What is armsvc.exe?
armsvc.exe is part of Adobe Acrobat Update Service and developed by Adobe Systems according to the armsvc.exe version information.
armsvc.exe's description is "Adobe Acrobat Update Service"
armsvc.exe is usually located in the 'c:\program files (x86)\common files\adobe\arm\1.0\' folder.
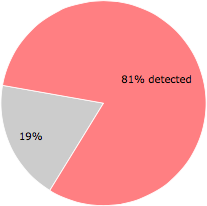
Some of the anti-virus scanners at VirusTotal detected armsvc.exe.
If you have additional information about the file, please share it with the FreeFixer users by posting a comment at the bottom of this page.
Vendor and version information [?]
The following is the available information on armsvc.exe:
| Property | Value |
|---|---|
| Product name | Adobe Acrobat Update Service |
| Company name | Adobe Systems |
| File description | Adobe Acrobat Update Service |
| Internal name | armsvc.exe |
| Original filename | armsvc.exe |
| Legal copyright | Copyright © 2019 Adobe Systems. All rights reserved. |
| Product version | 1.824.36.9436 |
| File version | 1.824.36.9436 |
Here's a screenshot of the file properties when displayed by Windows Explorer:
| Product name | Adobe Acrobat Update Service |
| Company name | Adobe Systems |
| File description | Adobe Acrobat Update Service |
| Internal name | armsvc.exe |
| Original filename | armsvc.exe |
| Legal copyright | Copyright © 2019 Adobe Systems. Al.. |
| Product version | 1.824.36.9436 |
| File version | 1.824.36.9436 |
VirusTotal report
59 of the 73 anti-virus programs at VirusTotal detected the armsvc.exe file. That's a 81% detection rate.
| Scanner | Detection Name |
|---|---|
| Acronis | suspicious |
| Ad-Aware | Win32.Floxif.A |
| AhnLab-V3 | Win32/Fixflo.GEN |
| ALYac | Win32.Floxif.A |
| Antiy-AVL | Virus/Win32.Pioneer.cz |
| APEX | Malicious |
| Arcabit | Win32.Floxif.A |
| Avast | Win32:FloxLib-A [Trj] |
| AVG | Win32:FloxLib-A [Trj] |
| Avira | W32/Floxif.hdc |
| Baidu | Win32.Virus.Floxif.a |
| BitDefender | Win32.Floxif.A |
| BitDefenderTheta | AI:FileInfector.207622A70E |
| Bkav | W32.FloxitNV.PE |
| CAT-QuickHeal | W32.Pioneer.CZ1 |
| Comodo | Virus.Win32.Floxif.A@7h5wha |
| CrowdStrike | win/malicious_confidence_100% (D) |
| Cybereason | malicious.d1b9a1 |
| Cylance | Unsafe |
| Cyren | W32/Floxif.B |
| DrWeb | Win32.FloodFix.7 |
| eGambit | Trojan.Generic |
| Emsisoft | Win32.Floxif.A (B) |
| Endgame | malicious (high confidence) |
| ESET-NOD32 | Win32/Floxif.H |
| F-Prot | W32/Floxif.B |
| F-Secure | Malware.W32/Floxif.hdc |
| FireEye | Generic.mg.ea6b545d1b9a14d5 |
| Fortinet | W32/Pioneer.CZ!tr |
| GData | Win32.Floxif.A |
| Ikarus | Virus.Win32.Floxif.A |
| Invincea | heuristic |
| Jiangmin | Win32/Pioneer.l |
| K7AntiVirus | Virus ( 00521e9a1 ) |
| K7GW | Virus ( 00521e9a1 ) |
| Kaspersky | Virus.Win32.Pioneer.cz |
| MAX | malware (ai score=85) |
| MaxSecure | Virus.W32.Pioneer.CZ |
| McAfee | Dropper-FIY!EA6B545D1B9A |
| McAfee-GW-Edition | BehavesLike.Win32.PUPXFF.cc |
| Microsoft | Virus:Win32/Floxif.H |
| MicroWorld-eScan | Win32.Floxif.A |
| NANO-Antivirus | Virus.Win32.Pioneer.bvrqhu |
| Panda | W32/Floxif.A |
| Qihoo-360 | Virus.Win32.Pioneer.C |
| Rising | Virus.Floxif!1.9BE6 (CLASSIC) |
| Sangfor | Malware |
| SentinelOne | DFI - Malicious PE |
| Sophos | W32/Floxif-C |
| Symantec | W32.Fixflo.B!inf |
| Tencent | Virus.Win32.Pionner.tt |
| TotalDefense | Win32/Flofix.D |
| TrendMicro | PE_FLOXIF.D |
| TrendMicro-HouseCall | PE_FLOXIF.D |
| VBA32 | Virus.Win32.Floxif.h |
| VIPRE | Virus.Win32.Floxif.a (v) |
| Zillya | Virus.Floxif.Win32.1 |
| ZoneAlarm | Virus.Win32.Pioneer.cz |
| Zoner | Virus.Win32.32881 |
Sandbox Report
The following information was gathered by executing the file inside Cuckoo Sandbox.
Summary
Successfully executed process in sandbox.
