What is EBJeSN.exe?
EBJeSN.exe is usually located in the 'c:\downloads\' folder.
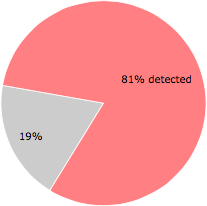
Some of the anti-virus scanners at VirusTotal detected EBJeSN.exe.
If you have additional information about the file, please share it with the FreeFixer users by posting a comment at the bottom of this page.
Digital signatures [?]
EBJeSN.exe is not signed.
VirusTotal report
57 of the 70 anti-virus programs at VirusTotal detected the EBJeSN.exe file. That's a 81% detection rate.
| Scanner | Detection Name |
|---|---|
| Acronis | suspicious |
| Ad-Aware | Trojan.VIZ.Gen.1 |
| AegisLab | Trojan.Win32.Zbot.l!c |
| AhnLab-V3 | Spyware/Win32.Zbot.R84198 |
| Alibaba | VirTool:Win32/Obfuscator.7936e174 |
| ALYac | Trojan.VIZ.Gen.1 |
| Antiy-AVL | Trojan[Spy]/Win32.Zbot |
| APEX | Malicious |
| Arcabit | Trojan.VIZ.Gen.1 |
| Avast | Win32:Downloader-UWY [Trj] |
| AVG | Win32:Downloader-UWY [Trj] |
| Avira | TR/Urausy.839684486 |
| BitDefender | Trojan.VIZ.Gen.1 |
| CAT-QuickHeal | TrojanPWS.Zbot.Gen |
| Comodo | TrojWare.Win32.Kryptik.BLUA@52iiih |
| CrowdStrike | win/malicious_confidence_90% (W) |
| Cybereason | malicious.f3f2c4 |
| Cylance | Unsafe |
| Cyren | W32/FakeAV.MPJU-7076 |
| DrWeb | Trojan.PackedENT.24465 |
| eGambit | Generic.Malware |
| Emsisoft | Trojan.VIZ.Gen.1 (B) |
| Endgame | malicious (high confidence) |
| ESET-NOD32 | a variant of Win32/Kryptik.BMBB |
| F-Secure | Trojan.TR/Urausy.839684486 |
| Fortinet | W32/Kryptik.BDPK!tr |
| GData | Trojan.VIZ.Gen.1 |
| Ikarus | Trojan-PWS.Win32.Fareit |
| Invincea | heuristic |
| Jiangmin | TrojanSpy.Zbot.dyvv |
| K7AntiVirus | Trojan ( 004ff4611 ) |
| K7GW | Trojan ( 004ff4611 ) |
| Kaspersky | HEUR:Trojan.Win32.Generic |
| Malwarebytes | Trojan.MalPack.FFS |
| MAX | malware (ai score=100) |
| McAfee | Generic-FANP!33FF431F3F2C |
| McAfee-GW-Edition | BehavesLike.Win32.PWSZbot.fc |
| Microsoft | VirTool:Win32/Obfuscator.WT |
| MicroWorld-eScan | Trojan.VIZ.Gen.1 |
| NANO-Antivirus | Trojan.Win32.Zbot.chyzje |
| Paloalto | generic.ml |
| Panda | Trj/Tepfer.B |
| Qihoo-360 | HEUR/Malware.QVM20.Gen |
| Rising | Trojan.Bagsu!8.3B1 (CLOUD) |
| SentinelOne | DFI - Malicious PE |
| Sophos | Troj/FakeAV-GVX |
| SUPERAntiSpyware | Trojan.Agent/Gen-Zbot |
| Symantec | Packed.Generic.443 |
| Tencent | Win32.Trojan.Generic.Llrr |
| TheHacker | Trojan/Kryptik.bphz |
| TrendMicro | BKDR_KELIHOS.SMF |
| TrendMicro-HouseCall | BKDR_KELIHOS.SMF |
| VBA32 | Trojan.FakeAV.01657 |
| Webroot | W32.InfoStealer.Zeus |
| Yandex | TrojanSpy.Zbot!1zlJZhdqmiU |
| Zillya | Trojan.Zbot.Win32.175534 |
| ZoneAlarm | HEUR:Trojan.Win32.Generic |
Sandbox Report
The following information was gathered by executing the file inside Cuckoo Sandbox.
Summary
Successfully executed process in sandbox.
Summary
{
"file_created": [
"C:\\Users\\cuck\\AppData\\LocalLow\\uloj.wae",
"C:\\Users\\cuck\\AppData\\Roaming\\Kidi\\vaegyv.exe",
"C:\\Users\\cuck\\AppData\\Local\\Temp\\FHF2E01.bat"
],
"regkey_written": [
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\bi76c7e",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\1gbabd40",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\ge60cic",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Run\\Vaegyv"
],
"dll_loaded": [
"ntdll.dll",
"WS2_32.dll",
"API-MS-Win-Security-SDDL-L1-1-0.dll",
"profapi.dll",
"IPHLPAPI.DLL",
"WININET.dll",
"CRYPT32.dll",
"ADVAPI32.dll",
"KERNEL32.dll",
"msvcrt.dll",
"Secur32.dll",
"GDI32.dll",
"NETAPI32.dll",
"VERSION.dll",
"SHELL32.dll",
"rpcrt4.dll",
"ole32.dll",
"SHLWAPI.dll",
"CRYPTSP.dll",
"USER32.dll",
"OLEAUT32.dll"
],
"file_opened": [
"C:\\",
"C:\\Users\\cuck\\AppData\\Local\\Temp\\a557fa363f1bce12c415a22d1d81905cc007e12bec6fb117f48275cf9b280e09.bin",
"C:\\Users\\cuck\\AppData\\Roaming\\Kidi",
"C:\\Users\\cuck\\AppData\\Roaming\\Kidi\\vaegyv.exe",
"C:\\Users\\cuck\\AppData\\Roaming",
"C:\\Users\\cuck\\AppData\\LocalLow"
],
"regkey_opened": [
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows NT\\CurrentVersion",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\User Shell Folders",
"HKEY_LOCAL_MACHINE\\Software\\Policies\\Microsoft\\Windows NT\\Rpc",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\KnownFolderSettings",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\FolderDescriptions",
"HKEY_LOCAL_MACHINE\\Software\\Policies\\Microsoft\\Windows\\CurrentVersion\\Internet Settings",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\PropertyBag",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Run",
"HKEY_LOCAL_MACHINE\\SYSTEM\\CurrentControlSet\\Services\\crypt32",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\PropertyBag",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Rpc",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows NT\\CurrentVersion\\ProfileList\\S-1-5-21-699399860-4089948139-3198924279-1001",
"HKEY_CURRENT_USER\\Software\\Microsoft",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\SessionInfo\\1\\KnownFolders",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\PropertyBag",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\PropertyBag",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Rpc\\SecurityService",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\SessionInfo\\1"
],
"command_line": [
"\"C:\\Users\\cuck\\AppData\\Roaming\\Kidi\\vaegyv.exe\"",
"\"C:\\Windows\\system32\\cmd.exe\" \/c \"C:\\Users\\cuck\\AppData\\Local\\Temp\\FHF2E01.bat\""
],
"file_written": [
"C:\\Users\\cuck\\AppData\\Roaming\\Kidi\\vaegyv.exe",
"C:\\Users\\cuck\\AppData\\Local\\Temp\\FHF2E01.bat"
],
"regkey_deleted": [
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Run\\internat.exe"
],
"file_exists": [
"C:\\cuckoo_1768.ini",
"C:\\Users\\cuck\\AppData\\Roaming",
"C:\\Users\\cuck\\AppData\\LocalLow",
"C:\\cuckoo_1636.ini",
"C:\\cuckoo_1700.ini",
"C:\\cuckoo_1788.ini",
"C:\\Users\\cuck\\AppData\\Roaming\\Kidi\\vaegyv.exe",
"C:\\Windows",
"C:\\cuckoo_1724.ini",
"C:\\cuckoo_1692.ini",
"C:\\cuckoo_1820.ini"
],
"mutex": [
"Global\\{224A23F9-3857-A1AF-E8E1-B06EFA019373}",
"Global\\{56060262-19CC-D5E3-A920-6470BBC0476D}",
"Global\\{224A23F9-3857-A1AF-70E3-B06E62039373}",
"Global\\{224A23F9-3857-A1AF-BCE8-B06EAE089373}",
"Global\\{224A23F9-3857-A1AF-60EB-B06E720B9373}",
"Local\\{C8B94219-59B7-4B5C-A920-6470BBC0476D}",
"Global\\{224A23F9-3857-A1AF-4CEC-B06E5E0C9373}",
"Global\\{224A23F9-3857-A1AF-E0E8-B06EF2089373}",
"Global\\{A5B32338-3896-2656-A920-6470BBC0476D}",
"Global\\{224A23F9-3857-A1AF-F4EB-B06EE60B9373}",
"Global\\{224A23F9-3857-A1AF-48EE-B06E5A0E9373}",
"Global\\{224A23F9-3857-A1AF-58E9-B06E4A099373}",
"Global\\{224A23F9-3857-A1AF-CCEB-B06EDE0B9373}",
"Global\\{224A23F9-3857-A1AF-B4EC-B06EA60C9373}",
"Global\\{224A23F9-3857-A1AF-2CEA-B06E3E0A9373}",
"Global\\{224A23F9-3857-A1AF-9CE0-B06E8E009373}",
"Global\\{224A23F9-3857-A1AF-3CEB-B06E2E0B9373}",
"Global\\{224A23F9-3857-A1AF-D4EC-B06EC60C9373}",
"Global\\{224A23F9-3857-A1AF-50EB-B06E420B9373}",
"Global\\{224A23F9-3857-A1AF-80EB-B06E920B9373}",
"Global\\{224A23F9-3857-A1AF-78E8-B06E6A089373}",
"Global\\{224A23F9-3857-A1AF-0CE9-B06E1E099373}",
"Global\\{73B5150B-0EA5-F050-A920-6470BBC0476D}",
"Global\\{224A23F9-3857-A1AF-94EC-B06E860C9373}",
"Global\\{224A23F9-3857-A1AF-C0E9-B06ED2099373}",
"Global\\{224A23F9-3857-A1AF-8CEC-B06E9E0C9373}",
"Global\\{224A23F9-3857-A1AF-28E0-B06E3A009373}",
"Global\\{224A23F9-3857-A1AF-A8EB-B06EBA0B9373}",
"Global\\{C3671720-0C8E-4082-A920-6470BBC0476D}",
"Global\\{224A23F9-3857-A1AF-0CEF-B06E1E0F9373}",
"Global\\{224A23F9-3857-A1AF-E8EE-B06EFA0E9373}",
"Global\\{224A23F9-3857-A1AF-0CE3-B06E1E039373}",
"Global\\{224A23F9-3857-A1AF-24EC-B06E360C9373}",
"Global\\{224A23F9-3857-A1AF-34ED-B06E260D9373}",
"Global\\{224A23F9-3857-A1AF-D0E1-B06EC2019373}",
"Global\\{224A23F9-3857-A1AF-C0EC-B06ED20C9373}",
"Global\\{224A23F9-3857-A1AF-70EC-B06E620C9373}",
"Global\\{224A23F9-3857-A1AF-C8EB-B06EDA0B9373}",
"Global\\{224A23F9-3857-A1AF-68ED-B06E7A0D9373}",
"Global\\{A95FF40A-EFA4-2ABA-A920-6470BBC0476D}",
"Local\\{E91F2729-3C87-6AFA-A920-6470BBC0476D}",
"Global\\{224A23F9-3857-A1AF-D4EA-B06EC60A9373}",
"Global\\{224A23F9-3857-A1AF-50E2-B06E42029373}",
"Global\\{224A23F9-3857-A1AF-14EE-B06E060E9373}",
"Global\\{A95FF40D-EFA3-2ABA-A920-6470BBC0476D}",
"Local\\{C8B94218-59B6-4B5C-A920-6470BBC0476D}",
"Global\\{224A23F9-3857-A1AF-14EC-B06E060C9373}",
"Global\\{224A23F9-3857-A1AF-FCEB-B06EEE0B9373}"
],
"file_failed": [
"C:\\cuckoo_1768.ini",
"C:\\cuckoo_1636.ini",
"C:\\cuckoo_1700.ini",
"C:\\cuckoo_1788.ini",
"C:\\Users\\cuck\\AppData\\LocalLow\\uloj.wae.dat",
"C:\\cuckoo_1724.ini",
"C:\\cuckoo_1692.ini"
],
"guid": [
"{0ca545c6-37ad-4a6c-bf92-9f7610067ef5}",
"{f7898af5-cac4-4632-a2ec-da06e5111af2}",
"{e0483ba0-47ff-4d9c-a6d6-7741d0b195f7}",
"{304ce942-6e39-40d8-943a-b913c40c9cd4}"
],
"file_read": [
"C:\\Users\\cuck\\AppData\\Roaming\\Kidi\\vaegyv.exe",
"C:\\Users\\cuck\\AppData\\Local\\Temp\\a557fa363f1bce12c415a22d1d81905cc007e12bec6fb117f48275cf9b280e09.bin"
],
"regkey_read": [
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\PublishExpandedPath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\LocalizedName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Category",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Rpc\\MaxRpcSize",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\InfoTip",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Icon",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\PreCreate",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\StreamResourceType",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\ProfileList\\S-1-5-21-699399860-4089948139-3198924279-1001\\ProfileImagePath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Stream",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Security",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\RelativePath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Roamable",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\ParsingName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\RelativePath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Category",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\InfoTip",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\DisableImprovedZoneCheck",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Attributes",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\PreCreate",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\LocalizedName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\ParentFolder",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\InfoTip",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Security",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Stream",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\ge60cic",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\InstallDate",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\ParsingName",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\User Shell Folders\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}",
"HKEY_CURRENT_USER\\AppEvents\\Schemes\\Apps\\.Default\\Open\\.Current\\Default Flags",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Attributes",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\LocalRedirectOnly",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Run\\Vaegyv",
"HKEY_LOCAL_MACHINE\\SYSTEM\\ControlSet001\\services\\crypt32\\DebugHeapFlags",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\ParentFolder",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Name",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\FolderTypeID",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\PreCreate",
"HKEY_CURRENT_USER\\AppEvents\\Schemes\\Apps\\.Default\\Close\\.Current\\Default Flags",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Stream",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Rpc\\SecurityService\\DefaultAuthLevel",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\StreamResource",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\PublishExpandedPath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Roamable",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Category",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Category",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Attributes",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\FolderTypeID",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\LocalRedirectOnly",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\InfoTip",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\PublishExpandedPath",
"HKEY_CURRENT_USER\\AppEvents\\Schemes\\Apps\\.Default\\Open\\.Current\\(Default)",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\ParsingName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\ParentFolder",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Roamable",
"HKEY_LOCAL_MACHINE\\SYSTEM\\Setup\\SystemSetupInProgress",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\LocalRedirectOnly",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\StreamResource",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Description",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\InitFolderHandler",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\RelativePath",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\12864b4h",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\InitFolderHandler",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\FolderTypeID",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\84545h5",
