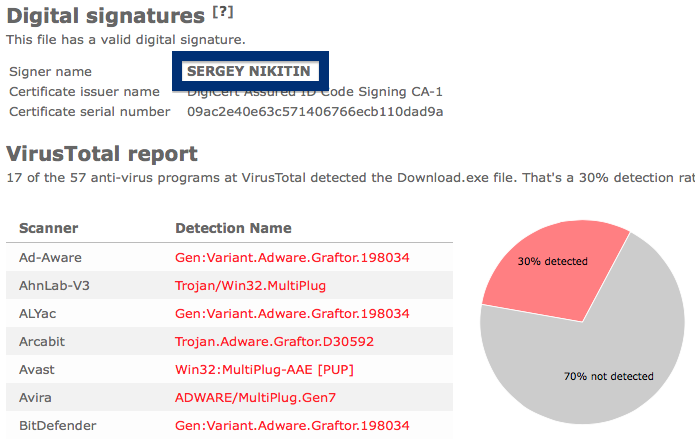
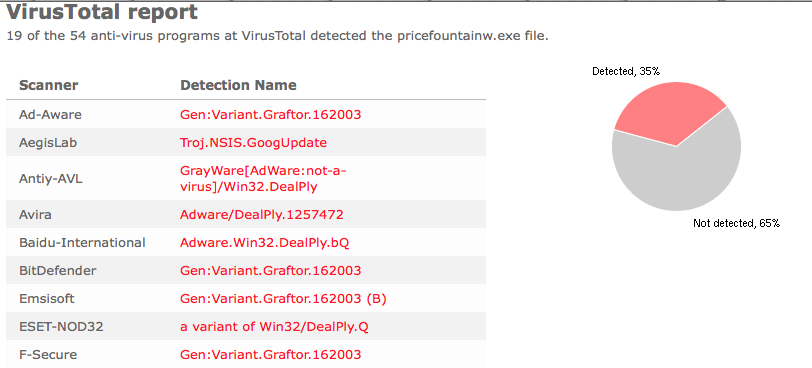
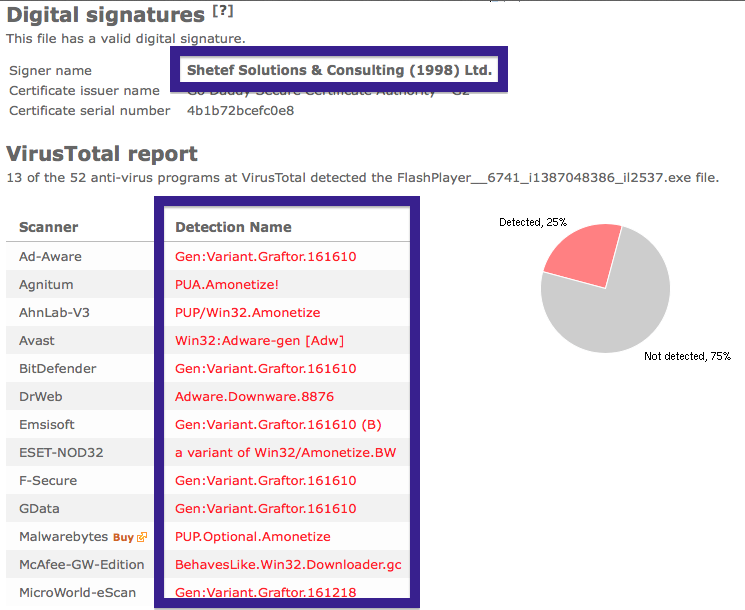
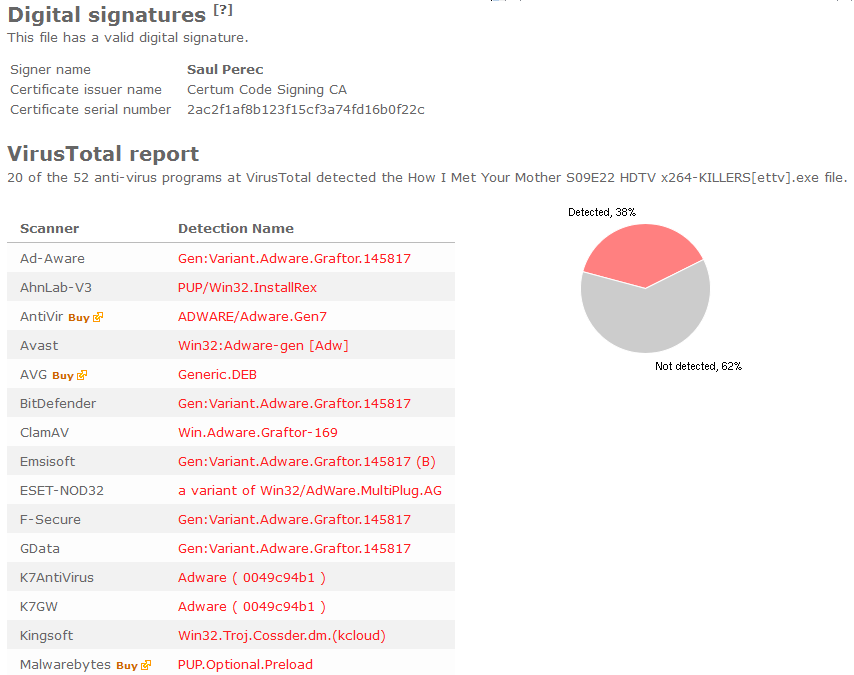
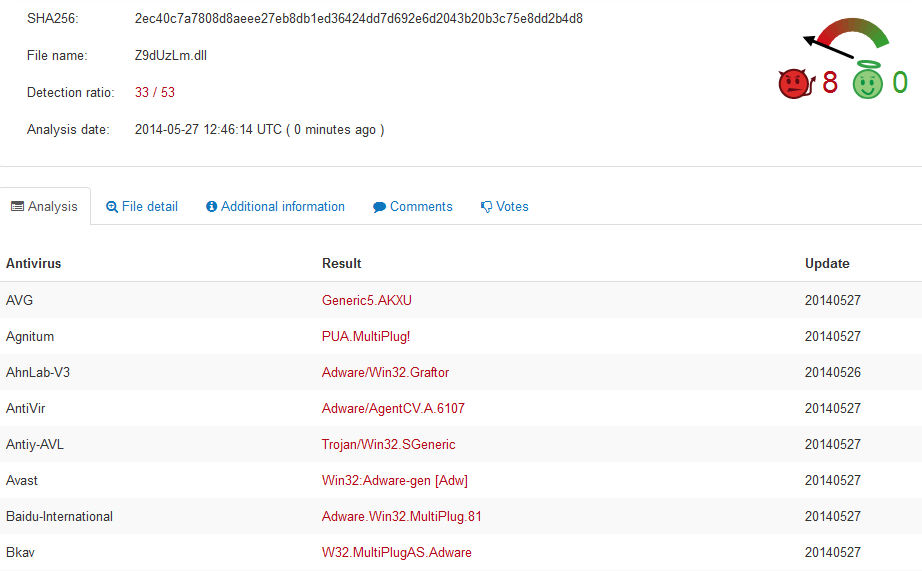
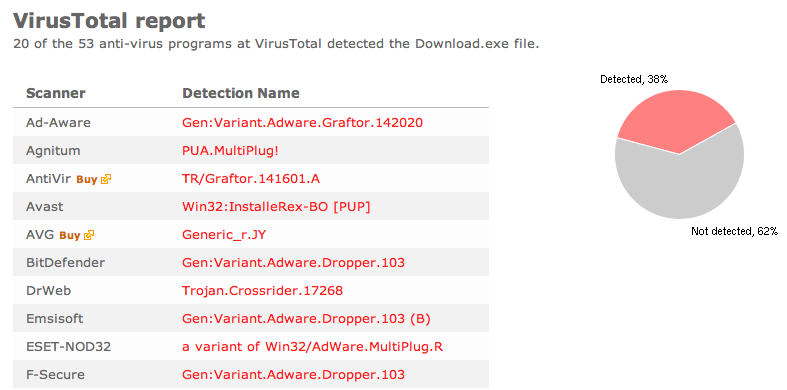
Welcome! Just a note on a publisher called Egor Klochko. The Egor Klochko download – Download Uc Browser V Handler Zip.exe – was detected when I uploaded it to VirusTotal. Did you also find a download by Egor Klochko? Was it also detected when you uploaded it to VirusTotal?
