Hi there! Short on time this evening, but I just wanted to give you the heads up on a publisher called LLC DE PROEKT.
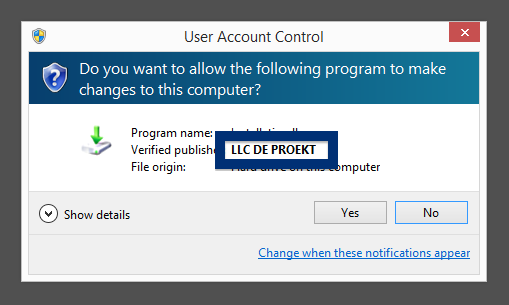
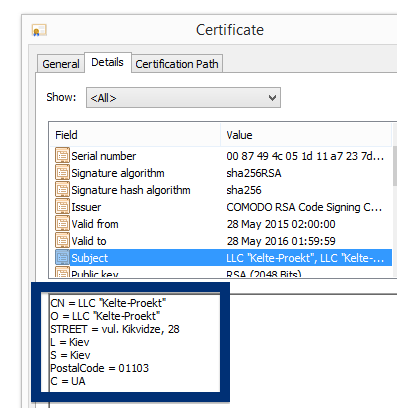
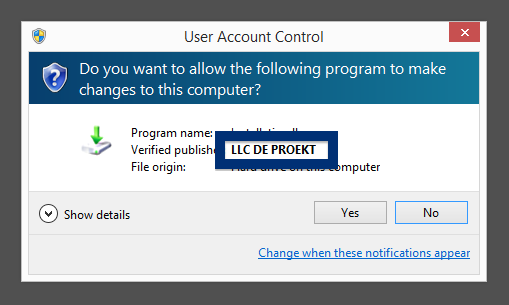
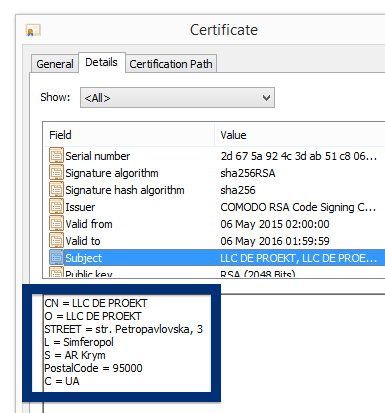
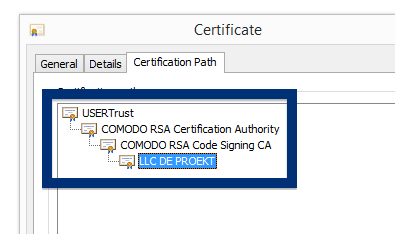
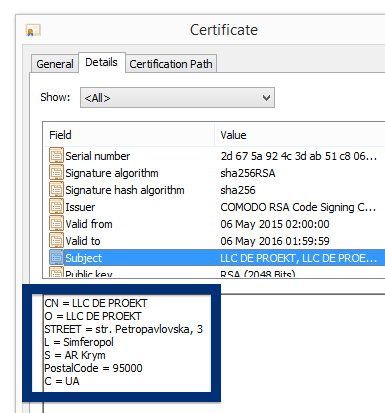
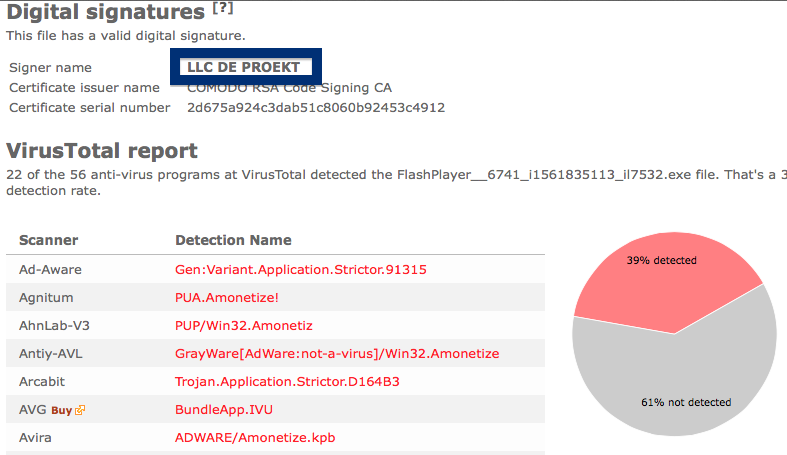
If you have a LLC DE PROEKT file on your machine you may have noticed that LLC DE PROEKT is displayed as the publisher in the UAC dialog when double-clicking on the file. The certificate is issued by COMODO RSA Code Signing CA. The publisher is located in the Ukraine.