Summary
{
"file_created": [
"C:\\Program Files\\Common Files\\System\\symsrv.dll"
],
"regkey_written": [
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\EnableConsoleTracing",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\{E34DF837-3A38-4E8C-83F4-ABF8AB3FB4A6}\\WpadDecisionReason",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\{E34DF837-3A38-4E8C-83F4-ABF8AB3FB4A6}\\WpadDecision",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\{E34DF837-3A38-4E8C-83F4-ABF8AB3FB4A6}\\WpadNetworkName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\EnableFileTracing",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Connections\\DefaultConnectionSettings",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\MaxFileSize",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\FileTracingMask",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\{E34DF837-3A38-4E8C-83F4-ABF8AB3FB4A6}\\WpadDecisionTime",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\WpadLastNetwork",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\ConsoleTracingMask",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\FileDirectory",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Adobe\\Adobe ARM\\1.0\\ARM\\iLastSvcSuccess"
],
"dll_loaded": [
"C:\\Windows\\System32\\mswsock.dll",
"DNSAPI.dll",
"kernel32.dll",
"ntdll.dll",
"C:\\Windows\\system32\\napinsp.dll",
"API-MS-WIN-Service-Management-L1-1-0.dll",
"C:\\Program Files\\Common Files\\System\\symsrv.dll",
"KERNEL32.DLL",
"API-MS-WIN-Service-winsvc-L1-1-0.dll",
"advapi32.dll",
"ole32.dll",
"USER32.dll",
"API-MS-Win-Security-SDDL-L1-1-0.dll",
"RASMAN.DLL",
"rtutils.dll",
"IPHLPAPI.DLL",
"wininet.dll",
"WINTRUST.dll",
"ws2help.dll",
"OLEAUT32.dll",
"C:\\Windows\\system32\\pnrpnsp.dll",
"DHCPCSVC.DLL",
"C:\\Windows\\System32\\winrnr.dll",
"C:\\Windows\\system32\\NLAapi.dll",
"C:\\Windows\\SysWOW64\\oleaut32.dll",
"ADVAPI32.dll",
"WS2_32.dll"
],
"file_opened": [
"C:\\Program Files\\Common Files\\System\\symsrv.dll",
"C:\\Windows",
"C:\\Users\\cuck\\AppData\\Local\\Temp\\267228283c9f8311bcaa249810bd97926539c56f0fe0c7af4db16b15444bff0b.bin",
"C:\\Windows\\Globalization\\Sorting\\sortdefault.nls"
],
"regkey_opened": [
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\TreatAs",
"HKEY_LOCAL_MACHINE\\System\\CurrentControlSet\\Services\\DnsCache\\Parameters",
"HKEY_LOCAL_MACHINE\\Software\\Policies\\Microsoft\\Windows NT\\DnsClient",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{2A1C9EB2-DF62-4154-B800-63278FCB8037}\\ProxyStubClsid32",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows NT\\CurrentVersion\\ProfileList",
"HKEY_LOCAL_MACHINE\\Software\\Policies\\Microsoft\\Windows\\CurrentVersion\\Internet Settings",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Adobe\\Adobe ARM\\1.0\\ARM",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Tracing",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{26656EAA-54EB-4E6F-8F85-4F0EF901A406}\\ProxyStubClsid32",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Tracing\\RASMANCS",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\User Shell Folders",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\InprocServer32",
"HKEY_LOCAL_MACHINE\\SYSTEM\\CurrentControlSet\\Services\\crypt32",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\Progid",
"HKEY_CURRENT_USER\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\OleAut",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\{E34DF837-3A38-4E8C-83F4-ABF8AB3FB4A6}",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\InprocHandler32",
"HKEY_CURRENT_USER\\Software\\Microsoft\\windows\\CurrentVersion\\Internet Settings\\Connections",
"HKEY_CURRENT_USER\\Interface\\{2A1C9EB2-DF62-4154-B800-63278FCB8037}",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows NT\\CurrentVersion\\ProfileList\\S-1-5-21-699399860-4089948139-3198924279-1001",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\Progid",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{8A40A45D-055C-4B62-ABD7-6D613E2CEAEC}\\ProxyStubClsid32",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\InprocHandler",
"HKEY_LOCAL_MACHINE\\System\\CurrentControlSet\\Services\\Tcpip\\Parameters",
"HKEY_CURRENT_USER\\Software\\Microsoft\\windows\\CurrentVersion\\Internet Settings\\Wpad",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\msasn1",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{55272A00-42CB-11CE-8135-00AA004BB851}\\ProxyStubClsid32",
"HKEY_CURRENT_USER\\Interface\\{BCD1DE7E-2DB1-418B-B047-4A74E101F8C1}",
"HKEY_CURRENT_USER\\Interface\\{26656EAA-54EB-4E6F-8F85-4F0EF901A406}",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{BCD1DE7E-2DB1-418B-B047-4A74E101F8C1}\\ProxyStubClsid32",
"HKEY_LOCAL_MACHINE\\Software\\Policies\\Microsoft\\System\\DNSClient",
"HKEY_CURRENT_USER\\Interface\\{8A40A45D-055C-4B62-ABD7-6D613E2CEAEC}",
"HKEY_CURRENT_USER\\Interface\\{55272A00-42CB-11CE-8135-00AA004BB851}"
],
"resolves_host": [
"wpad",
"cuckpc"
],
"file_written": [
"C:\\Program Files\\Common Files\\System\\symsrv.dll"
],
"file_exists": [
"c:\\program files\\common files\\System\\symsrv.dll.dat",
"C:\\Users\\cuck\\AppData\\Local\\Temp\\267228283c9f8311bcaa249810bd97926539c56f0fe0c7af4db16b15444bff0b.bin.dat",
"C:\\Users\\cuck\\AppData\\Local\\Temp\\A1D26E2"
],
"mutex": [
"IESQMMUTEX_0_208"
],
"fetches_url": [
"http:\/\/5isohu.com\/logo.gif",
"http:\/\/www.aieov.com\/logo.gif"
