Arcabit | Adware.SwiftBrowse.CO |
| Avast | Win32:Truntalol-C [PUP], Win32:Adware-BYZ [PUP], Win32:BrowseFox-JA [PUP] |
| Avira | ADWARE/BrowseFox.Gen7, ADWARE/BrowseFox.ape |
| Baidu-International | Adware.Win32.BrowseFox.BB, Adware.Win32.BrowseFox.bH, Adware.Win32.BrowseFox.BD |
| BitDefender | Gen:Variant.Adware.BHO.Agent.4, Adware.SwiftBrowse.CO, Adware.NetFilter.E |
| Bkav | W32.HfsAdware.19D8 |
| CAT-QuickHeal | PUA.Trolatunt.Gen |
| ClamAV | Win.Adware.Agent-22685, Win.Adware.Swiftbrowse-75, Win.Adware.Agent-41785 |
| Comodo | Application.Win32.Altbrowse.AK, Application.Win32.BrowseFox.B, Application.Win32.BrowseFox.AHJ |
| Cyren | W32/S-11fc74d1!Eldorado |
| DrWeb | Trojan.BPlug.17, Trojan.BPlug.141, Trojan.BPlug.123, Trojan.BPlug.117, Trojan.BPlug.281, Trojan.Yontoo.1734 |
| ESET-NOD32 | a variant of Win32/BrowseFox.F, a variant of MSIL/BrowseFox.H, a variant of Win32/BrowseFox.H, Win32/BrowseFox.V, a variant of Win64/BrowseFox.AY, Win32/BrowseFox.BD potentially unwanted |
| Emsisoft | Gen:Variant.Adware.BHO.Agent.4 (B), Adware.SwiftBrowse.CO (B), Adware.NetFilter.E (B) |
| F-Prot | W32/A-de841313!Eldorado, W64/A-e967bae2!Eldorado, W32/S-11fc74d1!Eldorado |
| F-Secure | Gen:Variant.Adware.BHO.Agent.4, Adware.SwiftBrowse.CO, Adware.NetFilter.E |
| Fortinet | Adware/Agent |
| GData | Gen:Variant.Adware.BHO.Agent.4, Adware.SwiftBrowse.CO, Adware.NetFilter.E |
| Ikarus | not-a-virus:AdWare.Win32.Agent, AdWare.SpadeCast, AdWare.SwiftBrowse |
| Jiangmin | AdWare/Yotoon.m, AdWare/Yotoon.l, AdWare/SwiftBrowse.ssl |
| K7AntiVirus | Trojan ( 004af26b1 ), Riskware ( 0049c6851 ), Adware ( 004b92811 ) |
| K7GW | Trojan ( 004af26b1 ), Riskware ( 0049c6851 ), Adware ( 004b92811 ) |
| Kaspersky | not-a-virus:AdWare.Win32.Agent.ahbx, not-a-virus:AdWare.Win32.Yotoon.bfm |
| Kingsoft | Win32.Troj.Agent.ah.(kcloud), Win32.Troj.Generic.a.(kcloud) |
| Malwarebytes | PUP.Optional.Trolatunt.A, PUP.Optional.BrowseFox |
| McAfee | Artemis!276C350FE57A, Artemis!4A6DCD4662CE, Artemis!7F4ACAC8DEFC, Artemis!F66B7E12F6E7, Artemis!EF2D1526BEBE, Artemis!F8A8AFE030AF, Artemis!046DA6A74CDC, BrowseFox-FXS |
| McAfee-GW-Edition | Artemis!276C350FE57A, Artemis!4A6DCD4662CE, Artemis!F66B7E12F6E7, Artemis!EF2D1526BEBE, BehavesLike.Win32.Downloader.ch, BehavesLike.Win64.PUPAmonetize.qm, BrowseFox-FXS |
| MicroWorld-eScan | Gen:Variant.Adware.BHO.Agent.4, Adware.SwiftBrowse.CO, Adware.NetFilter.E |
| NANO-Antivirus | Riskware.Win32.Agent.crkvek, Trojan.Win32.BPlug.dcxxfx, Riskware.Win32.Kranet.dgiwfc, Riskware.Win32.Yotoon.ddghtt, Trojan.Win32.Yontoo.dpmcsm |
| Panda | Trj/CI.A |
| Qihoo-360 | HEUR/QVM10.1.Malware.Gen |
| Rising | NS:PUF.SilenceInstaller!1.9DDF, PE:Trojan.Win32.Generic.175C048E!391906446, PE:AdWare.Win32.BrowseFox.i!1075357760 |
| SUPERAntiSpyware | Adware.BrowseFox/Variant |
| Sophos | Generic PUA NM, Browse Fox, BrowseSmart |
| Symantec | Yontoo.C |
| Tencent | Win32.Trojan.Falsesign.Duma, Win32.Trojan.Falsesign.Efau |
| TrendMicro-HouseCall | TROJ_GEN.F47V0603, Suspicious_GEN.F47V0627, TROJ_GEN.F47V0602, Suspicious_GEN.F47V0730, Suspicious_GEN.F47V0720, Suspicious_GEN.F47V0817 |
| VBA32 | AdWare.Win64.Yotoon, AdWare.Kranet, AdWare.DealKeeper |
| VIPRE | Yontoo (fs), Trojan.Win32.Generic!BT, Yontoo, Adware.SwiftBrowse |
| Zillya | Adware.Kranet.Win32.476, Adware.Yotoon.Win64.3, Adware.Yotoon.Win64.1, Adware.Agent.Win32.52012 |
| nProtect | Adware.SwiftBrowse.CO, Adware.NetFilter.E |
* How the Detection Percentage is Calculated
The detection percentage is based on the fact that I've collected 909 scan reports for the trolatunt files. 200 of these scan reports came up with some sort of detection. You can view the full details of the scan reports by examining the files listed above.
Analysis Details
The analysis is done on certificates with the following serial numbers:
- 16e5b55bc9746e627e43f6a38dde3e80