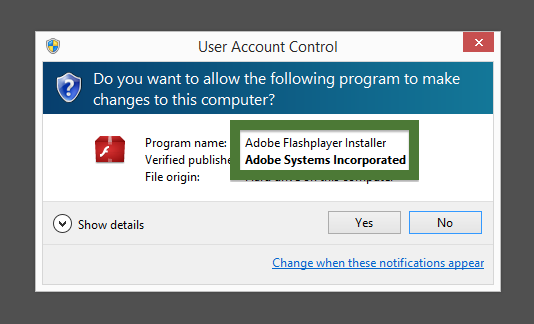
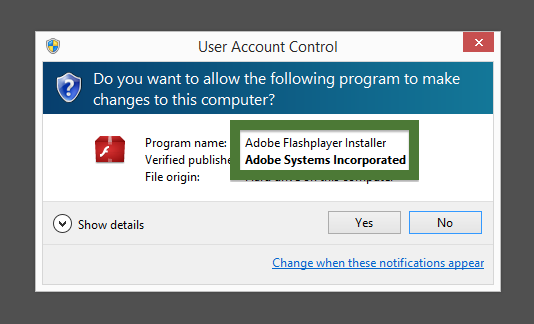
The problem here is that if FlashPlayer__6741_i1561835113_il7532.exe really was a setup file for Adobe Flash Player, it should have been digitally signed by Adobe Systems Incorporated and not by some unknown company. This looks suspicious. Here’s how the authentic Adobe Flash Player looks like when you double click on it. Notice that the “Verified publisher” says “Adobe Systems Incorporated”.
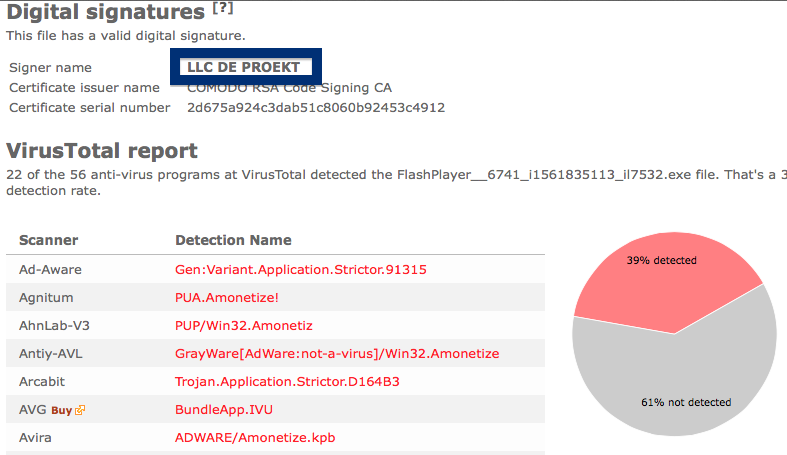
The issue with the LLC DE PROEKT file is that it is detected by many of the antimalware software. Here are some of the detection names: Trojan.Application.Strictor.D164B3, BundleApp.IVU, W32.HfsAdware.B493, Gen:Variant.Application.Strictor, PUP.Optional.Bundle and Amonetize (fs).
Did you also find a download that was digitally signed by LLC DE PROEKT? What kind of download was it and was it detected by the anti-viruses at VirusTotal? Please share by posting a comment.
