What is clientc.exe?
clientc.exe is part of Camtasia and developed by TechSmith Corporation according to the clientc.exe version information.
clientc.exe's description is "CamtasiaStudio.exe"
clientc.exe is usually located in the 'c:\downloads\' folder.
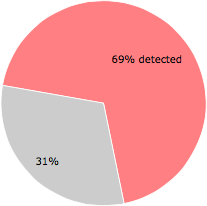
Some of the anti-virus scanners at VirusTotal detected clientc.exe.
If you have additional information about the file, please share it with the FreeFixer users by posting a comment at the bottom of this page.
Vendor and version information [?]
The following is the available information on clientc.exe:
| Property | Value |
|---|---|
| Product name | Camtasia |
| Company name | TechSmith Corporation |
| File description | CamtasiaStudio.exe |
| Internal name | Crypted.exe |
| Original filename | Crypted.exe |
| Comments | TechSmith Camtasia 2018 |
| Legal copyright | Copyright © 2011-2019 TechSmith Corporation. All rights reserved. |
| Legal trademark | 18 |
| Product version | 0.1.31.0 |
| File version | 0.1.31.0 |
Here's a screenshot of the file properties when displayed by Windows Explorer:
| Product name | Camtasia |
| Company name | TechSmith Corporation |
| File description | CamtasiaStudio.exe |
| Internal name | Crypted.exe |
| Original filename | Crypted.exe |
| Comments | TechSmith Camtasia 2018 |
| Legal copyright | Copyright © 2011-2019 TechSmith Cor.. |
| Legal trademark | 18 |
| Product version | 0.1.31.0 |
| File version | 0.1.31.0 |
Digital signatures [?]
clientc.exe is not signed.
VirusTotal report
49 of the 71 anti-virus programs at VirusTotal detected the clientc.exe file. That's a 69% detection rate.
| Scanner | Detection Name |
|---|---|
| Acronis | suspicious |
| Ad-Aware | Gen:Variant.Razy.412481 |
| AhnLab-V3 | Malware/Gen.Generic.C3035987 |
| ALYac | Gen:Variant.Razy.412481 |
| Antiy-AVL | Trojan/MSIL.Tasker |
| Arcabit | Trojan.Razy.D64B41 |
| Avast | Win32:Trojan-gen |
| AVG | Win32:Trojan-gen |
| Avira | TR/Dropper.Gen |
| BitDefender | Gen:Variant.Razy.412481 |
| Comodo | Malware@#1tvw005krihki |
| CrowdStrike | win/malicious_confidence_100% (W) |
| Cybereason | malicious.8cf9bf |
| Cylance | Unsafe |
| Cyren | W32/MSIL_Troj.PK.gen!Eldorado |
| DrWeb | Trojan.Siggen7.63254 |
| Emsisoft | Gen:Variant.Razy.412481 (B) |
| Endgame | malicious (moderate confidence) |
| ESET-NOD32 | MSIL/Agent.BPK |
| F-Prot | W32/MSIL_Troj.PK.gen!Eldorado |
| F-Secure | Trojan.TR/Dropper.Gen |
| Fortinet | MSIL/GenKryptik.CQSD!tr |
| GData | Gen:Variant.Razy.412481 |
| Ikarus | Trojan.MSIL.Krypt |
| Invincea | heuristic |
| K7AntiVirus | Trojan ( 004dcb4e1 ) |
| K7GW | Trojan ( 004dcb4e1 ) |
| Kaspersky | HEUR:Trojan.MSIL.Tasker.gen |
| Malwarebytes | Trojan.Crypt.MSIL.Generic |
| McAfee | RDN/Generic.dx |
| McAfee-GW-Edition | BehavesLike.Win32.Generic.qc |
| Microsoft | Trojan:Win32/Occamy.C |
| MicroWorld-eScan | Gen:Variant.Razy.412481 |
| NANO-Antivirus | Trojan.Win32.Tasker.fnisoi |
| Paloalto | generic.ml |
| Panda | Trj/GdSda.A |
| Qihoo-360 | Trojan.Generic |
| Rising | Dropper.Generic!8.35E (CLOUD) |
| SentinelOne | static engine - malicious |
| Sophos | Mal/Generic-S |
| Symantec | Trojan.Gen.MBT |
| Tencent | Msil.Trojan.Tasker.Bnn |
| Trapmine | suspicious.low.ml.score |
| TrendMicro | TROJ_GEN.R002C0WBM19 |
| TrendMicro-HouseCall | TROJ_GEN.R002C0WBM19 |
| VBA32 | TScope.Trojan.MSIL |
| VIPRE | Trojan.Win32.Generic!BT |
| Yandex | Trojan.Tasker! |
| ZoneAlarm | HEUR:Trojan.MSIL.Tasker.gen |
Sandbox Report
The following information was gathered by executing the file inside Cuckoo Sandbox.
Summary
Successfully executed process in sandbox.
Summary
{
"dll_loaded": [
"ADVAPI32.dll",
"SHLWAPI.dll",
"C:\\Windows\\system32\\IMM32.DLL",
"gdi32.dll"
],
"file_failed": [
"C:\\Users\\cuck\\AppData\\Local\\Temp\\34d54fc11ec26dc3645995c8cad58d22976293e6af1ec3789cfab640ace146b4.bin.config"
],
"regkey_opened": [
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\.NETFramework\\Policy\\Upgrades",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\.NETFramework\\Policy\\Upgrades",
"HKEY_CURRENT_USER\\Software\\Microsoft\\.NETFramework\\Policy\\Standards",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\.NETFramework\\Policy\\Standards\\v4.0.30319",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\.NETFramework",
"HKEY_CURRENT_USER\\Software\\Microsoft\\.NETFramework",
"HKEY_CURRENT_USER\\Software\\Microsoft\\.NETFramework\\Policy\\Upgrades",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\.NETFramework\\Policy\\",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\.NETFramework\\Policy\\Standards",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\.NETFramework\\Policy\\AppPatch",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\.NETFramework\\Policy\\v2.0",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\.NETFramework\\Policy\\Standards"
],
"file_exists": [
"C:\\Windows\\System32\\MSCOREE.DLL.local"
],
"file_opened": [
"C:\\Users\\cuck\\AppData\\Local\\Temp\\34d54fc11ec26dc3645995c8cad58d22976293e6af1ec3789cfab640ace146b4.bin"
],
"regkey_read": [
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\.NETFramework\\NoGuiFromShim",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\GRE_Initialize\\DisableMetaFiles",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\.NETFramework\\InstallRoot",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows NT\\CurrentVersion\\Windows\\LoadAppInit_DLLs",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\.NETFramework\\CLRLoadLogDir",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\.NETFramework\\OnlyUseLatestCLR"
],
"directory_enumerated": [
"C:\\Windows\\Microsoft.NET\\Framework\\v2.0.50727\\mscoreei.dll",
"C:\\Windows\\Microsoft.NET\\Framework\\Upgrades.2.0.50727\\mscoreei.dll",
"C:\\Windows\\Microsoft.NET\\Framework\\v4.0.30319\\mscorwks.dll"
]
}Generic
[
{
"process_path": "C:\\Windows\\System32\\lsass.exe",
"process_name": "lsass.exe",
"pid": 476,
"summary": {},
"first_seen": 1604008386.34375,
"ppid": 376
},
{
"process_path": "C:\\Users\\cuck\\AppData\\Local\\Temp\\34d54fc11ec26dc3645995c8cad58d22976293e6af1ec3789cfab640ace146b4.bin",
"process_name": "34d54fc11ec26dc3645995c8cad58d22976293e6af1ec3789cfab640ace146b4.bin",
"pid": 2500,
"summary": {
"dll_loaded": [
"ADVAPI32.dll",
"SHLWAPI.dll",
"C:\\Windows\\system32\\IMM32.DLL",
"gdi32.dll"
],
"file_failed": [
"C:\\Users\\cuck\\AppData\\Local\\Temp\\34d54fc11ec26dc3645995c8cad58d22976293e6af1ec3789cfab640ace146b4.bin.config"
],
"regkey_opened": [
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\.NETFramework\\Policy\\Upgrades",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\.NETFramework\\Policy\\Upgrades",
"HKEY_CURRENT_USER\\Software\\Microsoft\\.NETFramework\\Policy\\Standards",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\.NETFramework\\Policy\\Standards\\v4.0.30319",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\.NETFramework",
"HKEY_CURRENT_USER\\Software\\Microsoft\\.NETFramework",