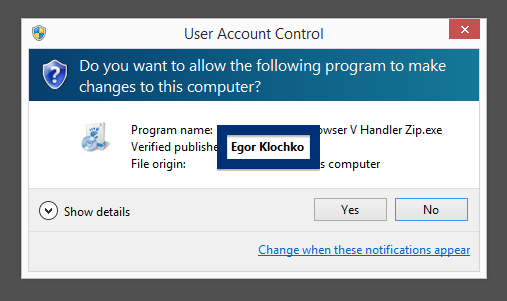
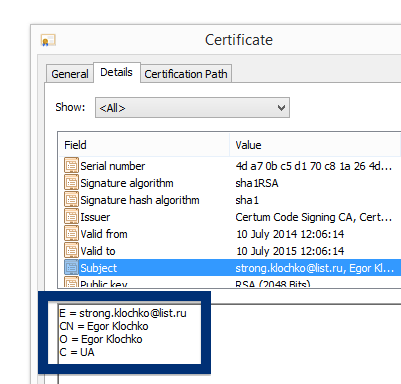
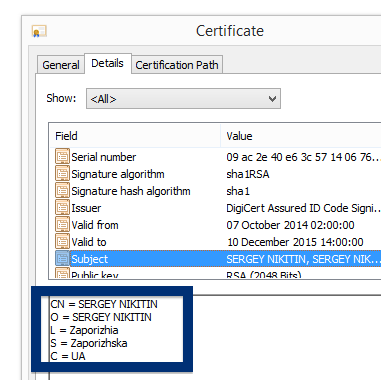
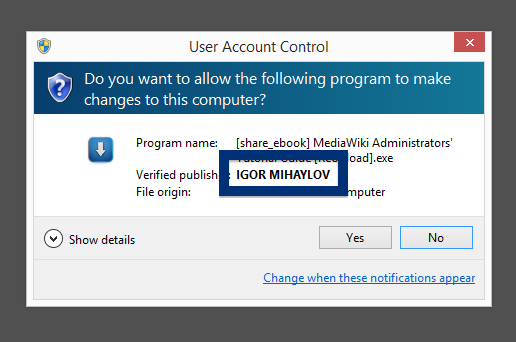
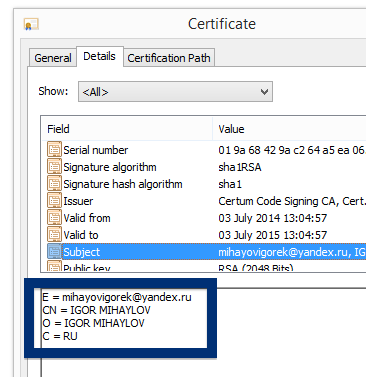
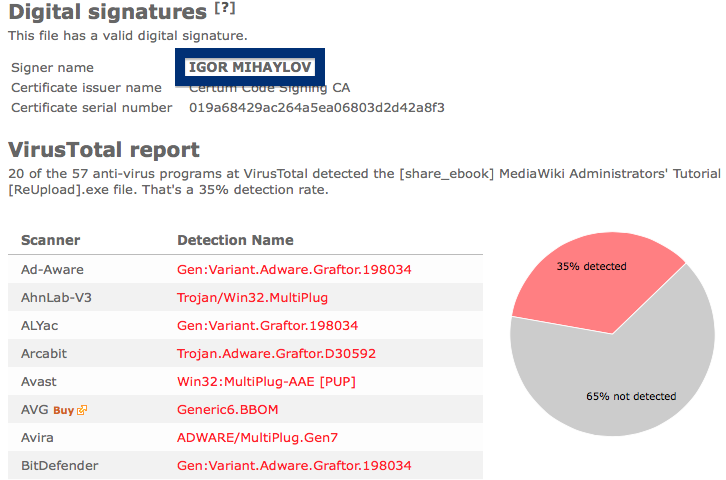
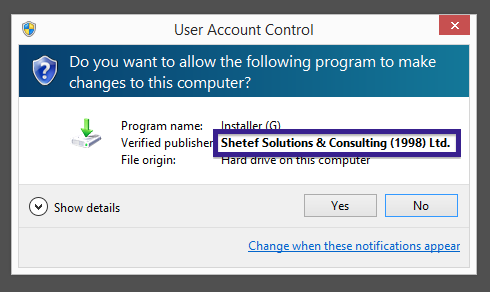
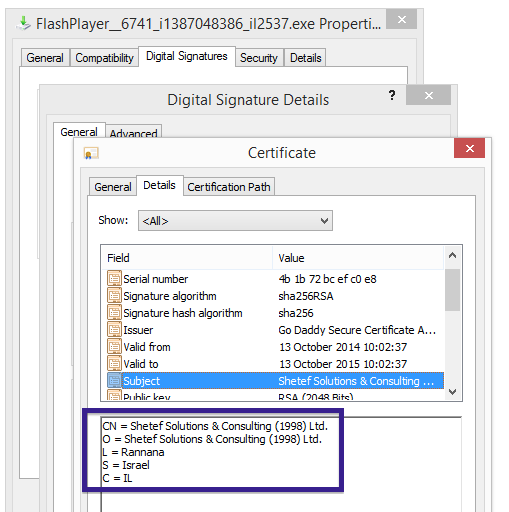
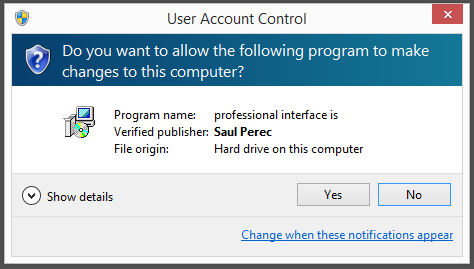
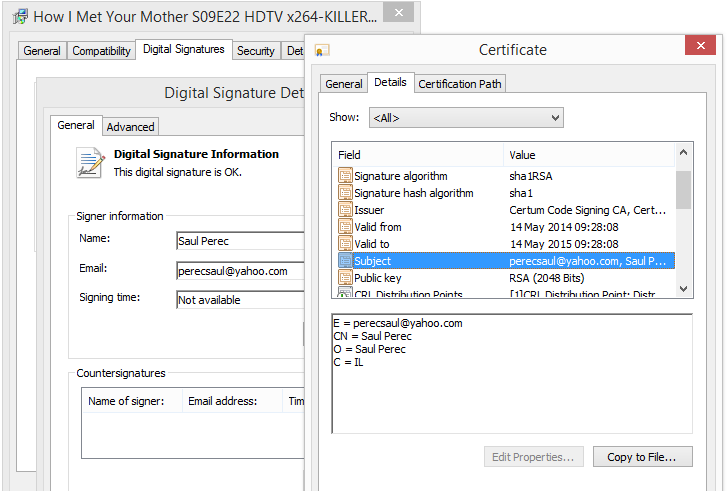
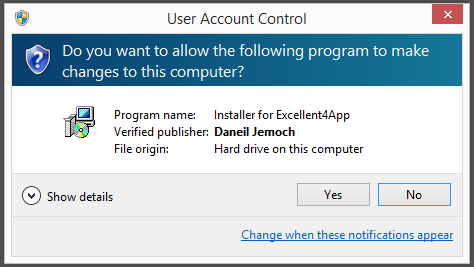
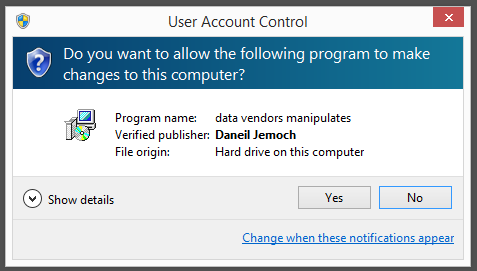
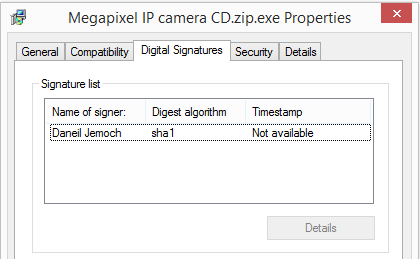
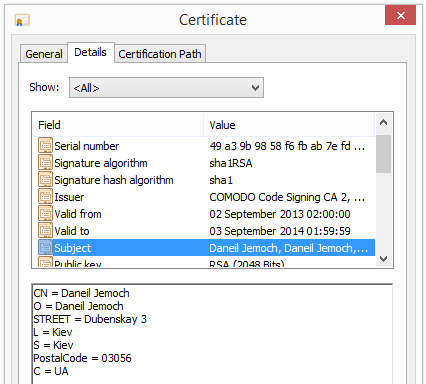