"HKEY_LOCAL_MACHINE\\SYSTEM\\Setup\\OOBEInProgress",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Security",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\DigitalProductId",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\LocalizedName",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\21b6376b",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\LocalRedirectOnly",
"HKEY_CURRENT_USER\\AppEvents\\Schemes\\Apps\\.Default\\Close\\.Current\\(Default)",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\StreamResourceType",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\StreamResource",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Security",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\LocalizedName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Name",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Icon",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\RelativePath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Name",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\ParsingName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Icon",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Policies\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Security_HKLM_only",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\StreamResource",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\PublishExpandedPath",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\id7d6b3",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\FolderTypeID",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Stream",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Description",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Icon",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\GRE_Initialize\\DisableMetaFiles",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\1gbabd40",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Description",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\StreamResourceType",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\InitFolderHandler",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\StreamResourceType",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\SQMClient\\Windows\\CEIPEnable",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\User Shell Folders\\AppData",
"HKEY_LOCAL_MACHINE\\SYSTEM\\ControlSet001\\Control\\ComputerName\\ActiveComputerName\\ComputerName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Name",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\PreCreate",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Description",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\bi76c7e",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\d8c0g05",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Roamable",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\ParentFolder",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\1gf413bh",
"HKEY_CURRENT_USER\\AppEvents\\Schemes\\(Default)",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Attributes",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\InitFolderHandler"
],
"directory_enumerated": [
"C:\\Users\\cuck\\AppData\\LocalLow\\*.90121382"
],
"directory_created": [
"C:\\Users\\cuck\\AppData\\Roaming\\Kidi"
]
}Dropped
[
{
"yara": [],
"sha1": "7f3ace8e90dc1d21281c54c5cff542af5e94ab84",
"name": "ba8262cbc018a755_vaegyv.exe",
"filepath": "C:\\Users\\cuck\\AppData\\Roaming\\Kidi\\vaegyv.exe",
"type": "PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows",
"sha256": "ba8262cbc018a755b8119d84f8eeedd58b14d9f5da05b1ab4a57cadec845cb7b",
"urls": [],
"crc32": "231D8C11",
"path": "\/home\/hpuser\/.cuckoo\/storage\/analyses\/1190\/files\/ba8262cbc018a755_vaegyv.exe",
"ssdeep": null,
"size": 320512,
"sha512": "fce8a0f9700f1ebec624394fbeac7eb4f41b3a6782dbd532132d355acc047829425503795824bda72f5c2d18533a9b9551077287b6552be113edd0ac5feff208",
"pids": [
2740
],
"md5": "6b6551ede0af775d9e8d19db8e99cbd6"
}
]Generic
[
{
"process_path": "C:\\Windows\\System32\\cmd.exe",
"process_name": "cmd.exe",
"pid": 1692,
"summary": {},
"first_seen": 1563691997.859,
"ppid": 1788
},
{
"process_path": "C:\\Windows\\System32\\taskhost.exe",
"process_name": "taskhost.exe",
"pid": 1724,
"summary": {
"regkey_read": [
"HKEY_CURRENT_USER\\AppEvents\\Schemes\\(Default)",
"HKEY_CURRENT_USER\\AppEvents\\Schemes\\Apps\\.Default\\Close\\.Current\\Default Flags",
"HKEY_CURRENT_USER\\AppEvents\\Schemes\\Apps\\.Default\\Close\\.Current\\(Default)",
"HKEY_CURRENT_USER\\AppEvents\\Schemes\\Apps\\.Default\\Open\\.Current\\(Default)",
"HKEY_CURRENT_USER\\AppEvents\\Schemes\\Apps\\.Default\\Open\\.Current\\Default Flags"
],
"regkey_deleted": [
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Run\\internat.exe"
]
},
"first_seen": 1563691996.7028,
"ppid": 468
},
{
"process_path": "C:\\Windows\\System32\\mobsync.exe",
"process_name": "mobsync.exe",
"pid": 1636,
"summary": {},
"first_seen": 1563691998.6402,
"ppid": 592
},
{
"process_path": "C:\\Windows\\System32\\dwm.exe",
"process_name": "dwm.exe",
"pid": 1768,
"summary": {},
"first_seen": 1563691997.3121,
"ppid": 804
},
{
"process_path": "C:\\Windows\\explorer.exe",
"process_name": "explorer.exe",
"pid": 1788,
"summary": {
"file_opened": [
"C:\\"
],
"file_exists": [
"C:\\cuckoo_1768.ini",
"C:\\cuckoo_1636.ini",
"C:\\cuckoo_1700.ini",
"C:\\cuckoo_1788.ini",
"C:\\cuckoo_1724.ini",
"C:\\cuckoo_1692.ini",
"C:\\cuckoo_1820.ini"
],
"file_failed": [
"C:\\cuckoo_1768.ini",
"C:\\cuckoo_1636.ini",
"C:\\cuckoo_1700.ini",
"C:\\cuckoo_1788.ini",
"C:\\cuckoo_1724.ini",
"C:\\cuckoo_1692.ini"
]
},
"first_seen": 1563691997.5465,
"ppid": 1740
},
{
"process_path": "C:\\Windows\\System32\\lsass.exe",
"process_name": "lsass.exe",
"pid": 476,
"summary": {},
"first_seen": 1563691985.3281,
"ppid": 376
},
{
"process_path": "C:\\Users\\cuck\\AppData\\Local\\Temp\\a557fa363f1bce12c415a22d1d81905cc007e12bec6fb117f48275cf9b280e09.bin",
"process_name": "a557fa363f1bce12c415a22d1d81905cc007e12bec6fb117f48275cf9b280e09.bin",
"pid": 2740,
"summary": {
"file_created": [
"C:\\Users\\cuck\\AppData\\LocalLow\\uloj.wae",
"C:\\Users\\cuck\\AppData\\Roaming\\Kidi\\vaegyv.exe",
"C:\\Users\\cuck\\AppData\\Local\\Temp\\FHF2E01.bat"
],
"directory_created": [
"C:\\Users\\cuck\\AppData\\Roaming\\Kidi"
],
"dll_loaded": [
"ntdll.dll",
"WS2_32.dll",
"API-MS-Win-Security-SDDL-L1-1-0.dll",
"profapi.dll",
"IPHLPAPI.DLL",
"WININET.dll",
"CRYPT32.dll",
"ADVAPI32.dll",
"KERNEL32.dll",
"msvcrt.dll",
"Secur32.dll",
"GDI32.dll",
"NETAPI32.dll",
"VERSION.dll",
"SHELL32.dll",
"rpcrt4.dll",
"ole32.dll",
"SHLWAPI.dll",
"CRYPTSP.dll",
"USER32.dll",
"OLEAUT32.dll"
],
"file_opened": [
"C:\\Users\\cuck\\AppData\\Roaming\\Kidi",
"C:\\Users\\cuck\\AppData\\Roaming\\Kidi\\vaegyv.exe",
"C:\\Users\\cuck\\AppData\\LocalLow",
"C:\\Users\\cuck\\AppData\\Local\\Temp\\a557fa363f1bce12c415a22d1d81905cc007e12bec6fb117f48275cf9b280e09.bin",
"C:\\Users\\cuck\\AppData\\Roaming"
],
"regkey_opened": [
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows NT\\CurrentVersion",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\User Shell Folders",
"HKEY_LOCAL_MACHINE\\Software\\Policies\\Microsoft\\Windows NT\\Rpc",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\KnownFolderSettings",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\FolderDescriptions",
"HKEY_LOCAL_MACHINE\\Software\\Policies\\Microsoft\\Windows\\CurrentVersion\\Internet Settings",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\PropertyBag",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings",
"HKEY_LOCAL_MACHINE\\SYSTEM\\CurrentControlSet\\Services\\crypt32",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\PropertyBag",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Rpc",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows NT\\CurrentVersion\\ProfileList\\S-1-5-21-699399860-4089948139-3198924279-1001",
"HKEY_CURRENT_USER\\Software\\Microsoft",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\SessionInfo\\1\\KnownFolders",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\PropertyBag",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\PropertyBag",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\SessionInfo\\1"
],
"file_written": [
"C:\\Users\\cuck\\AppData\\Roaming\\Kidi\\vaegyv.exe",
"C:\\Users\\cuck\\AppData\\Local\\Temp\\FHF2E01.bat"
],
"file_exists": [
"C:\\Users\\cuck\\AppData\\Roaming\\Kidi\\vaegyv.exe",
"C:\\Users\\cuck\\AppData\\Roaming",
"C:\\Windows",
"C:\\Users\\cuck\\AppData\\LocalLow"
],
"mutex": [
"Global\\{224A23F9-3857-A1AF-34ED-B06E260D9373}",
"Global\\{56060262-19CC-D5E3-A920-6470BBC0476D}",
"Global\\{C3671720-0C8E-4082-A920-6470BBC0476D}"
],
"file_failed": [
"C:\\Users\\cuck\\AppData\\LocalLow\\uloj.wae.dat"
],
"command_line": [
"\"C:\\Users\\cuck\\AppData\\Roaming\\Kidi\\vaegyv.exe\"",
"\"C:\\Windows\\system32\\cmd.exe\" \/c \"C:\\Users\\cuck\\AppData\\Local\\Temp\\FHF2E01.bat\""
],
"file_read": [
"C:\\Users\\cuck\\AppData\\Local\\Temp\\a557fa363f1bce12c415a22d1d81905cc007e12bec6fb117f48275cf9b280e09.bin"
],
"regkey_read": [
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\PublishExpandedPath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\LocalizedName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Category",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Rpc\\MaxRpcSize",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\InfoTip",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Icon",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\PreCreate",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\StreamResourceType",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\ProfileList\\S-1-5-21-699399860-4089948139-3198924279-1001\\ProfileImagePath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Stream",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Security",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\RelativePath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Roamable",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\ParsingName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\RelativePath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Category",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\InfoTip",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\DisableImprovedZoneCheck",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Attributes",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\PreCreate",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\LocalizedName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\ParentFolder",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\InfoTip",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Security",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Stream",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\ge60cic",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\InstallDate",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\ParsingName",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\User Shell Folders\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Attributes",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\LocalRedirectOnly",
"HKEY_LOCAL_MACHINE\\SYSTEM\\ControlSet001\\services\\crypt32\\DebugHeapFlags",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\ParentFolder",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Name",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\FolderTypeID",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\PreCreate",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Stream",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\StreamResource",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\PublishExpandedPath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Roamable",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Category",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Category",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Attributes",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\FolderTypeID",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\LocalRedirectOnly",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\InfoTip",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\PublishExpandedPath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\ParsingName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\ParentFolder",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Roamable",
"HKEY_LOCAL_MACHINE\\SYSTEM\\Setup\\SystemSetupInProgress",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\LocalRedirectOnly",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\StreamResource",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Description",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\InitFolderHandler",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\RelativePath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\InitFolderHandler",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\FolderTypeID",