"HKEY_CURRENT_USER\\Software\\Microsoft\\.NETFramework\\Policy\\Upgrades",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\.NETFramework\\Policy\\",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\.NETFramework\\Policy\\Standards",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\.NETFramework\\Policy\\AppPatch",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\.NETFramework\\Policy\\v2.0",
"HKEY_LOCAL_MACHINE\\Software\\Microsoft\\.NETFramework\\Policy\\Standards"
],
"file_exists": [
"C:\\Windows\\System32\\MSCOREE.DLL.local"
],
"file_opened": [
"C:\\Users\\cuck\\AppData\\Local\\Temp\\34d54fc11ec26dc3645995c8cad58d22976293e6af1ec3789cfab640ace146b4.bin"
],
"regkey_read": [
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\.NETFramework\\NoGuiFromShim",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion\\GRE_Initialize\\DisableMetaFiles",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\.NETFramework\\InstallRoot",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\Windows NT\\CurrentVersion\\Windows\\LoadAppInit_DLLs",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\.NETFramework\\CLRLoadLogDir",
"HKEY_LOCAL_MACHINE\\SOFTWARE\\Wow6432Node\\Microsoft\\.NETFramework\\OnlyUseLatestCLR"
],
"directory_enumerated": [
"C:\\Windows\\Microsoft.NET\\Framework\\v2.0.50727\\mscoreei.dll",
"C:\\Windows\\Microsoft.NET\\Framework\\Upgrades.2.0.50727\\mscoreei.dll",
"C:\\Windows\\Microsoft.NET\\Framework\\v4.0.30319\\mscorwks.dll"
]
},
"first_seen": 1604008386.609375,
"ppid": 1608
}
]Signatures
[
{
"markcount": 2,
"families": [],
"description": "The binary likely contains encrypted or compressed data indicative of a packer",
"severity": 2,
"marks": [
{
"entropy": 7.869151978941095,
"section": {
"size_of_data": "0x0000da00",
"virtual_address": "0x00002000",
"entropy": 7.869151978941095,
"name": ".text",
"virtual_size": "0x0000d9d4"
},
"type": "generic",
"description": "A section with a high entropy has been found"
},
{
"entropy": 0.956140350877193,
"type": "generic",
"description": "Overall entropy of this PE file is high"
}
],
"references": [
"http:\/\/www.forensickb.com\/2013\/03\/file-entropy-explained.html",
"http:\/\/virii.es\/U\/Using%20Entropy%20Analysis%20to%20Find%20Encrypted%20and%20Packed%20Malware.pdf"
],
"name": "packer_entropy"
}
]Yara
The Yara rules did not detect anything in the file.
Network
{
"tls": [],
"udp": [
{
"src": "192.168.56.101",
"dst": "192.168.56.255",
"offset": 662,
"time": 6.220831871032715,
"dport": 137,
"sport": 137
},
{
"src": "192.168.56.101",
"dst": "224.0.0.252",
"offset": 2350,
"time": 6.179390907287598,
"dport": 5355,
"sport": 51001
},
{
"src": "192.168.56.101",
"dst": "224.0.0.252",
"offset": 2678,
"time": 4.157063961029053,
"dport": 5355,
"sport": 53595
},
{
"src": "192.168.56.101",
"dst": "224.0.0.252",
"offset": 3006,
"time": 6.19123101234436,
"dport": 5355,
"sport": 53848
},
{
"src": "192.168.56.101",
"dst": "224.0.0.252",
"offset": 3334,
"time": 4.660184860229492,
"dport": 5355,
"sport": 54255
},
{
"src": "192.168.56.101",
"dst": "224.0.0.252",
"offset": 3662,
"time": 3.053804874420166,
"dport": 5355,
"sport": 55314
},
{
"src": "192.168.56.101",
"dst": "239.255.255.250",
"offset": 3990,
"time": 4.220813035964966,
"dport": 1900,
"sport": 1900
},
{
"src": "192.168.56.101",
"dst": "239.255.255.250",
"offset": 9368,
"time": 4.205857992172241,
"dport": 3702,
"sport": 49152
},
{