],
"file_failed": [
"\\??\\d:"
],
"guid": [
"{a47979d2-c419-11d9-a5b4-001185ad2b89}",
"{dcb00c01-570f-4a9b-8d69-199fdba5723b}",
"{dcb00000-570f-4a9b-8d69-199fdba5723b}",
"{d0074ffd-570f-4a9b-8d69-199fdba5723b}"
],
"file_read": [
"C:\\Program Files\\Common Files\\System\\symsrv.dll",
"C:\\Users\\cuck\\AppData\\Local\\Temp\\267228283c9f8311bcaa249810bd97926539c56f0fe0c7af4db16b15444bff0b.bin"
],
"regkey_read": [
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{26656EAA-54EB-4E6F-8F85-4F0EF901A406}\\ProxyStubClsid32\\(Default)",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\EnableFileTracing",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\InprocServer32\\ThreadingModel",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASAPI32\\EnableConsoleTracing",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\EnableConsoleTracing",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\InprocServer32\\(Default)",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\User Shell Folders\\AppData",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\InprocServer32\\InprocServer32",
"HKEY_LOCAL_MACHINE\\SYSTEM\\ControlSet001\\Control\\Nls\\CustomLocale\\en-US",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{55272A00-42CB-11CE-8135-00AA004BB851}\\ProxyStubClsid32\\(Default)",
"HKEY_LOCAL_MACHINE\\SYSTEM\\ControlSet001\\services\\Tcpip\\Parameters\\Hostname",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{BCD1DE7E-2DB1-418B-B047-4A74E101F8C1}\\ProxyStubClsid32\\(Default)",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASAPI32\\FileDirectory",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\ProfileList\\ProgramData",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASAPI32\\FileTracingMask",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\AutoProxyDetectType",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{2A1C9EB2-DF62-4154-B800-63278FCB8037}\\ProxyStubClsid32\\(Default)",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASAPI32\\MaxFileSize",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{8A40A45D-055C-4B62-ABD7-6D613E2CEAEC}\\ProxyStubClsid32\\(Default)",
"HKEY_LOCAL_MACHINE\\SYSTEM\\ControlSet001\\services\\Tcpip\\Parameters\\Domain",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\DisableImprovedZoneCheck",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\FileTracingMask",
"HKEY_LOCAL_MACHINE\\SYSTEM\\ControlSet001\\Control\\Nls\\ExtendedLocale\\en-US",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\ConsoleTracingMask",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\FileDirectory",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Connections\\DefaultConnectionSettings",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASAPI32\\EnableFileTracing",
"HKEY_LOCAL_MACHINE\\SYSTEM\\ControlSet001\\services\\crypt32\\DebugHeapFlags",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\ProfileList\\S-1-5-21-699399860-4089948139-3198924279-1001\\ProfileImagePath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\MaxFileSize",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\WpadLastNetwork",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Policies\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Security_HKLM_only",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASAPI32\\ConsoleTracingMask",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\(Default)"
],
"directory_enumerated": [
"C:\\Users\\cuck\\AppData\\Roaming\\Microsoft\\Network\\Connections\\Pbk\\rasphone.pbk",
"C:\\ProgramData\\Microsoft\\Network\\Connections\\Pbk\\rasphone.pbk",
"C:\\Windows\\System32\\ras\\*.pbk",
"C:\\ProgramData\\Microsoft\\Network\\Connections\\Pbk\\*.pbk",
"C:\\Users\\cuck\\AppData\\Roaming\\Microsoft\\Network\\Connections\\Pbk\\*.pbk"
]
}Dropped
[
{
"yara": [],
"sha1": "14ba3fa927a06224dfe587014299e834def4644f",
"name": "de055a89de246e62_symsrv.dll",
"filepath": "C:\\Program Files\\Common Files\\System\\symsrv.dll",
"type": "PE32 executable (DLL) (GUI) Intel 80386, for MS Windows, UPX compressed",
"sha256": "de055a89de246e629a8694bde18af2b1605e4b9b493c7e4aef669dd67acf5085",
"urls": [],
"crc32": "B7C90DAE",
"path": "\/home\/hpuser\/.cuckoo\/storage\/analyses\/7365\/files\/de055a89de246e62_symsrv.dll",
"ssdeep": null,
"size": 69337,
"sha512": "4db19f2d8d5bc1c7bbb812d3fa9c43b80fa22140b346d2760f090b73aed8a5177edb4bddc647a6ebd5a2db8565be5a1a36a602b0d759e38540d9a584ba5896ab",
"pids": [
1512
],
"md5": "7574cf2c64f35161ab1292e2f532aabf"
}
]Generic
[
{
"process_path": "C:\\Users\\cuck\\AppData\\Local\\Temp\\267228283c9f8311bcaa249810bd97926539c56f0fe0c7af4db16b15444bff0b.bin",
"process_name": "267228283c9f8311bcaa249810bd97926539c56f0fe0c7af4db16b15444bff0b.bin",
"pid": 1512,
"summary": {
"file_created": [
"C:\\Program Files\\Common Files\\System\\symsrv.dll"
],
"regkey_written": [
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\EnableConsoleTracing",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\{E34DF837-3A38-4E8C-83F4-ABF8AB3FB4A6}\\WpadDecisionReason",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\{E34DF837-3A38-4E8C-83F4-ABF8AB3FB4A6}\\WpadDecision",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\{E34DF837-3A38-4E8C-83F4-ABF8AB3FB4A6}\\WpadNetworkName",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\EnableFileTracing",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Connections\\DefaultConnectionSettings",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\MaxFileSize",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\FileTracingMask",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\{E34DF837-3A38-4E8C-83F4-ABF8AB3FB4A6}\\WpadDecisionTime",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\WpadLastNetwork",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\ConsoleTracingMask",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\FileDirectory",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Adobe\\Adobe ARM\\1.0\\ARM\\iLastSvcSuccess"
],
"dll_loaded": [
"C:\\Windows\\System32\\mswsock.dll",
"DNSAPI.dll",
"kernel32.dll",
"ntdll.dll",
"C:\\Windows\\system32\\napinsp.dll",
"API-MS-WIN-Service-Management-L1-1-0.dll",
"C:\\Program Files\\Common Files\\System\\symsrv.dll",
"KERNEL32.DLL",
"API-MS-WIN-Service-winsvc-L1-1-0.dll",
"advapi32.dll",
"ole32.dll",
"USER32.dll",
"API-MS-Win-Security-SDDL-L1-1-0.dll",
"RASMAN.DLL",
"rtutils.dll",
"IPHLPAPI.DLL",
"wininet.dll",
"WINTRUST.dll",
"ws2help.dll",
"OLEAUT32.dll",
"C:\\Windows\\system32\\pnrpnsp.dll",
"DHCPCSVC.DLL",
"C:\\Windows\\System32\\winrnr.dll",
"C:\\Windows\\system32\\NLAapi.dll",
"C:\\Windows\\SysWOW64\\oleaut32.dll",
"ADVAPI32.dll",
"WS2_32.dll"
],
"file_opened": [
"C:\\Program Files\\Common Files\\System\\symsrv.dll",
"C:\\Windows",
"C:\\Users\\cuck\\AppData\\Local\\Temp\\267228283c9f8311bcaa249810bd97926539c56f0fe0c7af4db16b15444bff0b.bin",
"C:\\Windows\\Globalization\\Sorting\\sortdefault.nls"
],
"regkey_opened": [
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\TreatAs",
"HKEY_LOCAL_MACHINE\\System\\CurrentControlSet\\Services\\DnsCache\\Parameters",
"HKEY_LOCAL_MACHINE\\Software\\Policies\\Microsoft\\Windows NT\\DnsClient",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{2A1C9EB2-DF62-4154-B800-63278FCB8037}\\ProxyStubClsid32",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows NT\\CurrentVersion\\ProfileList",
"HKEY_LOCAL_MACHINE\\Software\\Policies\\Microsoft\\Windows\\CurrentVersion\\Internet Settings",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Adobe\\Adobe ARM\\1.0\\ARM",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Tracing",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{26656EAA-54EB-4E6F-8F85-4F0EF901A406}\\ProxyStubClsid32",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Tracing\\RASMANCS",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\User Shell Folders",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\InprocServer32",
"HKEY_LOCAL_MACHINE\\SYSTEM\\CurrentControlSet\\Services\\crypt32",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\Progid",
"HKEY_CURRENT_USER\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\OleAut",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\{E34DF837-3A38-4E8C-83F4-ABF8AB3FB4A6}",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\InprocHandler32",
"HKEY_CURRENT_USER\\Software\\Microsoft\\windows\\CurrentVersion\\Internet Settings\\Connections",
"HKEY_CURRENT_USER\\Interface\\{2A1C9EB2-DF62-4154-B800-63278FCB8037}",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\Windows NT\\CurrentVersion\\ProfileList\\S-1-5-21-699399860-4089948139-3198924279-1001",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\Progid",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{8A40A45D-055C-4B62-ABD7-6D613E2CEAEC}\\ProxyStubClsid32",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\InprocHandler",
"HKEY_LOCAL_MACHINE\\System\\CurrentControlSet\\Services\\Tcpip\\Parameters",
"HKEY_CURRENT_USER\\Software\\Microsoft\\windows\\CurrentVersion\\Internet Settings\\Wpad",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\msasn1",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{55272A00-42CB-11CE-8135-00AA004BB851}\\ProxyStubClsid32",
"HKEY_CURRENT_USER\\Interface\\{BCD1DE7E-2DB1-418B-B047-4A74E101F8C1}",
"HKEY_CURRENT_USER\\Interface\\{26656EAA-54EB-4E6F-8F85-4F0EF901A406}",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{BCD1DE7E-2DB1-418B-B047-4A74E101F8C1}\\ProxyStubClsid32",
"HKEY_LOCAL_MACHINE\\Software\\Policies\\Microsoft\\System\\DNSClient",
"HKEY_CURRENT_USER\\Interface\\{8A40A45D-055C-4B62-ABD7-6D613E2CEAEC}",
"HKEY_CURRENT_USER\\Interface\\{55272A00-42CB-11CE-8135-00AA004BB851}"
],
"resolves_host": [
"wpad",
"cuckpc"
],
"file_written": [
"C:\\Program Files\\Common Files\\System\\symsrv.dll"
],
"file_exists": [
"c:\\program files\\common files\\System\\symsrv.dll.dat",
"C:\\Users\\cuck\\AppData\\Local\\Temp\\267228283c9f8311bcaa249810bd97926539c56f0fe0c7af4db16b15444bff0b.bin.dat",
"C:\\Users\\cuck\\AppData\\Local\\Temp\\A1D26E2"
],
"mutex": [
"IESQMMUTEX_0_208"
],
"fetches_url": [
"http:\/\/5isohu.com\/logo.gif",
"http:\/\/www.aieov.com\/logo.gif"
],
"file_failed": [
"\\??\\d:"
],
"guid": [
"{a47979d2-c419-11d9-a5b4-001185ad2b89}",
"{dcb00c01-570f-4a9b-8d69-199fdba5723b}",
"{dcb00000-570f-4a9b-8d69-199fdba5723b}",
"{d0074ffd-570f-4a9b-8d69-199fdba5723b}"
],
"file_read": [
"C:\\Program Files\\Common Files\\System\\symsrv.dll",
"C:\\Users\\cuck\\AppData\\Local\\Temp\\267228283c9f8311bcaa249810bd97926539c56f0fe0c7af4db16b15444bff0b.bin"
],
"regkey_read": [
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{26656EAA-54EB-4E6F-8F85-4F0EF901A406}\\ProxyStubClsid32\\(Default)",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\EnableFileTracing",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\InprocServer32\\ThreadingModel",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASAPI32\\EnableConsoleTracing",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\EnableConsoleTracing",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\InprocServer32\\(Default)",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\User Shell Folders\\AppData",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\InprocServer32\\InprocServer32",
"HKEY_LOCAL_MACHINE\\SYSTEM\\ControlSet001\\Control\\Nls\\CustomLocale\\en-US",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{55272A00-42CB-11CE-8135-00AA004BB851}\\ProxyStubClsid32\\(Default)",
"HKEY_LOCAL_MACHINE\\SYSTEM\\ControlSet001\\services\\Tcpip\\Parameters\\Hostname",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{BCD1DE7E-2DB1-418B-B047-4A74E101F8C1}\\ProxyStubClsid32\\(Default)",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASAPI32\\FileDirectory",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\ProfileList\\ProgramData",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASAPI32\\FileTracingMask",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\AutoProxyDetectType",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{2A1C9EB2-DF62-4154-B800-63278FCB8037}\\ProxyStubClsid32\\(Default)",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASAPI32\\MaxFileSize",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\Interface\\{8A40A45D-055C-4B62-ABD7-6D613E2CEAEC}\\ProxyStubClsid32\\(Default)",
"HKEY_LOCAL_MACHINE\\SYSTEM\\ControlSet001\\services\\Tcpip\\Parameters\\Domain",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\DisableImprovedZoneCheck",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\FileTracingMask",
"HKEY_LOCAL_MACHINE\\SYSTEM\\ControlSet001\\Control\\Nls\\ExtendedLocale\\en-US",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\ConsoleTracingMask",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\FileDirectory",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Connections\\DefaultConnectionSettings",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASAPI32\\EnableFileTracing",
"HKEY_LOCAL_MACHINE\\SYSTEM\\ControlSet001\\services\\crypt32\\DebugHeapFlags",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\ProfileList\\S-1-5-21-699399860-4089948139-3198924279-1001\\ProfileImagePath",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASMANCS\\MaxFileSize",
"HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\WpadLastNetwork",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Policies\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Security_HKLM_only",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Tracing\\RASAPI32\\ConsoleTracingMask",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Classes\\Wow6432Node\\CLSID\\{B196B286-BAB4-101A-B69C-00AA00341D07}\\(Default)"
],
"directory_enumerated": [
"C:\\Users\\cuck\\AppData\\Roaming\\Microsoft\\Network\\Connections\\Pbk\\rasphone.pbk",
"C:\\ProgramData\\Microsoft\\Network\\Connections\\Pbk\\rasphone.pbk",
"C:\\Windows\\System32\\ras\\*.pbk",
"C:\\ProgramData\\Microsoft\\Network\\Connections\\Pbk\\*.pbk",
"C:\\Users\\cuck\\AppData\\Roaming\\Microsoft\\Network\\Connections\\Pbk\\*.pbk"
]
},
"first_seen": 1588805585.5625,
"ppid": 2892
},
{
"process_path": "C:\\Windows\\System32\\lsass.exe",
"process_name": "lsass.exe",
"pid": 476,
"summary": {},
"first_seen": 1588805585.3125,
"ppid": 376
}
]Signatures
[
{
"markcount": 1,
"families": [],
"description": "This executable has a PDB path",
"severity": 1,
"marks": [
{
"category": "pdb_path",
"ioc": "D:\\CB\\ARM_Main\\BuildResults\\bin\\Win32\\Release\\armsvc.pdb",
"type": "ioc",
"description": null
}
],
"references": [],
"name": "has_pdb"
},
{
"markcount": 1,
"families": [],
"description": "The file contains an unknown PE resource name possibly indicative of a packer",
"severity": 1,
"marks": [
{
"category": "resource name",
"ioc": "REGISTRY",
"type": "ioc",
"description": null
}
],
"references": [],
"name": "pe_unknown_resource_name"
},
{
"markcount": 1,
"families": [],
"description": "One or more processes crashed",
"severity": 1,
"marks": [
{
"call": {
"category": "__notification__",
"status": 1,
"stacktrace": [],
"raw": [
"stacktrace"
],
"api": "__exception__",
"return_value": 0,
"arguments": {
"stacktrace": "c\nr\nc\n3\n2\n+\n0\nx\nb\n3\n5\n3\n \nF\nl\no\no\nd\nF\ni\nx\n-\n0\nx\na\nd\nb\n \ns\ny\nm\ns\nr\nv\n+\n0\nx\nc\n9\nb\n0\n \n@\n \n0\nx\n1\n0\n0\n0\nc\n9\nb\n0\n\n\nF\nl\no\no\nd\nF\ni\nx\n2\n+\n0\nx\n4\n7\n2\nc\n \ns\ny\nm\ns\nr\nv\n+\n0\nx\n1\n1\ne\n5\n4\n \n@\n \n0\nx\n1\n0\n0\n1\n1\ne\n5\n4\n\n\nB\na\ns\ne\nT\nh\nr\ne\na\nd\nI\nn\ni\nt\nT\nh\nu\nn\nk\n+\n0\nx\n1\n2\n \nV\ne\nr\ni\nf\ny\nC\no\nn\ns\no\nl\ne\nI\no\nH\na\nn\nd\nl\ne\n-\n0\nx\nb\n3\n \nk\ne\nr\nn\ne\nl\n3\n2\n+\n0\nx\n1\n3\n3\nc\na\n \n@\n \n0\nx\n7\n5\nb\nc\n3\n3\nc\na\n\n\nR\nt\nl\nI\nn\ni\nt\ni\na\nl\ni\nz\ne\nE\nx\nc\ne\np\nt\ni\no\nn\nC\nh\na\ni\nn\n+\n0\nx\n6\n3\n \nR\nt\nl\nA\nl\nl\no\nc\na\nt\ne\nA\nc\nt\ni\nv\na\nt\ni\no\nn\nC\no\nn\nt\ne\nx\nt\nS\nt\na\nc\nk\n-\n0\nx\na\n1\n \nn\nt\nd\nl\nl\n+\n0\nx\n3\n9\ne\nd\n2\n \n@\n \n0\nx\n7\n7\nb\nc\n9\ne\nd\n2\n\n\nR\nt\nl\nI\nn\ni\nt\ni\na\nl\ni\nz\ne\nE\nx\nc\ne\np\nt\ni\no\nn\nC\nh\na\ni\nn\n+\n0\nx\n3\n6\n \nR\nt\nl\nA\nl\nl\no\nc\na\nt\ne\nA\nc\nt\ni\nv\na\nt\ni\no\nn\nC\no\nn\nt\ne\nx\nt\nS\nt\na\nc\nk\n-\n0\nx\nc\ne\n \nn\nt\nd\nl\nl\n+\n0\nx\n3\n9\ne\na\n5\n \n@\n \n0\nx\n7\n7\nb\nc\n9\ne\na\n5",
"registers": {
"esp": 13368248,
"edi": 1447909480,
"eax": 1447909480,
"ebp": 13368308,
"edx": 22104,
"ebx": 0,
"esi": 22104,
"ecx": 10
},
"exception": {
"instruction_r": "ed 3b df 0f 94 45 e4 5e 5f 5a 59 5b c7 45 fc ff",
"instruction": "in eax, dx",
"exception_code": "0xc0000096",
"symbol": "crc32+0x1e34 FloodFix-0x9ffa symsrv+0x3491",
"address": "0x10003491"
}
},
"time": 1588805585.8755,
"tid": 2588,
"flags": {}
},
"pid": 1512,
"type": "call",
"cid": 2897
}
],
"references": [],
"name": "raises_exception"
},
{
"markcount": 0,
"families": [],
"description": "One or more potentially interesting buffers were extracted, these generally contain injected code, configuration data, etc.",
"severity": 2,
"marks": [],
"references": [],
"name": "dumped_buffer"
},
{
"markcount": 1355,
"families": [],
"description": "Allocates read-write-execute memory (usually to unpack itself)",
"severity": 2,
"marks": [
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f28000"
},
"time": 1588805585.7655,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 19
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f20000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 191
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 12288,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f26000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 193
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 195
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 197
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 199
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 201
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 203
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 205
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 207
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 209
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 211
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 213
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 215
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 217
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 219
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 221
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 223
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 225
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 227
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 229
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 231
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 233
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 235
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 237
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 239
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 241
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 243
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 245
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 247
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 249
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 251
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 253
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 255
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 257
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 259
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 261
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 263
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 265
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8125,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 267
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8285,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 269
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8285,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 271
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8285,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 273
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8285,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 275
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8285,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 277
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8285,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 279
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8285,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 281
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8285,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 283
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8285,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 285
},
{
"call": {
"category": "process",
"status": 1,
"stacktrace": [],
"api": "NtProtectVirtualMemory",
"return_value": 0,
"arguments": {
"process_identifier": 1512,
"stack_dep_bypass": 0,
"stack_pivoted": 0,
"heap_dep_bypass": 0,
"length": 4096,
"protection": 64,
"process_handle": "0xffffffff",
"base_address": "0x00f21000"
},
"time": 1588805585.8285,
"tid": 2732,
"flags": {
"protection": "PAGE_EXECUTE_READWRITE"
}
},
"pid": 1512,
"type": "call",
"cid": 287
}
],
"references": [],
"name": "allocates_rwx"
},
{
"markcount": 1,
"families": [],
"description": "Checks adapter addresses which can be used to detect virtual network interfaces",
"severity": 2,
"marks": [
{
"call": {
"category": "network",
"status": 0,
"stacktrace": [],
"last_error": 0,