"HKEY_LOCAL_MACHINE\\SYSTEM\\Setup\\OOBEInProgress",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Security",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\DigitalProductId",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\LocalizedName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\LocalRedirectOnly",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\StreamResourceType",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\StreamResource",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Security",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\LocalizedName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Name",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Icon",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\RelativePath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Name",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\ParsingName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Icon",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Policies\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Security_HKLM_only",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\StreamResource",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\PublishExpandedPath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\FolderTypeID",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Stream",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Description",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Icon",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\GRE_Initialize\\DisableMetaFiles",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Description",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\StreamResourceType",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\InitFolderHandler",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\StreamResourceType",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\SQMClient\\Windows\\CEIPEnable",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\User Shell Folders\\AppData",
"HKEY_LOCAL_MACHINE\\SYSTEM\\ControlSet001\\Control\\ComputerName\\ActiveComputerName\\ComputerName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Name",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\PreCreate",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Description",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Roamable",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\ParentFolder",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Attributes",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\InitFolderHandler"
],
"regkey_written": [
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\ge60cic"
]
},
"first_seen": 1563691985.6406,
"ppid": 1664
},
{
"process_path": "C:\\Windows\\System32\\conhost.exe",
"process_name": "conhost.exe",
"pid": 1700,
"summary": {},
"first_seen": 1563691998.4059,
"ppid": 384
},
{
"process_path": "C:\\Users\\cuck\\AppData\\Roaming\\Kidi\\vaegyv.exe",
"process_name": "vaegyv.exe",
"pid": 2204,
"summary": {
"regkey_written": [
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\bi76c7e",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\1gbabd40",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Run\\Vaegyv"
],
"dll_loaded": [
"API-MS-Win-Security-SDDL-L1-1-0.dll",
"profapi.dll",
"IPHLPAPI.DLL",
"WININET.dll",
"CRYPT32.dll",
"ADVAPI32.dll",
"Secur32.dll",
"NETAPI32.dll",
"VERSION.dll",
"SHELL32.dll",
"rpcrt4.dll",
"ole32.dll",
"CRYPTSP.dll"
],
"file_opened": [
"C:\\Users\\cuck\\AppData\\Roaming\\Kidi\\vaegyv.exe"
],
"regkey_opened": [
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\User Shell Folders",
"HKEY_LOCAL_MACHINE\\Software\\Policies\\Microsoft\\Windows NT\\Rpc",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\KnownFolderSettings",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\FolderDescriptions",
"HKEY_LOCAL_MACHINE\\Software\\Policies\\Microsoft\\Windows\\CurrentVersion\\Internet Settings",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\PropertyBag",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Run",
"HKEY_LOCAL_MACHINE\\SYSTEM\\CurrentControlSet\\Services\\crypt32",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\PropertyBag",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Rpc",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows NT\\CurrentVersion\\ProfileList\\S-1-5-21-699399860-4089948139-3198924279-1001",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\SessionInfo\\1\\KnownFolders",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\PropertyBag",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\PropertyBag",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Rpc\\SecurityService",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\SessionInfo\\1"
],
"file_exists": [
"C:\\Users\\cuck\\AppData\\Roaming",
"C:\\Windows",
"C:\\Users\\cuck\\AppData\\LocalLow"
],
"mutex": [
"Global\\{224A23F9-3857-A1AF-E8E1-B06EFA019373}",
"Global\\{224A23F9-3857-A1AF-70E3-B06E62039373}",
"Global\\{224A23F9-3857-A1AF-BCE8-B06EAE089373}",
"Global\\{224A23F9-3857-A1AF-60EB-B06E720B9373}",
"Local\\{C8B94219-59B7-4B5C-A920-6470BBC0476D}",
"Global\\{224A23F9-3857-A1AF-4CEC-B06E5E0C9373}",
"Global\\{224A23F9-3857-A1AF-E0E8-B06EF2089373}",
"Global\\{A5B32338-3896-2656-A920-6470BBC0476D}",
"Global\\{224A23F9-3857-A1AF-F4EB-B06EE60B9373}",
"Global\\{224A23F9-3857-A1AF-48EE-B06E5A0E9373}",
"Global\\{224A23F9-3857-A1AF-58E9-B06E4A099373}",
"Global\\{224A23F9-3857-A1AF-CCEB-B06EDE0B9373}",
"Global\\{224A23F9-3857-A1AF-B4EC-B06EA60C9373}",
"Global\\{224A23F9-3857-A1AF-2CEA-B06E3E0A9373}",
"Global\\{224A23F9-3857-A1AF-9CE0-B06E8E009373}",
"Global\\{224A23F9-3857-A1AF-3CEB-B06E2E0B9373}",
"Global\\{224A23F9-3857-A1AF-D4EC-B06EC60C9373}",
"Global\\{224A23F9-3857-A1AF-50EB-B06E420B9373}",
"Global\\{224A23F9-3857-A1AF-80EB-B06E920B9373}",
"Global\\{224A23F9-3857-A1AF-78E8-B06E6A089373}",
"Global\\{224A23F9-3857-A1AF-0CE9-B06E1E099373}",
"Global\\{73B5150B-0EA5-F050-A920-6470BBC0476D}",
"Global\\{224A23F9-3857-A1AF-94EC-B06E860C9373}",
"Global\\{224A23F9-3857-A1AF-C0E9-B06ED2099373}",
"Global\\{224A23F9-3857-A1AF-8CEC-B06E9E0C9373}",
"Global\\{224A23F9-3857-A1AF-28E0-B06E3A009373}",
"Global\\{224A23F9-3857-A1AF-A8EB-B06EBA0B9373}",
"Global\\{224A23F9-3857-A1AF-0CEF-B06E1E0F9373}",
"Global\\{224A23F9-3857-A1AF-E8EE-B06EFA0E9373}",
"Global\\{224A23F9-3857-A1AF-0CE3-B06E1E039373}",
"Global\\{224A23F9-3857-A1AF-24EC-B06E360C9373}",
"Global\\{224A23F9-3857-A1AF-D0E1-B06EC2019373}",
"Global\\{224A23F9-3857-A1AF-C0EC-B06ED20C9373}",
"Global\\{224A23F9-3857-A1AF-70EC-B06E620C9373}",
"Global\\{224A23F9-3857-A1AF-C8EB-B06EDA0B9373}",
"Global\\{224A23F9-3857-A1AF-68ED-B06E7A0D9373}",
"Global\\{A95FF40A-EFA4-2ABA-A920-6470BBC0476D}",
"Local\\{E91F2729-3C87-6AFA-A920-6470BBC0476D}",
"Global\\{224A23F9-3857-A1AF-D4EA-B06EC60A9373}",
"Global\\{224A23F9-3857-A1AF-50E2-B06E42029373}",
"Global\\{224A23F9-3857-A1AF-14EE-B06E060E9373}",
"Global\\{A95FF40D-EFA3-2ABA-A920-6470BBC0476D}",
"Local\\{C8B94218-59B6-4B5C-A920-6470BBC0476D}",
"Global\\{224A23F9-3857-A1AF-14EC-B06E060C9373}",
"Global\\{224A23F9-3857-A1AF-FCEB-B06EEE0B9373}"
],
"guid": [
"{0ca545c6-37ad-4a6c-bf92-9f7610067ef5}",
"{f7898af5-cac4-4632-a2ec-da06e5111af2}",
"{e0483ba0-47ff-4d9c-a6d6-7741d0b195f7}",
"{304ce942-6e39-40d8-943a-b913c40c9cd4}"
],
"file_read": [
"C:\\Users\\cuck\\AppData\\Roaming\\Kidi\\vaegyv.exe"
],
"regkey_read": [
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\PublishExpandedPath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\LocalizedName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Category",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Rpc\\MaxRpcSize",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\InfoTip",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Icon",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\PreCreate",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\StreamResourceType",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\ProfileList\\S-1-5-21-699399860-4089948139-3198924279-1001\\ProfileImagePath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Stream",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Security",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\RelativePath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Roamable",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\ParsingName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\RelativePath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Category",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\InfoTip",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\DisableImprovedZoneCheck",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Attributes",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\PreCreate",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\LocalizedName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\ParentFolder",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\InfoTip",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Security",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Stream",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\ge60cic",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\ParsingName",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\User Shell Folders\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Attributes",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\LocalRedirectOnly",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Run\\Vaegyv",
"HKEY_LOCAL_MACHINE\\SYSTEM\\ControlSet001\\services\\crypt32\\DebugHeapFlags",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\ParentFolder",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Name",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\FolderTypeID",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\PreCreate",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Stream",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Rpc\\SecurityService\\DefaultAuthLevel",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\StreamResource",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\PublishExpandedPath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Roamable",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Category",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Category",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Attributes",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\FolderTypeID",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\LocalRedirectOnly",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\InfoTip",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\PublishExpandedPath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\ParsingName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\ParentFolder",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Roamable",
"HKEY_LOCAL_MACHINE\\SYSTEM\\Setup\\SystemSetupInProgress",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\LocalRedirectOnly",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\StreamResource",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Description",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\InitFolderHandler",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\RelativePath",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\12864b4h",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\InitFolderHandler",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\FolderTypeID",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\84545h5",
"HKEY_LOCAL_MACHINE\\SYSTEM\\Setup\\OOBEInProgress",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Security",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\LocalizedName",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\21b6376b",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\LocalRedirectOnly",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\StreamResourceType",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\StreamResource",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Security",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\LocalizedName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Name",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Icon",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\RelativePath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Name",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\ParsingName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Icon",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Policies\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Security_HKLM_only",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\StreamResource",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\PublishExpandedPath",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\id7d6b3",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\FolderTypeID",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Stream",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Description",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Icon",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\1gbabd40",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Description",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\StreamResourceType",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\InitFolderHandler",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\StreamResourceType",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\SQMClient\\Windows\\CEIPEnable",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\User Shell Folders\\AppData",
"HKEY_LOCAL_MACHINE\\SYSTEM\\ControlSet001\\Control\\ComputerName\\ActiveComputerName\\ComputerName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\Name",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\PreCreate",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{F38BF404-1D43-42F2-9305-67DE0B28FC23}\\Description",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\bi76c7e",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\d8c0g05",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{3EB685DB-65F9-4CF6-A03A-E3EF65729F3D}\\Roamable",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\ParentFolder",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Ixxiziviulmi\\1gf413bh",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{5E6C858F-0E22-4760-9AFE-EA3317B67173}\\Attributes",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\explorer\\FolderDescriptions\\{A520A1A4-1780-4FF6-BD18-167343C5AF16}\\InitFolderHandler"
],
"directory_enumerated": [
"C:\\Users\\cuck\\AppData\\LocalLow\\*.90121382"
]
},
"first_seen": 1563691990.9528,
"ppid": 2740
}
]Signatures
[
{
"markcount": 1,
"families": [],
"description": "Queries for the computername",
"severity": 1,
"marks": [
{
"call": {
"category": "misc",
"status": 1,
"stacktrace": [],
"api": "GetComputerNameW",
"return_value": 1,
"arguments": {
"computer_name": "CUCKPC"
},
"time": 1563691990.8276,
"tid": 2436,
"flags": {}
},
"pid": 2740,
"type": "call",
"cid": 651
}
],
"references": [],
"name": "antivm_queries_computername"
},
{
"markcount": 2,
"families": [],
"description": "Collects information to fingerprint the system (MachineGuid, DigitalProductId, SystemBiosDate)",
"severity": 1,
"marks": [
{
"category": "registry",
"ioc": "HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\DigitalProductId",
"type": "ioc",
"description": null
},
{
"category": "registry",
"ioc": "HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\InstallDate",
"type": "ioc",
"description": null
}
],
"references": [],
"name": "recon_fingerprint"
},
{
"markcount": 1,
"families": [],
"description": "Checks amount of memory in system, this can be used to detect virtual machines that have a low amount of memory available",
"severity": 1,
"marks": [
{
"call": {
"category": "system",
"status": 1,
"stacktrace": [],
"api": "GlobalMemoryStatusEx",
"return_value": 1,
"arguments": {},
"time": 1563691990.7966,
"tid": 2436,
"flags": {}
},
"pid": 2740,
"type": "call",
"cid": 461
}
],
"references": [],
"name": "antivm_memory_available"
},
{
"markcount": 2,
"families": [],
"description": "The executable contains unknown PE section names indicative of a packer (could be a false positive)",
"severity": 1,
"marks": [
{
"category": "section",
"ioc": ".ndata",
"type": "ioc",
"description": null
},
{
"category": "section",
"ioc": ".qdata",
"type": "ioc",
"description": null
}
],
"references": [],
"name": "pe_features"
},
{
"markcount": 1,
"families": [],
"description": "One or more processes crashed",
"severity": 1,
"marks": [
{
"call": {
"category": "__notification__",
"status": 1,
"stacktrace": [],
"raw": [
"stacktrace"
],
"api": "__exception__",
"return_value": 0,
"arguments": {
"stacktrace": "R\na\ni\ns\ne\nE\nx\nc\ne\np\nt\ni\no\nn\n+\n0\nx\n3\nd\n \nF\nr\ne\ne\nE\nn\nv\ni\nr\no\nn\nm\ne\nn\nt\nS\nt\nr\ni\nn\ng\ns\nW\n-\n0\nx\n3\n7\n3\n \nk\ne\nr\nn\ne\nl\nb\na\ns\ne\n+\n0\nx\na\n4\n9\nd\n \n@\n \n0\nx\n7\nf\ne\nf\nd\na\n1\na\n4\n9\nd\n\n\nR\np\nc\nR\na\ni\ns\ne\nE\nx\nc\ne\np\nt\ni\no\nn\n+\n0\nx\n5\n3\n \nR\np\nc\nE\nx\nc\ne\np\nt\ni\no\nn\nF\ni\nl\nt\ne\nr\n-\n0\nx\n2\nb\nd\n \nr\np\nc\nr\nt\n4\n+\n0\nx\n1\n7\n3\nc\n3\n \n@\n \n0\nx\n7\nf\ne\nf\ne\ne\nf\n7\n3\nc\n3\n\n\nC\no\nG\ne\nt\nI\nn\ns\nt\na\nn\nc\ne\nF\nr\no\nm\nF\ni\nl\ne\n+\n0\nx\na\n7\n0\na\n \nH\nA\nC\nC\nE\nL\n_\nU\ns\ne\nr\nF\nr\ne\ne\n-\n0\nx\n1\n6\nc\n6\n \no\nl\ne\n3\n2\n+\n0\nx\n1\n7\n6\n2\nb\na\n \n@\n \n0\nx\n7\nf\ne\nf\nf\nb\n6\n6\n2\nb\na\n\n\nN\nd\nr\n6\n4\nA\ns\ny\nn\nc\nS\ne\nr\nv\ne\nr\nC\na\nl\nl\nA\nl\nl\n+\n0\nx\n1\n4\nc\n9\n \nN\nd\nr\n6\n4\nA\ns\ny\nn\nc\nC\nl\ni\ne\nn\nt\nC\na\nl\nl\n-\n0\nx\n5\n1\n7\n \nr\np\nc\nr\nt\n4\n+\n0\nx\nd\nb\n9\n4\n9\n \n@\n \n0\nx\n7\nf\ne\nf\ne\nf\nb\nb\n9\n4\n9\n\n\nC\no\nG\ne\nt\nI\nn\ns\nt\na\nn\nc\ne\nF\nr\no\nm\nF\ni\nl\ne\n+\n0\nx\n6\n6\n2\n0\n \nH\nA\nC\nC\nE\nL\n_\nU\ns\ne\nr\nF\nr\ne\ne\n-\n0\nx\n5\n7\nb\n0\n \no\nl\ne\n3\n2\n+\n0\nx\n1\n7\n2\n1\nd\n0\n \n@\n \n0\nx\n7\nf\ne\nf\nf\nb\n6\n2\n1\nd\n0\n\n\nD\nc\no\nm\nC\nh\na\nn\nn\ne\nl\nS\ne\nt\nH\nR\ne\ns\nu\nl\nt\n+\n0\nx\n3\n0\n6\n6\n \nO\nb\nj\ne\nc\nt\nS\nt\nu\nb\nl\ne\ns\ns\nC\nl\ni\ne\nn\nt\n3\n-\n0\nx\n7\ne\ne\n \no\nl\ne\n3\n2\n+\n0\nx\n2\nd\n8\na\n2\n \n@\n \n0\nx\n7\nf\ne\nf\nf\na\n1\nd\n8\na\n2\n\n\nO\nb\nj\ne\nc\nt\nS\nt\nu\nb\nl\ne\ns\ns\nC\nl\ni\ne\nn\nt\n5\n+\n0\nx\n1\n8\n3\n \nI\ns\nV\na\nl\ni\nd\nI\nn\nt\ne\nr\nf\na\nc\ne\n-\n0\nx\n1\n0\n5\nd\n \no\nl\ne\n3\n2\n+\n0\nx\n3\n1\nb\nb\n3\n \n@\n \n0\nx\n7\nf\ne\nf\nf\na\n2\n1\nb\nb\n3\n\n\nO\nb\nj\ne\nc\nt\nS\nt\nu\nb\nl\ne\ns\ns\nC\nl\ni\ne\nn\nt\n5\n+\n0\nx\nf\n2\n \nI\ns\nV\na\nl\ni\nd\nI\nn\nt\ne\nr\nf\na\nc\ne\n-\n0\nx\n1\n0\ne\ne\n \no\nl\ne\n3\n2\n+\n0\nx\n3\n1\nb\n2\n2\n \n@\n \n0\nx\n7\nf\ne\nf\nf\na\n2\n1\nb\n2\n2\n\n\nC\no\nM\na\nr\ns\nh\na\nl\nI\nn\nt\ne\nr\nf\na\nc\ne\n+\n0\nx\n2\n6\n3\nf\n \nO\nb\nj\ne\nc\nt\nS\nt\nu\nb\nl\ne\ns\ns\nC\nl\ni\ne\nn\nt\n5\n-\n0\nx\n2\n4\n5\n \no\nl\ne\n3\n2\n+\n0\nx\n3\n1\n7\ne\nb\n \n@\n \n0\nx\n7\nf\ne\nf\nf\na\n2\n1\n7\ne\nb\n\n\nC\no\nM\na\nr\ns\nh\na\nl\nI\nn\nt\ne\nr\nf\na\nc\ne\n+\n0\nx\n2\n2\n6\nb\n \nO\nb\nj\ne\nc\nt\nS\nt\nu\nb\nl\ne\ns\ns\nC\nl\ni\ne\nn\nt\n5\n-\n0\nx\n6\n1\n9\n \no\nl\ne\n3\n2\n+\n0\nx\n3\n1\n4\n1\n7\n \n@\n \n0\nx\n7\nf\ne\nf\nf\na\n2\n1\n4\n1\n7\n\n\nC\no\nS\ne\nt\nS\nt\na\nt\ne\n+\n0\nx\n4\n5\na\n \nD\nc\no\nm\nC\nh\na\nn\nn\ne\nl\nS\ne\nt\nH\nR\ne\ns\nu\nl\nt\n-\n0\nx\n1\n3\n4\n2\n \no\nl\ne\n3\n2\n+\n0\nx\n2\n9\n4\nf\na\n \n@\n \n0\nx\n7\nf\ne\nf\nf\na\n1\n9\n4\nf\na\n\n\nC\no\nS\ne\nt\nS\nt\na\nt\ne\n+\n0\nx\n3\n8\n8\n \nD\nc\no\nm\nC\nh\na\nn\nn\ne\nl\nS\ne\nt\nH\nR\ne\ns\nu\nl\nt\n-\n0\nx\n1\n4\n1\n4\n \no\nl\ne\n3\n2\n+\n0\nx\n2\n9\n4\n2\n8\n \n@\n \n0\nx\n7\nf\ne\nf\nf\na\n1\n9\n4\n2\n8\n\n\nC\no\nS\ne\nt\nS\nt\na\nt\ne\n+\n0\nx\na\na\n9\n \nD\nc\no\nm\nC\nh\na\nn\nn\ne\nl\nS\ne\nt\nH\nR\ne\ns\nu\nl\nt\n-\n0\nx\nc\nf\n3\n \no\nl\ne\n3\n2\n+\n0\nx\n2\n9\nb\n4\n9\n \n@\n \n0\nx\n7\nf\ne\nf\nf\na\n1\n9\nb\n4\n9\n\n\nC\no\nR\ne\ng\ni\ns\nt\ne\nr\nM\ne\ns\ns\na\ng\ne\nF\ni\nl\nt\ne\nr\n+\n0\nx\n1\n5\n3\nb\n \nC\no\nU\nn\ni\nn\ni\nt\ni\na\nl\ni\nz\ne\n-\n0\nx\n3\n3\n4\n1\n \no\nl\ne\n3\n2\n+\n0\nx\n1\nd\nf\nd\n3\n \n@\n \n0\nx\n7\nf\ne\nf\nf\na\n0\nd\nf\nd\n3\n\n\nC\no\nR\ne\ng\ni\ns\nt\ne\nr\nM\ne\ns\ns\na\ng\ne\nF\ni\nl\nt\ne\nr\n+\n0\nx\n1\n1\nc\n0\n \nC\no\nU\nn\ni\nn\ni\nt\ni\na\nl\ni\nz\ne\n-\n0\nx\n3\n6\nb\nc\n \no\nl\ne\n3\n2\n+\n0\nx\n1\nd\nc\n5\n8\n \n@\n \n0\nx\n7\nf\ne\nf\nf\na\n0\nd\nc\n5\n8\n\n\nC\no\nR\ne\ng\ni\ns\nt\ne\nr\nM\ne\ns\ns\na\ng\ne\nF\ni\nl\nt\ne\nr\n+\n0\nx\nb\n9\n7\n \nC\no\nU\nn\ni\nn\ni\nt\ni\na\nl\ni\nz\ne\n-\n0\nx\n3\nc\ne\n5\n \no\nl\ne\n3\n2\n+\n0\nx\n1\nd\n6\n2\nf\n \n@\n \n0\nx\n7\nf\ne\nf\nf\na\n0\nd\n6\n2\nf\n\n\nC\no\nR\ne\ng\ni\ns\nt\ne\nr\nM\ne\ns\ns\na\ng\ne\nF\ni\nl\nt\ne\nr\n+\n0\nx\n1\n3\nf\ne\n \nC\no\nU\nn\ni\nn\ni\nt\ni\na\nl\ni\nz\ne\n-\n0\nx\n3\n4\n7\ne\n \no\nl\ne\n3\n2\n+\n0\nx\n1\nd\ne\n9\n6\n \n@\n \n0\nx\n7\nf\ne\nf\nf\na\n0\nd\ne\n9\n6\n\n\nO\nb\nj\ne\nc\nt\nS\nt\nu\nb\nl\ne\ns\ns\nC\nl\ni\ne\nn\nt\n3\n2\n+\n0\nx\n7\n3\nc\n2\n \nC\no\nD\ni\ns\nc\no\nn\nn\ne\nc\nt\nC\no\nn\nt\ne\nx\nt\n-\n0\nx\n9\nc\nb\n6\n \no\nl\ne\n3\n2\n+\n0\nx\n4\na\ne\nc\n2\n \n@\n \n0\nx\n7\nf\ne\nf\nf\na\n3\na\ne\nc\n2\n\n\nC\no\nU\nn\ni\nn\ni\nt\ni\na\nl\ni\nz\ne\n+\n0\nx\n1\n0\n1\n0\n \nC\no\nI\nn\ni\nt\ni\na\nl\ni\nz\ne\nE\nx\n-\n0\nx\n7\n0\nc\n \no\nl\ne\n3\n2\n+\n0\nx\n2\n2\n3\n2\n4\n \n@\n \n0\nx\n7\nf\ne\nf\nf\na\n1\n2\n3\n2\n4\n\n\nC\no\nR\ne\ng\ni\ns\nt\ne\nr\nM\ne\ns\ns\na\ng\ne\nF\ni\nl\nt\ne\nr\n+\n0\nx\n3\nc\n3\n0\n \nC\no\nU\nn\ni\nn\ni\nt\ni\na\nl\ni\nz\ne\n-\n0\nx\nc\n4\nc\n \no\nl\ne\n3\n2\n+\n0\nx\n2\n0\n6\nc\n8\n \n@\n \n0\nx\n7\nf\ne\nf\nf\na\n1\n0\n6\nc\n8\n\n\nC\no\nR\ne\ng\ni\ns\nt\ne\nr\nM\ne\ns\ns\na\ng\ne\nF\ni\nl\nt\ne\nr\n+\n0\nx\n3\nc\n0\n1\n \nC\no\nU\nn\ni\nn\ni\nt\ni\na\nl\ni\nz\ne\n-\n0\nx\nc\n7\nb\n \no\nl\ne\n3\n2\n+\n0\nx\n2\n0\n6\n9\n9\n \n@\n \n0\nx\n7\nf\ne\nf\nf\na\n1\n0\n6\n9\n9\n\n\nC\no\nD\ni\ns\na\nb\nl\ne\nC\na\nl\nl\nC\na\nn\nc\ne\nl\nl\na\nt\ni\no\nn\n+\n0\nx\n3\nf\nc\n \nO\nb\nj\ne\nc\nt\nS\nt\nu\nb\nl\ne\ns\ns\nC\nl\ni\ne\nn\nt\n2\n4\n-\n0\nx\ne\n4\n \no\nl\ne\n3\n2\n+\n0\nx\ne\n7\na\nc\n \n@\n \n0\nx\n7\nf\ne\nf\nf\n9\nf\ne\n7\na\nc\n\n\nC\no\nU\nn\ni\nn\ni\nt\ni\na\nl\ni\nz\ne\n+\n0\nx\na\n6\n \nC\no\nI\nn\ni\nt\ni\na\nl\ni\nz\ne\nE\nx\n-\n0\nx\n1\n6\n7\n6\n \no\nl\ne\n3\n2\n+\n0\nx\n2\n1\n3\nb\na\n \n@\n \n0\nx\n7\nf\ne\nf\nf\na\n1\n1\n3\nb\na\n\n\nN\ne\nw\n_\no\nl\ne\n3\n2\n_\nC\no\nU\nn\ni\nn\ni\nt\ni\na\nl\ni\nz\ne\n+\n0\nx\n5\n7\n \nN\ne\nw\n_\no\nl\ne\n3\n2\n_\nO\nl\ne\nC\no\nn\nv\ne\nr\nt\nO\nL\nE\nS\nT\nR\nE\nA\nM\nT\no\nI\nS\nt\no\nr\na\ng\ne\n-\n0\nx\n5\n3\n \n@\n \n0\nx\n6\n5\na\na\n7\n6\n1\ne\n\n\nm\no\nb\ns\ny\nn\nc\n+\n0\nx\n6\n8\n4\n0\n \n@\n \n0\nx\nf\nf\nd\n8\n6\n8\n4\n0\n\n\nm\no\nb\ns\ny\nn\nc\n+\n0\nx\n7\n0\na\ne\n \n@\n \n0\nx\nf\nf\nd\n8\n7\n0\na\ne\n\n\nB\na\ns\ne\nT\nh\nr\ne\na\nd\nI\nn\ni\nt\nT\nh\nu\nn\nk\n+\n0\nx\nd\n \nC\nr\ne\na\nt\ne\nT\nh\nr\ne\na\nd\n-\n0\nx\n5\n3\n \nk\ne\nr\nn\ne\nl\n3\n2\n+\n0\nx\n1\n6\n5\n2\nd\n \n@\n \n0\nx\n7\n7\n7\na\n6\n5\n2\nd\n\n\nR\nt\nl\nU\ns\ne\nr\nT\nh\nr\ne\na\nd\nS\nt\na\nr\nt\n+\n0\nx\n2\n1\n \ns\nt\nr\nc\nh\nr\n-\n0\nx\n3\nd\nf\n \nn\nt\nd\nl\nl\n+\n0\nx\n2\nc\n5\n2\n1\n \n@\n \n0\nx\n7\n7\n9\nd\nc\n5\n2\n1",
"registers": {
"r14": 0,
"r9": 0,
"rcx": 2548704,
"rsi": 0,
"r10": 0,
"rbx": 0,
"rdi": 0,
"r11": 2550464,
"r8": 0,
"rdx": 1,
"rbp": 0,
"r15": 0,
"r12": 0,
"rsp": 2555520,
"rax": 2011628644,
"r13": 0
},
"exception": {
"instruction_r": "48 81 c4 c8 00 00 00 c3 48 85 f6 74 08 83 3b 00",
"symbol": "RaiseException+0x3d FreeEnvironmentStringsW-0x373 kernelbase+0xa49d",
"instruction": "add rsp, 0xc8",
"module": "KERNELBASE.dll",
"exception_code": "0x80010012",
"offset": 42141,
"address": "0x7fefda1a49d"
}
},
"time": 1563691998.8742,
"tid": 916,
"flags": {}
},
"pid": 1636,
"type": "call",
"cid": 19
}
],
"references": [],
"name": "raises_exception"
},
{
"markcount": 0,
"families": [],
"description": "One or more potentially interesting buffers were extracted, these generally contain injected code, configuration data, etc.",
"severity": 2,
"marks": [],
"references": [],
"name": "dumped_buffer"
},
{
"markcount": 32,
"families": [],
"description": "Allocates read-write-execute memory (usually to unpack itself)",
"severity": 2,
"marks": [
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00409000"
},
"time": 1563691985.7186,
"tid": 2436,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"region_size": 4096,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0xffffffff",
"allocation_type": 4096,
"base_address": "0x003b0000"
},
"time": 1563691985.7186,
"tid": 2436,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT"
}
},
"pid": 2740,
"type": "call",
"cid": 6
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00419000"
},
"time": 1563691990.8276,
"tid": 2436,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 643
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"region_size": 65536,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 1,
"protection": 64,
"process_handle": "0xffffffff",
"allocation_type": 12288,
"base_address": "0x63db0000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2740,
"type": "call",
"cid": 1084
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x63dec000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1085
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x63dec000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1086
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x63deb000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1087
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x63dec000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1088
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x63deb000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1089
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x77317000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1090
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x75710000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1091
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x63de5000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1092
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x63de5000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1093
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 1,
"length": 65536,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x63db0000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1106
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x763a7000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1107
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x763e9000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1108
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 1,
"length": 65536,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x63db0000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1112
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x75fa0000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1113
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 1,
"length": 65536,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x63db0000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1116
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x63deb000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1117
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x63dec000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1118
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x77314000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1119
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x77314000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1120
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x63dec000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1121
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x63dec000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1122
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x77314000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1123
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 1,
"length": 65536,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x63db0000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1128
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x63dde000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1131
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 1,
"length": 65536,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x63db0000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1134
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x63ddd000"
},
"time": 1563691999.1876,
"tid": 608,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2740,
"type": "call",
"cid": 1135
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2204,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00409000"
},
"time": 1563691991.0158,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 2204,
"type": "call",
"cid": 1
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2204,
"region_size": 4096,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0xffffffff",
"allocation_type": 4096,
"base_address": "0x003c0000"
},
"time": 1563691991.0468,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT"
}
},
"pid": 2204,
"type": "call",
"cid": 6
}
],
"references": [],
"name": "allocates_rwx"
},
{
"markcount": 0,
"families": [],
"description": "Checks whether any human activity is being performed by constantly checking whether the foreground window changed",
"severity": 2,
"marks": [],
"references": [
"https:\/\/www.virusbtn.com\/virusbulletin\/archive\/2015\/09\/vb201509-custom-packer.dkb"
],
"name": "antisandbox_foregroundwindows"
},
{
"markcount": 1,
"families": [],
"description": "Creates hidden or system file",
"severity": 2,
"marks": [
{
"call": {
"category": "file",
"status": 1,
"stacktrace": [],
"api": "NtCreateFile",
"return_value": 0,
"arguments": {
"create_disposition": 2,
"file_handle": "0x00000148",
"filepath": "C:\\Users\\cuck\\AppData\\LocalLow\\uloj.wae",
"desired_access": "0xc0110080",
"file_attributes": 2,
"filepath_r": "\\??\\C:\\Users\\cuck\\AppData\\LocalLow\\uloj.wae",
"create_options": 4192,
"status_info": 2,
"share_access": 1
},
"time": 1563691990.8436,
"tid": 2436,
"flags": {
"create_disposition": "FILE_CREATE",
"desired_access": "FILE_READ_ATTRIBUTES|DELETE|SYNCHRONIZE|GENERIC_WRITE",
"create_options": "FILE_NON_DIRECTORY_FILE|FILE_SYNCHRONOUS_IO_NONALERT|FILE_DELETE_ON_CLOSE",
"file_attributes": "FILE_ATTRIBUTE_HIDDEN",
"status_info": "FILE_CREATED",
"share_access": "FILE_SHARE_READ"
}
},
"pid": 2740,
"type": "call",
"cid": 670
}
],
"references": [],
"name": "creates_hidden_file"
},
{
"markcount": 1,
"families": [],
"description": "Creates a suspicious process",
"severity": 2,
"marks": [
{
"category": "cmdline",
"ioc": "\"C:\\Windows\\system32\\cmd.exe\" \/c \"C:\\Users\\cuck\\AppData\\Local\\Temp\\FHF2E01.bat\"",
"type": "ioc",
"description": null
}
],
"references": [],
"name": "suspicious_process"
},
{
"markcount": 1,
"families": [],
"description": "Drops an executable to the user AppData folder",
"severity": 2,
"marks": [
{
"category": "file",
"ioc": "C:\\Users\\cuck\\AppData\\Roaming\\Kidi\\vaegyv.exe",
"type": "ioc",
"description": null
}
],
"references": [],
"name": "exe_appdata"
},
{
"markcount": 2,
"families": [],
"description": "Searches running processes potentially to identify processes for sandbox evasion, code injection or memory dumping",
"severity": 2,
"marks": [
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "Process32NextW",
"return_value": 1,
"arguments": {
"process_name": "vaegyv.exe",
"snapshot_handle": "0x00000144",
"process_identifier": 2204
},
"time": 1563691999.2188,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 997
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "Process32NextW",
"return_value": 1,
"arguments": {
"process_name": "svchost.exe",
"snapshot_handle": "0x00000178",
"process_identifier": 2392
},
"time": 1563692004.2808,
"tid": 312,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 1450
}
],
"references": [],
"name": "injection_process_search"
},
{
"markcount": 2,
"families": [],
"description": "The binary likely contains encrypted or compressed data indicative of a packer",
"severity": 2,
"marks": [
{
"entropy": 7.9622674515913,
"section": {
"size_of_data": "0x00048a00",
"virtual_address": "0x0000b000",
"entropy": 7.9622674515913,
"name": ".ndata",
"virtual_size": "0x0004e000"
},
"type": "generic",
"description": "A section with a high entropy has been found"
},
{
"entropy": 0.93108974358974,
"type": "generic",
"description": "Overall entropy of this PE file is high"
}
],
"references": [
"http:\/\/www.forensickb.com\/2013\/03\/file-entropy-explained.html",
"http:\/\/virii.es\/U\/Using%20Entropy%20Analysis%20to%20Find%20Encrypted%20and%20Packed%20Malware.pdf"
],
"name": "packer_entropy"
},
{
"markcount": 10,
"families": [],
"description": "One or more of the buffers contains an embedded PE file",
"severity": 3,
"marks": [
{
"category": "buffer",
"ioc": "Buffer with sha1: 3c0848f98a0ffa274f62595992c3670a21e5994b",
"type": "ioc",
"description": null
},
{
"category": "buffer",
"ioc": "Buffer with sha1: c23864f4d3ed36ef26f3bfc495f87f79f23afa01",
"type": "ioc",
"description": null
},
{
"category": "buffer",
"ioc": "Buffer with sha1: 7635b008b2a62e74d2f1bdbcdc29a6b79c7c40d1",
"type": "ioc",
"description": null
},
{
"category": "buffer",
"ioc": "Buffer with sha1: d6e071305d7c94d3f988bde6a60c7572d92a4ec5",
"type": "ioc",
"description": null
},
{
"category": "buffer",
"ioc": "Buffer with sha1: 839fa972b3ef955ba34e7475cd84f47bd8bf6d73",
"type": "ioc",
"description": null
},
{
"category": "buffer",
"ioc": "Buffer with sha1: 75920067b25a3e71da7a4f0c4c6d0e52cfd6a9eb",
"type": "ioc",
"description": null
},
{
"category": "buffer",
"ioc": "Buffer with sha1: b38dde4a59400880eac5af908e189e85609b0db7",
"type": "ioc",
"description": null
},
{
"category": "buffer",
"ioc": "Buffer with sha1: 10e815f8a92b63c1a4e4333c86651431a456ea5d",
"type": "ioc",
"description": null
},
{
"category": "buffer",
"ioc": "Buffer with sha1: c461a888d85efc046a8b3c0bea8d9fb256a9207d",
"type": "ioc",
"description": null
},
{
"category": "buffer",
"ioc": "Buffer with sha1: 2e347f9ffc4e861afde2c16779c0e489e428d46c",
"type": "ioc",
"description": null
}
],
"references": [],
"name": "dumped_buffer2"
},
{
"markcount": 10,
"families": [],
"description": "Allocates execute permission to another process indicative of possible code injection",
"severity": 3,
"marks": [
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1820,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x00000148",
"allocation_type": 12288,
"base_address": "0x00050000"
},
"time": 1563691999.2496,
"tid": 2436,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2740,
"type": "call",
"cid": 1159
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1724,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x02300000"
},
"time": 1563691996.2808,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 768
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1768,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x00130000"
},
"time": 1563691996.8128,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 789
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1788,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x02a40000"
},
"time": 1563691997.4218,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 810
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1692,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x02680000"
},
"time": 1563691997.7658,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 837
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1700,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x01c60000"
},
"time": 1563691997.9848,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 858
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2168,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x03300000"
},
"time": 1563691998.4998,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 891
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1636,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x01c70000"
},
"time": 1563691998.5308,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 922
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1596,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x03850000"
},
"time": 1563691998.8278,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 943
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x022e0000"
},
"time": 1563691998.8598,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 982
}
],
"references": [],
"name": "allocates_execute_remote_process"
},
{
"markcount": 1,
"families": [],
"description": "Installs itself for autorun at Windows startup",
"severity": 3,
"marks": [
{
"type": "generic",
"reg_key": "HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Run\\Vaegyv",
"reg_value": "C:\\Users\\cuck\\AppData\\Roaming\\Kidi\\vaegyv.exe"
}
],
"references": [],
"name": "persistence_autorun"
},
{
"markcount": 18,
"families": [],
"description": "Creates a thread using CreateRemoteThread in a non-child process indicative of process injection",
"severity": 3,
"marks": [
{
"category": "Process injection",
"ioc": "Process 2204 created a remote thread in non-child process 1724",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 0,
"stacktrace": [],
"last_error": 5,
"nt_status": -1073741790,
"api": "CreateRemoteThread",
"return_value": 0,
"arguments": {
"thread_identifier": 0,
"process_identifier": 1724,
"function_address": "0x02324fcf",
"flags": 0,
"process_handle": "0x0000014c",
"parameter": "0x00000000",
"stack_size": 0
},
"time": 1563691996.8128,
"tid": 2492,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 778
},
{
"category": "Process injection",
"ioc": "Process 2204 created a remote thread in non-child process 1768",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 0,
"stacktrace": [],
"last_error": 5,
"nt_status": -1073741790,
"api": "CreateRemoteThread",
"return_value": 0,
"arguments": {
"thread_identifier": 0,
"process_identifier": 1768,
"function_address": "0x00154fcf",
"flags": 0,
"process_handle": "0x0000014c",
"parameter": "0x00000000",
"stack_size": 0
},
"time": 1563691997.4218,
"tid": 2572,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 799
},
{
"category": "Process injection",
"ioc": "Process 2204 created a remote thread in non-child process 1788",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 0,
"stacktrace": [],
"last_error": 5,
"nt_status": -1073741790,
"api": "CreateRemoteThread",
"return_value": 0,
"arguments": {
"thread_identifier": 0,
"process_identifier": 1788,
"function_address": "0x02a64fcf",
"flags": 0,
"process_handle": "0x0000014c",
"parameter": "0x00000000",
"stack_size": 0
},
"time": 1563691997.7658,
"tid": 2648,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 820
},
{
"category": "Process injection",
"ioc": "Process 2204 created a remote thread in non-child process 1692",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 0,
"stacktrace": [],
"last_error": 5,
"nt_status": -1073741790,
"api": "CreateRemoteThread",
"return_value": 0,
"arguments": {
"thread_identifier": 0,
"process_identifier": 1692,
"function_address": "0x026a4fcf",
"flags": 0,
"process_handle": "0x0000014c",
"parameter": "0x00000000",
"stack_size": 0
},
"time": 1563691997.9528,
"tid": 2844,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 847
},
{
"category": "Process injection",
"ioc": "Process 2204 created a remote thread in non-child process 1700",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 0,
"stacktrace": [],
"last_error": 5,
"nt_status": -1073741790,
"api": "CreateRemoteThread",
"return_value": 0,
"arguments": {
"thread_identifier": 0,
"process_identifier": 1700,
"function_address": "0x01c84fcf",
"flags": 0,
"process_handle": "0x0000014c",
"parameter": "0x00000000",
"stack_size": 0
},
"time": 1563691998.4998,
"tid": 2784,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 868
},
{
"category": "Process injection",
"ioc": "Process 2204 created a remote thread in non-child process 2168",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 0,
"stacktrace": [],
"last_error": 5,
"nt_status": -1073741790,
"api": "CreateRemoteThread",
"return_value": 0,
"arguments": {
"thread_identifier": 0,
"process_identifier": 2168,
"function_address": "0x03324fcf",
"flags": 0,
"process_handle": "0x0000014c",
"parameter": "0x00000000",
"stack_size": 0
},
"time": 1563691998.5308,
"tid": 2796,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 901
},
{
"category": "Process injection",
"ioc": "Process 2204 created a remote thread in non-child process 1636",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 0,
"stacktrace": [],
"last_error": 5,
"nt_status": -1073741790,
"api": "CreateRemoteThread",
"return_value": 0,
"arguments": {
"thread_identifier": 0,
"process_identifier": 1636,
"function_address": "0x01c94fcf",
"flags": 0,
"process_handle": "0x0000014c",
"parameter": "0x00000000",
"stack_size": 0
},
"time": 1563691998.8278,
"tid": 2772,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 932
},
{
"category": "Process injection",
"ioc": "Process 2204 created a remote thread in non-child process 1596",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 0,
"stacktrace": [],
"last_error": 5,
"nt_status": -1073741790,
"api": "CreateRemoteThread",
"return_value": 0,
"arguments": {
"thread_identifier": 0,
"process_identifier": 1596,
"function_address": "0x03874fcf",
"flags": 0,
"process_handle": "0x0000014c",
"parameter": "0x00000000",
"stack_size": 0
},
"time": 1563691998.8598,
"tid": 2948,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 953
},
{
"category": "Process injection",
"ioc": "Process 2204 created a remote thread in non-child process 2740",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "CreateRemoteThread",
"return_value": 340,
"arguments": {
"thread_identifier": 0,
"process_identifier": 2740,
"function_address": "0x02304fcf",
"flags": 0,
"process_handle": "0x0000014c",
"parameter": "0x00000000",
"stack_size": 0
},
"time": 1563691999.1558,
"tid": 1096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 992
}
],
"references": [
"www.endgame.com\/blog\/technical-blog\/ten-process-injection-techniques-technical-survey-common-and-trending-process"
],
"name": "injection_createremotethread"
},
{
"markcount": 20,
"families": [],
"description": "Manipulates memory of a non-child process indicative of process injection",
"severity": 3,
"marks": [
{
"category": "Process injection",
"ioc": "Process 2740 manipulating memory of non-child process 1820",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1820,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x00000148",
"allocation_type": 12288,
"base_address": "0x00050000"
},
"time": 1563691999.2496,
"tid": 2436,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2740,
"type": "call",
"cid": 1159
},
{
"category": "Process injection",
"ioc": "Process 2204 manipulating memory of non-child process 1724",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1724,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x02300000"
},
"time": 1563691996.2808,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 768
},
{
"category": "Process injection",
"ioc": "Process 2204 manipulating memory of non-child process 1768",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1768,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x00130000"
},
"time": 1563691996.8128,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 789
},
{
"category": "Process injection",
"ioc": "Process 2204 manipulating memory of non-child process 1788",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1788,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x02a40000"
},
"time": 1563691997.4218,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 810
},
{
"category": "Process injection",
"ioc": "Process 2204 manipulating memory of non-child process 1692",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1692,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x02680000"
},
"time": 1563691997.7658,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 837
},
{
"category": "Process injection",
"ioc": "Process 2204 manipulating memory of non-child process 1700",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1700,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x01c60000"
},
"time": 1563691997.9848,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 858
},
{
"category": "Process injection",
"ioc": "Process 2204 manipulating memory of non-child process 2168",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2168,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x03300000"
},
"time": 1563691998.4998,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 891
},
{
"category": "Process injection",
"ioc": "Process 2204 manipulating memory of non-child process 1636",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1636,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x01c70000"
},
"time": 1563691998.5308,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 922
},
{
"category": "Process injection",
"ioc": "Process 2204 manipulating memory of non-child process 1596",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1596,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x03850000"
},
"time": 1563691998.8278,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 943
},
{
"category": "Process injection",
"ioc": "Process 2204 manipulating memory of non-child process 2740",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2740,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x022e0000"
},
"time": 1563691998.8598,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 982
}
],
"references": [
"www.endgame.com\/blog\/technical-blog\/ten-process-injection-techniques-technical-survey-common-and-trending-process"
],
"name": "injection_modifies_memory"
},
{
"markcount": 50,
"families": [],
"description": "Potential code injection by writing to the memory of another process",
"severity": 3,
"marks": [
{
"category": "Process injection",
"ioc": "Process 2740 injected into non-child 1820",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1820,
"buffer": "\u0000\u0000\u0000\u0000",
"process_handle": "0x00000148",
"base_address": "0x00092958"
},
"time": 1563691999.5626,
"tid": 2436,
"flags": {}
},
"pid": 2740,
"type": "call",
"cid": 1162
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1820,
"buffer": "\u0000\u0000\u0005\u0000",
"process_handle": "0x00000148",
"base_address": "0x0009296c"
},
"time": 1563691999.5626,
"tid": 2436,
"flags": {}
},
"pid": 2740,
"type": "call",
"cid": 1163
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1820,
"buffer": "\b\u0000\u0000\u0000",
"process_handle": "0x00000148",
"base_address": "0x00092fc8"
},
"time": 1563691999.5626,
"tid": 2436,
"flags": {}
},
"pid": 2740,
"type": "call",
"cid": 1165
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1820,
"buffer": "\f\u0000\u0000\u0000",
"process_handle": "0x00000148",
"base_address": "0x00092fcc"
},
"time": 1563691999.5626,
"tid": 2436,
"flags": {}
},
"pid": 2740,
"type": "call",
"cid": 1167
},
{
"category": "Process injection",
"ioc": "Process 2204 injected into non-child 1724",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1724,
"buffer": "\u0000\u0000\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x02342958"
},
"time": 1563691996.6098,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 771
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1724,
"buffer": "\u0000\u00000\u0002",
"process_handle": "0x0000014c",
"base_address": "0x0234296c"
},
"time": 1563691996.6098,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 772
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1724,
"buffer": "\u009c\u0003\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x02342fc8"
},
"time": 1563691996.6098,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 774
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1724,
"buffer": "\u0094\u0003\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x02342fcc"
},
"time": 1563691996.6098,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 776
},
{
"category": "Process injection",
"ioc": "Process 2204 injected into non-child 1768",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1768,
"buffer": "\u0000\u0000\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x00172958"
},
"time": 1563691997.2348,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 792
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1768,
"buffer": "\u0000\u0000\u0013\u0000",
"process_handle": "0x0000014c",
"base_address": "0x0017296c"
},
"time": 1563691997.2348,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 793
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1768,
"buffer": "4\u0001\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x00172fc8"
},
"time": 1563691997.2348,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 795
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1768,
"buffer": "\u00d8\u0000\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x00172fcc"
},
"time": 1563691997.2348,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 797
},
{
"category": "Process injection",
"ioc": "Process 2204 injected into non-child 1788",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1788,
"buffer": "\u0000\u0000\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x02a82958"
},
"time": 1563691997.4378,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 813
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1788,
"buffer": "\u0000\u0000\u00a4\u0002",
"process_handle": "0x0000014c",
"base_address": "0x02a8296c"
},
"time": 1563691997.4378,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 814
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1788,
"buffer": "\u0084\u000f\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x02a82fc8"
},
"time": 1563691997.4378,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 816
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1788,
"buffer": "D\u0005\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x02a82fcc"
},
"time": 1563691997.4378,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 818
},
{
"category": "Process injection",
"ioc": "Process 2204 injected into non-child 1692",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1692,
"buffer": "\u0000\u0000\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x026c2958"
},
"time": 1563691997.7808,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 840
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1692,
"buffer": "\u0000\u0000h\u0002",
"process_handle": "0x0000014c",
"base_address": "0x026c296c"
},
"time": 1563691997.7808,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 841
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1692,
"buffer": "x\u0001\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x026c2fc8"
},
"time": 1563691997.7808,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 843
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1692,
"buffer": "D\u0001\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x026c2fcc"
},
"time": 1563691997.7808,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 845
},
{
"category": "Process injection",
"ioc": "Process 2204 injected into non-child 1700",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1700,
"buffer": "\u0000\u0000\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x01ca2958"
},
"time": 1563691998.2968,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 861
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1700,
"buffer": "\u0000\u0000\u00c6\u0001",
"process_handle": "0x0000014c",
"base_address": "0x01ca296c"
},
"time": 1563691998.2968,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 862
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1700,
"buffer": "\u0000\u0001\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x01ca2fc8"
},
"time": 1563691998.2968,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 864
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1700,
"buffer": "\u0004\u0001\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x01ca2fcc"
},
"time": 1563691998.2968,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 866
},
{
"category": "Process injection",
"ioc": "Process 2204 injected into non-child 2168",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 2168,
"buffer": "\u0000\u0000\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x03342958"
},
"time": 1563691998.5308,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 894
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 2168,
"buffer": "\u0000\u00000\u0003",
"process_handle": "0x0000014c",
"base_address": "0x0334296c"
},
"time": 1563691998.5308,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 895
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 2168,
"buffer": "t\u0001\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x03342fc8"
},
"time": 1563691998.5308,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 897
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 2168,
"buffer": "x\u0001\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x03342fcc"
},
"time": 1563691998.5308,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 899
},
{
"category": "Process injection",
"ioc": "Process 2204 injected into non-child 1636",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1636,
"buffer": "\u0000\u0000\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x01cb2958"
},
"time": 1563691998.5468,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 925
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1636,
"buffer": "\u0000\u0000\u00c7\u0001",
"process_handle": "0x0000014c",
"base_address": "0x01cb296c"
},
"time": 1563691998.5468,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 926
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1636,
"buffer": "t\u0002\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x01cb2fc8"
},
"time": 1563691998.5468,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 928
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1636,
"buffer": "X\u0002\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x01cb2fcc"
},
"time": 1563691998.5468,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 930
},
{
"category": "Process injection",
"ioc": "Process 2204 injected into non-child 1596",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1596,
"buffer": "\u0000\u0000\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x03892958"
},
"time": 1563691998.8438,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 946
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1596,
"buffer": "\u0000\u0000\u0085\u0003",
"process_handle": "0x0000014c",
"base_address": "0x0389296c"
},
"time": 1563691998.8438,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 947
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1596,
"buffer": "\u00b4\u0003\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x03892fc8"
},
"time": 1563691998.8438,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 949
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1596,
"buffer": " \u0004\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x03892fcc"
},
"time": 1563691998.8438,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 951
},
{
"category": "Process injection",
"ioc": "Process 2204 injected into non-child 2740",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 2740,
"buffer": "\u0000\u0000\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x02322958"
},
"time": 1563691999.1558,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 985
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 2740,
"buffer": "\u0000\u0000.\u0002",
"process_handle": "0x0000014c",
"base_address": "0x0232296c"
},
"time": 1563691999.1558,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 986
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 2740,
"buffer": "X\u0001\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x02322fc8"
},
"time": 1563691999.1558,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 988
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 2740,
"buffer": "\\\u0001\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x02322fcc"
},
"time": 1563691999.1558,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 990
}
],
"references": [],
"name": "injection_write_memory"
},
{
"markcount": 2,
"families": [],
"description": "Used NtSetContextThread to modify a thread in a remote process indicative of process injection",
"severity": 3,
"marks": [
{
"category": "Process injection",
"ioc": "Process 2740 called NtSetContextThread to modify thread in remote process 1820",
"type": "ioc",
"description": null
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtSetContextThread",
"return_value": 0,
"arguments": {
"thread_handle": "0x00000140",
"registers": {
"eip": 2008678852,
"esp": 4454776,
"edi": 0,
"eax": 479128,
"ebp": 0,
"edx": 0,
"ebx": 2130567168,
"esi": 0,
"ecx": 0
},
"process_identifier": 1820
},
"time": 1563691999.5626,
"tid": 2436,
"flags": {}
},
"pid": 2740,
"type": "call",
"cid": 1169
}
],
"references": [
"www.endgame.com\/blog\/technical-blog\/ten-process-injection-techniques-technical-survey-common-and-trending-process"
],
"name": "injection_ntsetcontextthread"
},
{
"markcount": 56,
"families": [
"zeus"
],
"description": "Zeus P2P (Banking Trojan)",
"severity": 3,
"marks": [
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-E8E1-B06EFA019373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{56060262-19CC-D5E3-A920-6470BBC0476D}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-2CEA-B06E3E0A9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-FCEB-B06EEE0B9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-60EB-B06E720B9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Local\\{C8B94219-59B7-4B5C-A920-6470BBC0476D}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-4CEC-B06E5E0C9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-E0E8-B06EF2089373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{A5B32338-3896-2656-A920-6470BBC0476D}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-F4EB-B06EE60B9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-48EE-B06E5A0E9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-58E9-B06E4A099373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-CCEB-B06EDE0B9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-B4EC-B06EA60C9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-BCE8-B06EAE089373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-9CE0-B06E8E009373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-3CEB-B06E2E0B9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-D4EC-B06EC60C9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-50EB-B06E420B9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-80EB-B06E920B9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-78E8-B06E6A089373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-0CE9-B06E1E099373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{73B5150B-0EA5-F050-A920-6470BBC0476D}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-94EC-B06E860C9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-C0E9-B06ED2099373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-8CEC-B06E9E0C9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-28E0-B06E3A009373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-A8EB-B06EBA0B9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{C3671720-0C8E-4082-A920-6470BBC0476D}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-0CEF-B06E1E0F9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-E8EE-B06EFA0E9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-0CE3-B06E1E039373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-24EC-B06E360C9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-34ED-B06E260D9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-D0E1-B06EC2019373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-C0EC-B06ED20C9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-70EC-B06E620C9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-C8EB-B06EDA0B9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-68ED-B06E7A0D9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{A95FF40A-EFA4-2ABA-A920-6470BBC0476D}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Local\\{E91F2729-3C87-6AFA-A920-6470BBC0476D}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-D4EA-B06EC60A9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-50E2-B06E42029373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-14EE-B06E060E9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{A95FF40D-EFA3-2ABA-A920-6470BBC0476D}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Local\\{C8B94218-59B6-4B5C-A920-6470BBC0476D}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-14EC-B06E060C9373}",
"type": "ioc",
"description": null
},
{
"category": "mutex",
"ioc": "Global\\{224A23F9-3857-A1AF-70E3-B06E62039373}",
"type": "ioc",
"description": null
},
{
"category": "udp",
"ioc": {
"src": "192.168.56.101",
"dst": "224.0.0.252",
"offset": 7070,
"time": 3.0386309623718,
"dport": 5355,
"sport": 51001
},
"type": "ioc",
"description": null
},
{
"category": "udp",
"ioc": {
"src": "192.168.56.101",
"dst": "224.0.0.252",
"offset": 7398,
"time": 1.0355870723724,
"dport": 5355,
"sport": 53595
},
"type": "ioc",
"description": null
}
],
"references": [
"https:\/\/malwr.com\/analysis\/NmNhODg5ZWRkYjc0NDY0M2I3YTJhNDRlM2FlOTZiMjA\/",
"https:\/\/malwr.com\/analysis\/MmMwNDJlMTI0MTNkNGFjNmE0OGY3Y2I5MjhiMGI1NzI\/",
"https:\/\/malwr.com\/analysis\/MzY5ZTM2NzZhMzI3NDY2YjgzMjJiODFkODZkYzIwYmQ\/",
"https:\/\/www.virustotal.com\/de\/file\/301fcadf53e6a6167e559c84d6426960af8626d12b2e25aa41de6dce511d0568\/analysis\/#behavioural-info",
"https:\/\/www.virustotal.com\/de\/file\/d3cf49a7ac726ee27eae9d29dee648e34cb3e8fd9d494e1b347209677d62cdf9\/analysis\/#behavioural-info",
"https:\/\/www.virustotal.com\/de\/file\/d3cf49a7ac726ee27eae9d29dee648e34cb3e8fd9d494e1b347209677d62cdf9\/analysis\/#behavioural-info",
"https:\/\/www.virustotal.com\/de\/file\/301fcadf53e6a6167e559c84d6426960af8626d12b2e25aa41de6dce511d0568\/analysis\/#behavioural-info"
],
"name": "banker_zeus_p2p"
},
{
"markcount": 73,
"families": [],
"description": "Executed a process and injected code into it, probably while unpacking",
"severity": 5,
"marks": [
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtResumeThread",
"return_value": 0,
"arguments": {
"thread_handle": "0x00000114",
"suspend_count": 1,
"process_identifier": 2740
},
"time": 1563691990.7966,
"tid": 2436,
"flags": {}
},
"pid": 2740,
"type": "call",
"cid": 469
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "CreateProcessInternalW",
"return_value": 1,
"arguments": {
"thread_identifier": 2096,
"thread_handle": "0x00000144",
"process_identifier": 2204,
"current_directory": "C:\\Users\\cuck\\AppData\\Roaming",
"filepath": "",
"track": 1,
"command_line": "\"C:\\Users\\cuck\\AppData\\Roaming\\Kidi\\vaegyv.exe\"",
"filepath_r": "",
"stack_pivoted": 0,
"creation_flags": 67108864,
"process_handle": "0x00000148",
"inherit_handles": 0
},
"time": 1563691990.8906,
"tid": 2436,
"flags": {
"creation_flags": "CREATE_DEFAULT_ERROR_MODE"
}
},
"pid": 2740,
"type": "call",
"cid": 706
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1820,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x00000148",
"allocation_type": 12288,
"base_address": "0x00050000"
},
"time": 1563691999.2496,
"tid": 2436,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2740,
"type": "call",
"cid": 1159
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"buffer": "7635b008b2a62e74d2f1bdbcdc29a6b79c7c40d1",
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1820,
"buffer": "",
"process_handle": "0x00000148",
"base_address": "0x00050000"
},
"time": 1563691999.2496,
"tid": 2436,
"flags": {}
},
"pid": 2740,
"type": "call",
"cid": 1160
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1820,
"buffer": "\u0000\u0000\u0000\u0000",
"process_handle": "0x00000148",
"base_address": "0x00092958"
},
"time": 1563691999.5626,
"tid": 2436,
"flags": {}
},
"pid": 2740,
"type": "call",
"cid": 1162
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1820,
"buffer": "\u0000\u0000\u0005\u0000",
"process_handle": "0x00000148",
"base_address": "0x0009296c"
},
"time": 1563691999.5626,
"tid": 2436,
"flags": {}
},
"pid": 2740,
"type": "call",
"cid": 1163
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1820,
"buffer": "\b\u0000\u0000\u0000",
"process_handle": "0x00000148",
"base_address": "0x00092fc8"
},
"time": 1563691999.5626,
"tid": 2436,
"flags": {}
},
"pid": 2740,
"type": "call",
"cid": 1165
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1820,
"buffer": "\f\u0000\u0000\u0000",
"process_handle": "0x00000148",
"base_address": "0x00092fcc"
},
"time": 1563691999.5626,
"tid": 2436,
"flags": {}
},
"pid": 2740,
"type": "call",
"cid": 1167
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtGetContextThread",
"return_value": 0,
"arguments": {
"thread_handle": "0x00000140"
},
"time": 1563691999.5626,
"tid": 2436,
"flags": {}
},
"pid": 2740,
"type": "call",
"cid": 1168
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtSetContextThread",
"return_value": 0,
"arguments": {
"thread_handle": "0x00000140",
"registers": {
"eip": 2008678852,
"esp": 4454776,
"edi": 0,
"eax": 479128,
"ebp": 0,
"edx": 0,
"ebx": 2130567168,
"esi": 0,
"ecx": 0
},
"process_identifier": 1820
},
"time": 1563691999.5626,
"tid": 2436,
"flags": {}
},
"pid": 2740,
"type": "call",
"cid": 1169
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "CreateProcessInternalW",
"return_value": 1,
"arguments": {
"thread_identifier": 2356,
"thread_handle": "0x00000140",
"process_identifier": 1820,
"current_directory": "",
"filepath": "",
"track": 1,
"command_line": "\"C:\\Windows\\system32\\cmd.exe\" \/c \"C:\\Users\\cuck\\AppData\\Local\\Temp\\FHF2E01.bat\"",
"filepath_r": "",
"stack_pivoted": 0,
"creation_flags": 67108864,
"process_handle": "0x00000148",
"inherit_handles": 0
},
"time": 1563691999.6096,
"tid": 2436,
"flags": {
"creation_flags": "CREATE_DEFAULT_ERROR_MODE"
}
},
"pid": 2740,
"type": "call",
"cid": 1171
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtResumeThread",
"return_value": 0,
"arguments": {
"thread_handle": "0x00000114",
"suspend_count": 1,
"process_identifier": 2204
},
"time": 1563691996.1098,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 469
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1724,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x02300000"
},
"time": 1563691996.2808,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 768
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"buffer": "2e347f9ffc4e861afde2c16779c0e489e428d46c",
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1724,
"buffer": "",
"process_handle": "0x0000014c",
"base_address": "0x02300000"
},
"time": 1563691996.2808,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 769
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1724,
"buffer": "\u0000\u0000\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x02342958"
},
"time": 1563691996.6098,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 771
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1724,
"buffer": "\u0000\u00000\u0002",
"process_handle": "0x0000014c",
"base_address": "0x0234296c"
},
"time": 1563691996.6098,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 772
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1724,
"buffer": "\u009c\u0003\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x02342fc8"
},
"time": 1563691996.6098,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 774
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1724,
"buffer": "\u0094\u0003\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x02342fcc"
},
"time": 1563691996.6098,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 776
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1768,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x00130000"
},
"time": 1563691996.8128,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 789
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"buffer": "839fa972b3ef955ba34e7475cd84f47bd8bf6d73",
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1768,
"buffer": "",
"process_handle": "0x0000014c",
"base_address": "0x00130000"
},
"time": 1563691996.8128,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 790
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1768,
"buffer": "\u0000\u0000\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x00172958"
},
"time": 1563691997.2348,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 792
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1768,
"buffer": "\u0000\u0000\u0013\u0000",
"process_handle": "0x0000014c",
"base_address": "0x0017296c"
},
"time": 1563691997.2348,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 793
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1768,
"buffer": "4\u0001\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x00172fc8"
},
"time": 1563691997.2348,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 795
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1768,
"buffer": "\u00d8\u0000\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x00172fcc"
},
"time": 1563691997.2348,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 797
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1788,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x02a40000"
},
"time": 1563691997.4218,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 810
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"buffer": "3c0848f98a0ffa274f62595992c3670a21e5994b",
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1788,
"buffer": "",
"process_handle": "0x0000014c",
"base_address": "0x02a40000"
},
"time": 1563691997.4218,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 811
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1788,
"buffer": "\u0000\u0000\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x02a82958"
},
"time": 1563691997.4378,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 813
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1788,
"buffer": "\u0000\u0000\u00a4\u0002",
"process_handle": "0x0000014c",
"base_address": "0x02a8296c"
},
"time": 1563691997.4378,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 814
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1788,
"buffer": "\u0084\u000f\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x02a82fc8"
},
"time": 1563691997.4378,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 816
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1788,
"buffer": "D\u0005\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x02a82fcc"
},
"time": 1563691997.4378,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 818
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1692,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x02680000"
},
"time": 1563691997.7658,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 837
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"buffer": "75920067b25a3e71da7a4f0c4c6d0e52cfd6a9eb",
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1692,
"buffer": "",
"process_handle": "0x0000014c",
"base_address": "0x02680000"
},
"time": 1563691997.7658,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 838
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1692,
"buffer": "\u0000\u0000\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x026c2958"
},
"time": 1563691997.7808,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 840
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1692,
"buffer": "\u0000\u0000h\u0002",
"process_handle": "0x0000014c",
"base_address": "0x026c296c"
},
"time": 1563691997.7808,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 841
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1692,
"buffer": "x\u0001\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x026c2fc8"
},
"time": 1563691997.7808,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 843
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1692,
"buffer": "D\u0001\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x026c2fcc"
},
"time": 1563691997.7808,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 845
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1700,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x01c60000"
},
"time": 1563691997.9848,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 858
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"buffer": "10e815f8a92b63c1a4e4333c86651431a456ea5d",
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1700,
"buffer": "",
"process_handle": "0x0000014c",
"base_address": "0x01c60000"
},
"time": 1563691997.9848,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 859
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1700,
"buffer": "\u0000\u0000\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x01ca2958"
},
"time": 1563691998.2968,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 861
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1700,
"buffer": "\u0000\u0000\u00c6\u0001",
"process_handle": "0x0000014c",
"base_address": "0x01ca296c"
},
"time": 1563691998.2968,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 862
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1700,
"buffer": "\u0000\u0001\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x01ca2fc8"
},
"time": 1563691998.2968,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 864
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1700,
"buffer": "\u0004\u0001\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x01ca2fcc"
},
"time": 1563691998.2968,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 866
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 2168,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x03300000"
},
"time": 1563691998.4998,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 891
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"buffer": "c23864f4d3ed36ef26f3bfc495f87f79f23afa01",
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 2168,
"buffer": "",
"process_handle": "0x0000014c",
"base_address": "0x03300000"
},
"time": 1563691998.4998,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 892
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 2168,
"buffer": "\u0000\u0000\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x03342958"
},
"time": 1563691998.5308,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 894
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 2168,
"buffer": "\u0000\u00000\u0003",
"process_handle": "0x0000014c",
"base_address": "0x0334296c"
},
"time": 1563691998.5308,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 895
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 2168,
"buffer": "t\u0001\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x03342fc8"
},
"time": 1563691998.5308,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 897
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 2168,
"buffer": "x\u0001\u0000\u0000",
"process_handle": "0x0000014c",
"base_address": "0x03342fcc"
},
"time": 1563691998.5308,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 899
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtAllocateVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1636,
"region_size": 299008,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"protection": 64,
"process_handle": "0x0000014c",
"allocation_type": 12288,
"base_address": "0x01c70000"
},
"time": 1563691998.5308,
"tid": 2096,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE",
"allocation_type": "MEM_COMMIT|MEM_RESERVE"
}
},
"pid": 2204,
"type": "call",
"cid": 922
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"buffer": "d6e071305d7c94d3f988bde6a60c7572d92a4ec5",
"api": "WriteProcessMemory",
"return_value": 1,
"arguments": {
"process_identifier": 1636,
"buffer": "",
"process_handle": "0x0000014c",
"base_address": "0x01c70000"
},
"time": 1563691998.5308,
"tid": 2096,
"flags": {}
},
"pid": 2204,
"type": "call",
"cid": 923
}
],
"references": [],
"name": "injection_runpe"
}
]Yara
The Yara rules did not detect anything in the file.
Network
{
"tls": [],
"udp": [
{
"src": "192.168.56.101",
"dst": "192.168.56.255",
"offset": 546,
"time": 3.0786981582642,
"dport": 137,
"sport": 137
},
{
"src": "192.168.56.101",
"dst": "192.168.56.255",
"offset": 5226,
"time": 9.0798161029816,
"dport": 138,
"sport": 138
},
{
"src": "192.168.56.101",
"dst": "224.0.0.252",
"offset": 7070,
"time": 3.0386309623718,
"dport": 5355,
"sport": 51001
},
{
"src": "192.168.56.101",
"dst": "224.0.0.252",
"offset": 7398,
"time": 1.0355870723724,
"dport": 5355,
"sport": 53595
},
{
"src": "192.168.56.101",
"dst": "224.0.0.252",
"offset": 7726,
"time": 3.0529019832611,
"dport": 5355,
"sport": 53848
},
{
"src": "192.168.56.101",
"dst": "224.0.0.252",
"offset": 8054,
"time": 1.5337901115417,
"dport": 5355,
"sport": 54255
},
{
"src": "192.168.56.101",
"dst": "224.0.0.252",
"offset": 8382,
"time": -0.098152875900269,
"dport": 5355,
"sport": 55314
},
{
"src": "192.168.56.101",
"dst": "239.255.255.250",
"offset": 8710,
"time": 1.5472280979156,
"dport": 1900,
"sport": 1900
},
{
"src": "192.168.56.101",
"dst": "239.255.255.250",
"offset": 28120,
"time": 1.054172039032,
"dport": 3702,
"sport": 49152
},
{
"src": "192.168.56.101",
"dst": "239.255.255.250",
"offset": 36504,
"time": 3.1258690357208,
"dport": 1900,
"sport": 53598
}
],
"dns_servers": [],
"http": [],
"icmp": [],
"smtp": [],
"tcp": [],
"smtp_ex": [],
"mitm": [],
"hosts": [],
"pcap_sha256": "f474e26933bef2c18b897760fdc11c80fb23280fd06cb21d3401e5b02c9116e6",
"dns": [],
"http_ex": [],
"domains": [],
"dead_hosts": [],
"sorted_pcap_sha256": "3153819e74417fadc9a2f91802382cf4b9f8cd30d9a5a9a2101d863546ab5b86",
"irc": [],
"https_ex": []
}Screenshots







EBJeSN.exe removal instructions
The instructions below shows how to remove EBJeSN.exe with help from the FreeFixer removal tool. Basically, you install FreeFixer, scan your computer, check the EBJeSN.exe file for removal, restart your computer and scan it again to verify that EBJeSN.exe has been successfully removed. Here are the removal instructions in more detail:
- Download and install FreeFixer: http://www.freefixer.com/download.html
- When the scan is finished, locate EBJeSN.exe in the scan result and tick the checkbox next to the EBJeSN.exe file. Do not check any other file for removal unless you are 100% sure you want to delete it. Tip: Press CTRL-F to open up FreeFixer's search dialog to quickly locate EBJeSN.exe in the scan result.


 c:\downloads\EBJeSN.exe
c:\downloads\EBJeSN.exe 
- Restart your computer.
- Start FreeFixer and scan your computer again. If EBJeSN.exe still remains in the scan result, proceed with the next step. If EBJeSN.exe is gone from the scan result you're done.
- If EBJeSN.exe still remains in the scan result, check its checkbox again in the scan result and click Fix.
- Restart your computer.
- Start FreeFixer and scan your computer again. Verify that EBJeSN.exe no longer appear in the scan result.
Hashes [?]
| Property | Value |
|---|---|
| MD5 | 33ff431f3f2c4c597d1e5b404ee3d122 |
| SHA256 | a557fa363f1bce12c415a22d1d81905cc007e12bec6fb117f48275cf9b280e09 |
Error Messages
These are some of the error messages that can appear related to ebjesn.exe:
ebjesn.exe has encountered a problem and needs to close. We are sorry for the inconvenience.
ebjesn.exe - Application Error. The instruction at "0xXXXXXXXX" referenced memory at "0xXXXXXXXX". The memory could not be "read/written". Click on OK to terminate the program.
ebjesn.exe has stopped working.
End Program - ebjesn.exe. This program is not responding.
ebjesn.exe is not a valid Win32 application.
ebjesn.exe - Application Error. The application failed to initialize properly (0xXXXXXXXX). Click OK to terminate the application.
What will you do with EBJeSN.exe?
To help other users, please let us know what you will do with EBJeSN.exe:
Comments
Please share with the other users what you think about this file. What does this file do? Is it legitimate or something that your computer is better without? Do you know how it was installed on your system? Did you install it yourself or did it come bundled with some other software? Is it running smoothly or do you get some error message? Any information that will help to document this file is welcome. Thank you for your contributions.
I'm reading all new comments so don't hesitate to post a question about the file. If I don't have the answer perhaps another user can help you.
No comments posted yet.