Typically you’d see the Egor Klochko publisher name appear when double-clicking on the Download Uc Browser V Handler Zip.exe file: It is also possible to check a digital signature by looking at a file’s properties. Here’s a screenshot of the Egor Klochko certificate.
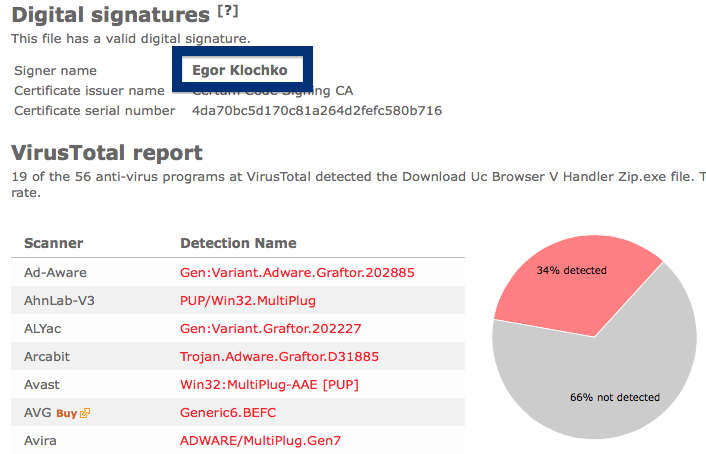
The VirusTotal report shows that the Egor Klochko file should be avoided, since Download Uc Browser V Handler Zip.exe is detected as Trojan.Adware.Graftor.D31885 by Arcabit, Gen:Variant.Adware.Graftor.202885 by BitDefender and PUP.Optional.Multiplug by Malwarebytes.
Did you also find a Egor Klochko file? Do you remember where you downloaded it?
Thank you for reading.