Thanks for reading.
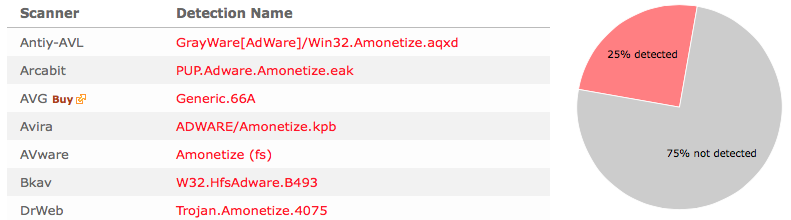
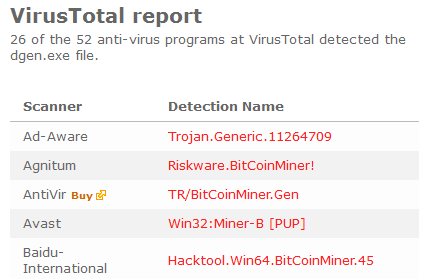
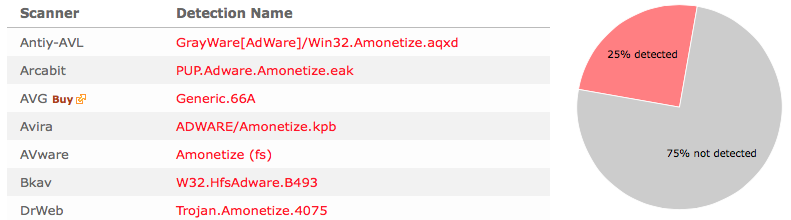
Update 2015-08-18: Found another download today, also signed by LLC DE PROEKT and also using “Flash” in the filename to confuse users. The detection rate for this file was 25% according to VirusTotal:
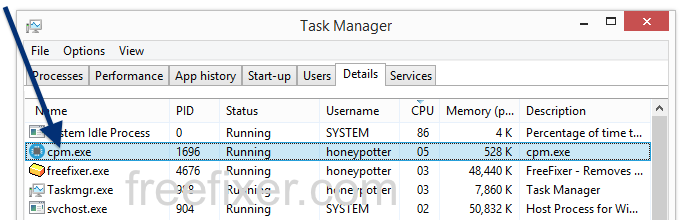
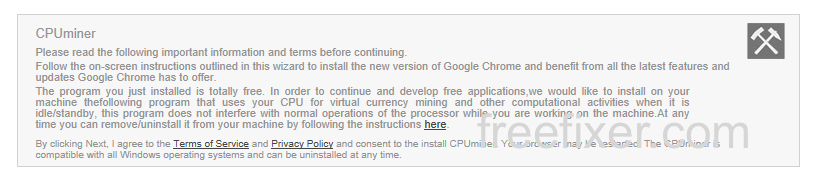
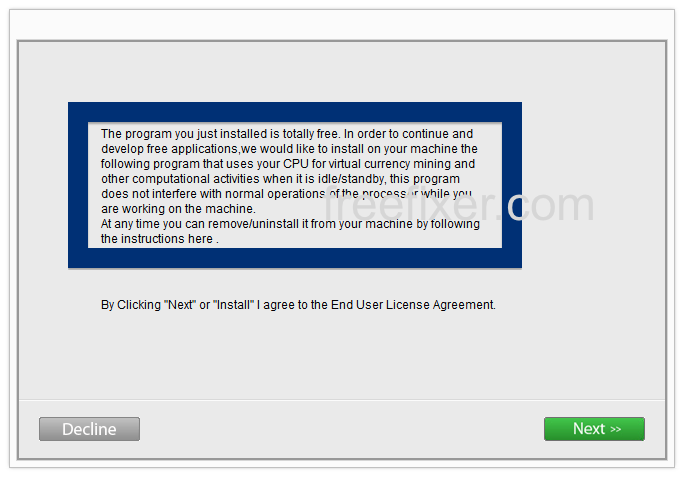
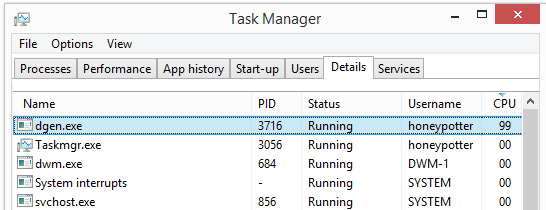
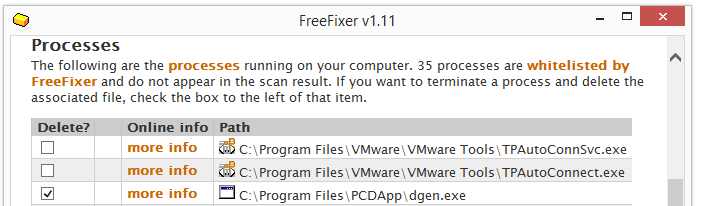
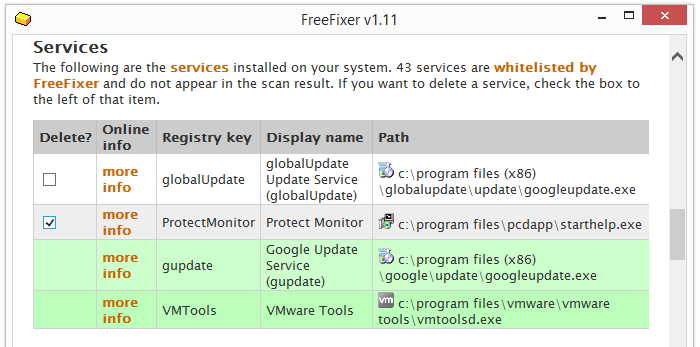
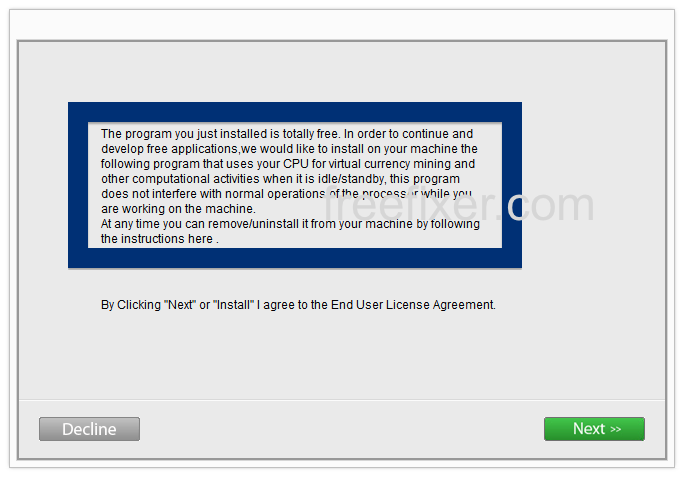
When I ran the installer it disclosed that it bundled a bitcoin miner or some other type of crypto currency miner:
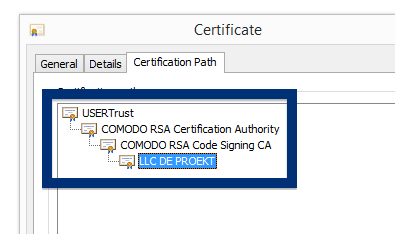
Just a quick update on the certificate chain. It begins with UserTrust, then Comodo and then LLC DE PROEKT: