
Cuckoo is an open source automated malware analysis tool. Cuckoo can execute files and monitor the behaviour. And if you are running FreeFixer, your suspicious files will also be analysed by the sandbox. For free.
I’ll try to explain what Cuckoo can do more in detail by using examples from the Cuckoo reports on files listed here at freefixer.com:
One of the most useful features is that Cuckoo can trace API calls. Here’s an example from RunBoosterUpdateTask64.exe, where you can see that it calls CreateServiceW to register a driver named WinDivert64.sys. This is pretty useful if you are trying to find out what a particular file on your system is doing.
"call": {
"category": "services",
"status": 1,
"stacktrace": [],
"api": "CreateServiceW",
"return_value": 4536928,
"arguments": {
"service_start_name": "",
"start_type": 2,
"service_handle": "0x0000000000453a60",
"display_name": "WinDivert1.2",
"error_control": 1,
"service_name": "WinDivert1.2",
"filepath": "C:\\Windows\\System32\\drivers\\WinDivert64.sys",
"filepath_r": "C:\\Windows\\system32\\drivers\\WinDivert64.sys",
"service_manager_handle": "0x0000000000453a00",
"desired_access": 983551,
"service_type": 1,
"password": ""
},
"time": 1576385586.79675,
"tid": 2436,
"flags": {}
}
Cuckoo also monitors host resolving. Here’s another example from the log where RunBoosterUpdateTask64.exe tries to get the IP address for update.updinfo.xyz:
"resolves_host": [ "update.updinfo.xyz" ]
And the list goes on. Cuckoo detects anti-virtualisation tactics. For example, Cuckoo will notice if the file under test checks for existence of VMware/VirtualBox registry keys or files.
Here’s an example from armsvc.exe where Cuckoo notice that the process is trying to detect if it is running in VMware using an instruction:
{
"markcount": 1,
"families": [],
"description": "Detects VMWare through the in instruction feature",
"severity": 3,
...
Cuckoo will detect potential compressed or encrypted data in the executable files by measuring the entropy in the file. Cuckoo can also step through installation wizards and takes screenshots during the analysis. It will also log UDP and TCP connection.
I’m impressed by all the features.
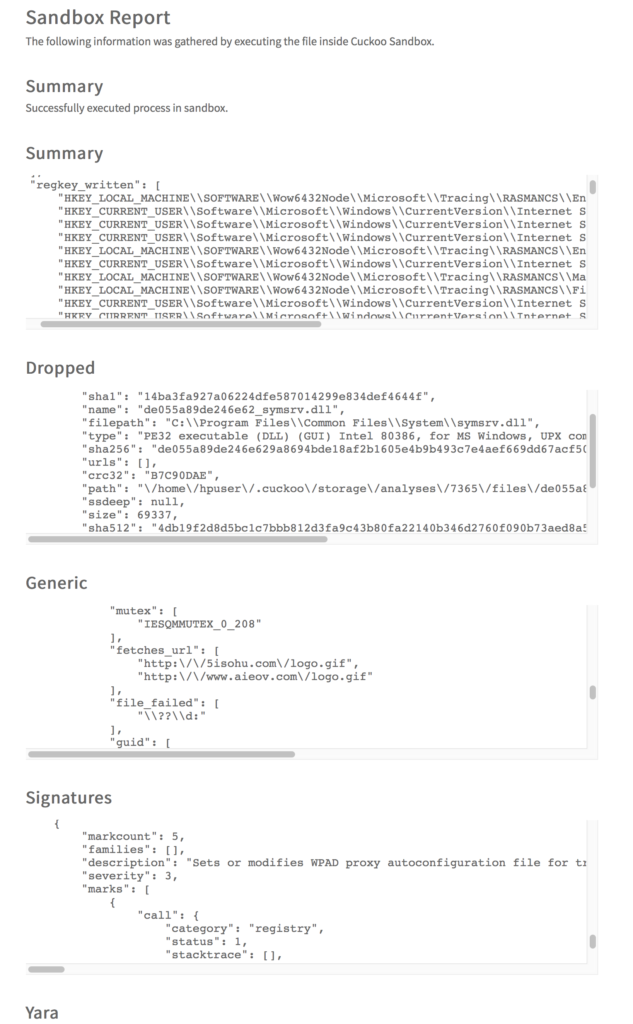
So, I’ve set up a Cuckoo installation that freefixer.com will use to analyse files. The approach is simple. Freefixer.com will upload files to sandbox and after a while the analysis will be displayed on the web site. I’ve decided to display the Summary, Generic, Dropped, Signatures, Yara, and Network sections from the sandbox report. Here’s an example report for armsvc.exe:
I’ve been running Cuckoo for some time now, and it has analysed more that 6000 files. I’m pretty happy with the result so far. Cuckoo just keeps on running, analysing one file after another.
I’ve identified a number of issues that needs to be addressed:
- Lots of noise! The reports from Cuckoo can be quite verbose and it can be difficult for users to identify the most interesting parts of the log. This is pretty difficult problem that I’m not sure how to fix. An automated approach is needed to pinpoint the most interesting parts of the log.
- Identical screenshots. The sandbox generates screenshots that are almost identical. I’m currently using ImageMagick to compare images for similarity but it does not work good enough. I think the code needs another round of tuning.
- The web site needs to explain what the items in the log means. For example, what does UPD packets sent from the local host to
224.0.0.255at port5355mean? (It’s a name resolution for hosts on the same local link) - The JSON reports are shown in fixed size text-areas (
<pre></pre>) with vertical and horizontal scrollbars. Works OK when the amount of JSON data is small. Works terrible when dealing with large amount of data. Please let me know if you have some ideas on how to present the JSON data in smart ways.
I’m hoping, now that you have another tool to analyse files, that this will help you to track down and remove that malware running on your machine.