"nt_status": -1073741772,
"api": "GetAdaptersAddresses",
"return_value": 111,
"arguments": {
"flags": 0,
"family": 0
},
"time": 1588805587.8755,
"tid": 460,
"flags": {}
},
"pid": 1512,
"type": "call",
"cid": 3566
}
],
"references": [],
"name": "antivm_network_adapters"
},
{
"markcount": 1,
"families": [],
"description": "Checks for the Locally Unique Identifier on the system for a suspicious privilege",
"severity": 2,
"marks": [
{
"call": {
"category": "system",
"status": 1,
"stacktrace": [],
"api": "LookupPrivilegeValueW",
"return_value": 1,
"arguments": {
"system_name": "",
"privilege_name": "SeDebugPrivilege"
},
"time": 1588805585.8755,
"tid": 2588,
"flags": {}
},
"pid": 1512,
"type": "call",
"cid": 2906
}
],
"references": [],
"name": "privilege_luid_check"
},
{
"markcount": 5,
"families": [],
"description": "Sets or modifies WPAD proxy autoconfiguration file for traffic interception",
"severity": 3,
"marks": [
{
"call": {
"category": "registry",
"status": 1,
"stacktrace": [],
"api": "RegSetValueExA",
"return_value": 0,
"arguments": {
"key_handle": "0x00000320",
"value": 1,
"regkey_r": "WpadDecisionReason",
"reg_type": 4,
"regkey": "HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\{E34DF837-3A38-4E8C-83F4-ABF8AB3FB4A6}\\WpadDecisionReason"
},
"time": 1588805590.6565,
"tid": 460,
"flags": {
"reg_type": "REG_DWORD"
}
},
"pid": 1512,
"type": "call",
"cid": 3579
},
{
"call": {
"category": "registry",
"status": 1,
"stacktrace": [],
"api": "RegSetValueExA",
"return_value": 0,
"arguments": {
"key_handle": "0x00000320",
"value": "\u00f0\u00f8\u0006C\u0012$\u00d6\u0001",
"regkey_r": "WpadDecisionTime",
"reg_type": 3,
"regkey": "HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\{E34DF837-3A38-4E8C-83F4-ABF8AB3FB4A6}\\WpadDecisionTime"
},
"time": 1588805590.6565,
"tid": 460,
"flags": {
"reg_type": "REG_BINARY"
}
},
"pid": 1512,
"type": "call",
"cid": 3580
},
{
"call": {
"category": "registry",
"status": 1,
"stacktrace": [],
"api": "RegSetValueExA",
"return_value": 0,
"arguments": {
"key_handle": "0x00000320",
"value": 3,
"regkey_r": "WpadDecision",
"reg_type": 4,
"regkey": "HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\{E34DF837-3A38-4E8C-83F4-ABF8AB3FB4A6}\\WpadDecision"
},
"time": 1588805590.6565,
"tid": 460,
"flags": {
"reg_type": "REG_DWORD"
}
},
"pid": 1512,
"type": "call",
"cid": 3581
},
{
"call": {
"category": "registry",
"status": 1,
"stacktrace": [],
"api": "RegSetValueExW",
"return_value": 0,
"arguments": {
"key_handle": "0x00000320",
"value": "Unidentified network",
"regkey_r": "WpadNetworkName",
"reg_type": 1,
"regkey": "HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\{E34DF837-3A38-4E8C-83F4-ABF8AB3FB4A6}\\WpadNetworkName"
},
"time": 1588805590.6565,
"tid": 460,
"flags": {
"reg_type": "REG_SZ"
}
},
"pid": 1512,
"type": "call",
"cid": 3582
},
{
"call": {
"category": "registry",
"status": 1,
"stacktrace": [],
"api": "RegSetValueExW",
"return_value": 0,
"arguments": {
"key_handle": "0x0000031c",
"value": "{E34DF837-3A38-4E8C-83F4-ABF8AB3FB4A6}",
"regkey_r": "WpadLastNetwork",
"reg_type": 1,
"regkey": "HKEY_CURRENT_USER\\Software\\Microsoft\\Windows\\CurrentVersion\\Internet Settings\\Wpad\\WpadLastNetwork"
},
"time": 1588805590.8435,
"tid": 460,
"flags": {
"reg_type": "REG_SZ"
}
},
"pid": 1512,
"type": "call",
"cid": 3650
}
],
"references": [],
"name": "modifies_proxy_wpad"
},
{
"markcount": 1,
"families": [],
"description": "Detects VMWare through the in instruction feature",
"severity": 3,
"marks": [
{
"call": {
"category": "__notification__",
"status": 1,
"stacktrace": [],
"raw": [
"stacktrace"
],
"api": "__exception__",
"return_value": 0,
"arguments": {
"stacktrace": "c\nr\nc\n3\n2\n+\n0\nx\nb\n3\n5\n3\n \nF\nl\no\no\nd\nF\ni\nx\n-\n0\nx\na\nd\nb\n \ns\ny\nm\ns\nr\nv\n+\n0\nx\nc\n9\nb\n0\n \n@\n \n0\nx\n1\n0\n0\n0\nc\n9\nb\n0\n\n\nF\nl\no\no\nd\nF\ni\nx\n2\n+\n0\nx\n4\n7\n2\nc\n \ns\ny\nm\ns\nr\nv\n+\n0\nx\n1\n1\ne\n5\n4\n \n@\n \n0\nx\n1\n0\n0\n1\n1\ne\n5\n4\n\n\nB\na\ns\ne\nT\nh\nr\ne\na\nd\nI\nn\ni\nt\nT\nh\nu\nn\nk\n+\n0\nx\n1\n2\n \nV\ne\nr\ni\nf\ny\nC\no\nn\ns\no\nl\ne\nI\no\nH\na\nn\nd\nl\ne\n-\n0\nx\nb\n3\n \nk\ne\nr\nn\ne\nl\n3\n2\n+\n0\nx\n1\n3\n3\nc\na\n \n@\n \n0\nx\n7\n5\nb\nc\n3\n3\nc\na\n\n\nR\nt\nl\nI\nn\ni\nt\ni\na\nl\ni\nz\ne\nE\nx\nc\ne\np\nt\ni\no\nn\nC\nh\na\ni\nn\n+\n0\nx\n6\n3\n \nR\nt\nl\nA\nl\nl\no\nc\na\nt\ne\nA\nc\nt\ni\nv\na\nt\ni\no\nn\nC\no\nn\nt\ne\nx\nt\nS\nt\na\nc\nk\n-\n0\nx\na\n1\n \nn\nt\nd\nl\nl\n+\n0\nx\n3\n9\ne\nd\n2\n \n@\n \n0\nx\n7\n7\nb\nc\n9\ne\nd\n2\n\n\nR\nt\nl\nI\nn\ni\nt\ni\na\nl\ni\nz\ne\nE\nx\nc\ne\np\nt\ni\no\nn\nC\nh\na\ni\nn\n+\n0\nx\n3\n6\n \nR\nt\nl\nA\nl\nl\no\nc\na\nt\ne\nA\nc\nt\ni\nv\na\nt\ni\no\nn\nC\no\nn\nt\ne\nx\nt\nS\nt\na\nc\nk\n-\n0\nx\nc\ne\n \nn\nt\nd\nl\nl\n+\n0\nx\n3\n9\ne\na\n5\n \n@\n \n0\nx\n7\n7\nb\nc\n9\ne\na\n5",
"registers": {
"esp": 13368248,
"edi": 1447909480,
"eax": 1447909480,
"ebp": 13368308,
"edx": 22104,
"ebx": 0,
"esi": 22104,
"ecx": 10
},
"exception": {
"instruction_r": "ed 3b df 0f 94 45 e4 5e 5f 5a 59 5b c7 45 fc ff",
"instruction": "in eax, dx",
"exception_code": "0xc0000096",
"symbol": "crc32+0x1e34 FloodFix-0x9ffa symsrv+0x3491",
"address": "0x10003491"
}
},
"time": 1588805585.8755,
"tid": 2588,
"flags": {}
},
"pid": 1512,
"type": "call",
"cid": 2897
}
],
"references": [],
"name": "antivm_vmware_in_instruction"
}
]Yara
The Yara rules did not detect anything in the file.