"src": "192.168.56.101",
"dst": "239.255.255.250",
"offset": 13560,
"time": 6.236129999160767,
"dport": 1900,
"sport": 53598
}
],
"dns_servers": [],
"http": [],
"icmp": [],
"smtp": [],
"tcp": [],
"smtp_ex": [],
"mitm": [],
"hosts": [],
"pcap_sha256": "21ce05815db6eeb15006817d5534b99edf746484012032e7f66e410762705ab7",
"dns": [],
"http_ex": [],
"domains": [],
"dead_hosts": [],
"sorted_pcap_sha256": "18f1e5e70f69775c5b512bb028e5a22abe713c086f48272fc02dd31960cbc3d0",
"irc": [],
"https_ex": []
}Screenshots

clientc.exe removal instructions
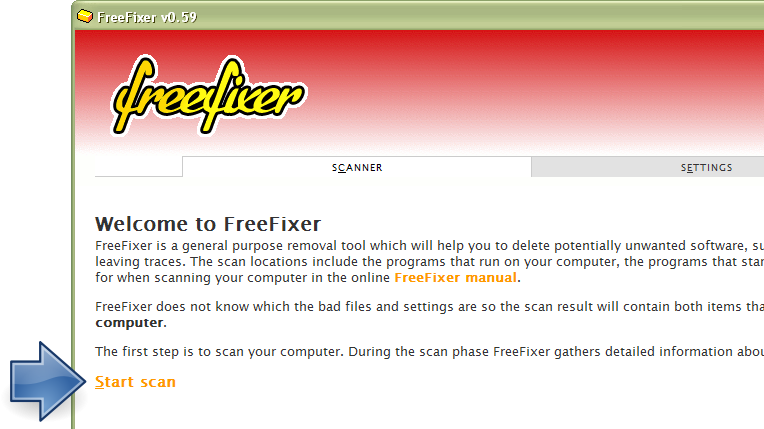
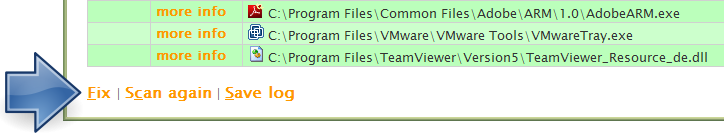
The instructions below shows how to remove clientc.exe with help from the FreeFixer removal tool. Basically, you install FreeFixer, scan your computer, check the clientc.exe file for removal, restart your computer and scan it again to verify that clientc.exe has been successfully removed. Here are the removal instructions in more detail:
- Download and install FreeFixer: http://www.freefixer.com/download.html
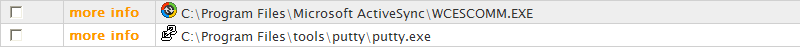
- When the scan is finished, locate clientc.exe in the scan result and tick the checkbox next to the clientc.exe file. Do not check any other file for removal unless you are 100% sure you want to delete it. Tip: Press CTRL-F to open up FreeFixer's search dialog to quickly locate clientc.exe in the scan result.


 c:\downloads\clientc.exe
c:\downloads\clientc.exe 
- Restart your computer.
- Start FreeFixer and scan your computer again. If clientc.exe still remains in the scan result, proceed with the next step. If clientc.exe is gone from the scan result you're done.
- If clientc.exe still remains in the scan result, check its checkbox again in the scan result and click Fix.
- Restart your computer.
- Start FreeFixer and scan your computer again. Verify that clientc.exe no longer appear in the scan result.
Hashes [?]
| Property | Value |
|---|---|
| MD5 | 004317b8cf9bf0a8595424977cecddd0 |
| SHA256 | 34d54fc11ec26dc3645995c8cad58d22976293e6af1ec3789cfab640ace146b4 |
Error Messages
These are some of the error messages that can appear related to clientc.exe:
clientc.exe has encountered a problem and needs to close. We are sorry for the inconvenience.
clientc.exe - Application Error. The instruction at "0xXXXXXXXX" referenced memory at "0xXXXXXXXX". The memory could not be "read/written". Click on OK to terminate the program.
CamtasiaStudio.exe has stopped working.
End Program - clientc.exe. This program is not responding.
clientc.exe is not a valid Win32 application.
clientc.exe - Application Error. The application failed to initialize properly (0xXXXXXXXX). Click OK to terminate the application.
What will you do with clientc.exe?
To help other users, please let us know what you will do with clientc.exe:
Comments
Please share with the other users what you think about this file. What does this file do? Is it legitimate or something that your computer is better without? Do you know how it was installed on your system? Did you install it yourself or did it come bundled with some other software? Is it running smoothly or do you get some error message? Any information that will help to document this file is welcome. Thank you for your contributions.
I'm reading all new comments so don't hesitate to post a question about the file. If I don't have the answer perhaps another user can help you.
No comments posted yet.