Network
{
"tls": [],
"udp": [
{
"src": "192.168.56.101",
"dst": "192.168.56.255",
"offset": 662,
"time": 6.252233028411865,
"dport": 137,
"sport": 137
},
{
"src": "192.168.56.101",
"dst": "192.168.56.255",
"offset": 15062,
"time": 12.328272104263306,
"dport": 138,
"sport": 138
},
{
"src": "192.168.56.101",
"dst": "224.0.0.252",
"offset": 16906,
"time": 6.159562110900879,
"dport": 5355,
"sport": 51001
},
{
"src": "192.168.56.101",
"dst": "224.0.0.252",
"offset": 17234,
"time": 4.142266035079956,
"dport": 5355,
"sport": 53595
},
{
"src": "192.168.56.101",
"dst": "224.0.0.252",
"offset": 17562,
"time": 6.204972982406616,
"dport": 5355,
"sport": 53848
},
{
"src": "192.168.56.101",
"dst": "224.0.0.252",
"offset": 17890,
"time": 4.643604040145874,
"dport": 5355,
"sport": 54255
},
{
"src": "192.168.56.101",
"dst": "224.0.0.252",
"offset": 18218,
"time": 3.0242719650268555,
"dport": 5355,
"sport": 55314
},
{
"src": "192.168.56.101",
"dst": "224.0.0.252",
"offset": 18546,
"time": 7.173439025878906,
"dport": 5355,
"sport": 55880
},
{
"src": "192.168.56.101",
"dst": "239.255.255.250",
"offset": 18866,
"time": 4.673733949661255,
"dport": 1900,
"sport": 1900
},
{
"src": "192.168.56.101",
"dst": "239.255.255.250",
"offset": 38276,
"time": 4.173293113708496,
"dport": 3702,
"sport": 49152
},
{
"src": "192.168.56.101",
"dst": "239.255.255.250",
"offset": 46660,
"time": 6.254003047943115,
"dport": 1900,
"sport": 53598
}
],
"dns_servers": [],
"http": [],
"icmp": [],
"smtp": [],
"tcp": [],
"smtp_ex": [],
"mitm": [],
"hosts": [],
"pcap_sha256": "2b1d04d52bfd6f7bf4b621dc1ff07a15ff52093b6bafbbf723233c4c37d74841",
"dns": [],
"http_ex": [],
"domains": [],
"dead_hosts": [],
"sorted_pcap_sha256": "07783458ac5986562b2d9f0f0caca4b925e7b158c081ff637b0b0689898ec25f",
"irc": [],
"https_ex": []
}Screenshots





armsvc.exe removal instructions
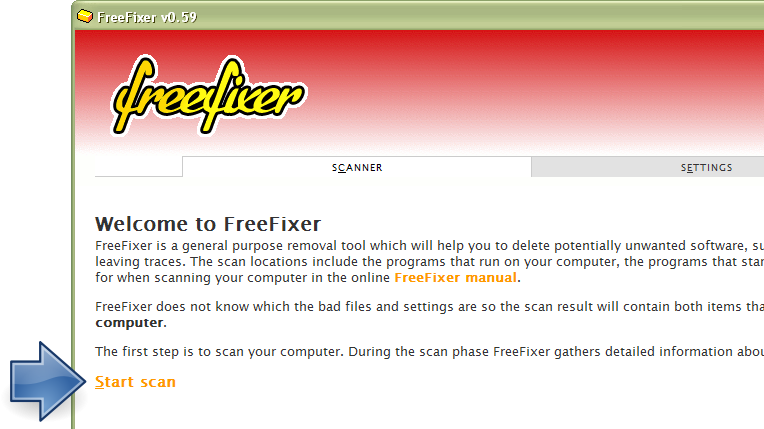
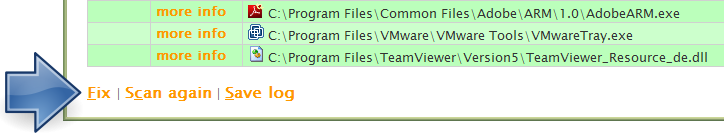
The instructions below shows how to remove armsvc.exe with help from the FreeFixer removal tool. Basically, you install FreeFixer, scan your computer, check the armsvc.exe file for removal, restart your computer and scan it again to verify that armsvc.exe has been successfully removed. Here are the removal instructions in more detail:
- Download and install FreeFixer: http://www.freefixer.com/download.html
- When the scan is finished, locate armsvc.exe in the scan result and tick the checkbox next to the armsvc.exe file. Do not check any other file for removal unless you are 100% sure you want to delete it. Tip: Press CTRL-F to open up FreeFixer's search dialog to quickly locate armsvc.exe in the scan result.


 c:\program files (x86)\common files\adobe\arm\1.0\armsvc.exe
c:\program files (x86)\common files\adobe\arm\1.0\armsvc.exe 
- Restart your computer.
- Start FreeFixer and scan your computer again. If armsvc.exe still remains in the scan result, proceed with the next step. If armsvc.exe is gone from the scan result you're done.
- If armsvc.exe still remains in the scan result, check its checkbox again in the scan result and click Fix.
- Restart your computer.
- Start FreeFixer and scan your computer again. Verify that armsvc.exe no longer appear in the scan result.
Other files also named armsvc.exe
armsvc.exe (79 votes)
Hashes [?]
| Property | Value |
|---|---|
| MD5 | ea6b545d1b9a14d58ba2ce7ef7d04a3f |
| SHA256 | 267228283c9f8311bcaa249810bd97926539c56f0fe0c7af4db16b15444bff0b |
Error Messages
These are some of the error messages that can appear related to armsvc.exe:
armsvc.exe has encountered a problem and needs to close. We are sorry for the inconvenience.
armsvc.exe - Application Error. The instruction at "0xXXXXXXXX" referenced memory at "0xXXXXXXXX". The memory could not be "read/written". Click on OK to terminate the program.
Adobe Acrobat Update Service has stopped working.
End Program - armsvc.exe. This program is not responding.
armsvc.exe is not a valid Win32 application.
armsvc.exe - Application Error. The application failed to initialize properly (0xXXXXXXXX). Click OK to terminate the application.
What will you do with armsvc.exe?
To help other users, please let us know what you will do with armsvc.exe:
What did other users do?
The poll result listed below shows what users chose to do with armsvc.exe. 73% have voted for removal. Based on votes from 11 users.
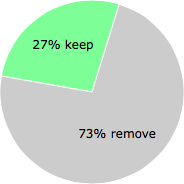
NOTE: Please do not use this poll as the only source of input to determine what you will do with armsvc.exe. Only 11 users has voted so far so it does not offer a high degree of confidence.
Comments
Please share with the other users what you think about this file. What does this file do? Is it legitimate or something that your computer is better without? Do you know how it was installed on your system? Did you install it yourself or did it come bundled with some other software? Is it running smoothly or do you get some error message? Any information that will help to document this file is welcome. Thank you for your contributions.
I'm reading all new comments so don't hesitate to post a question about the file. If I don't have the answer perhaps another user can help you.
No comments posted yet.