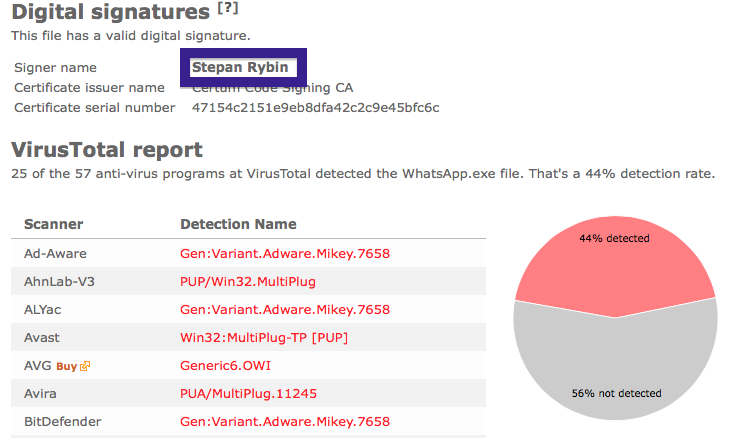
Hello! Did you see a file, such as WhatsApp.exe, on your system signed by Stepan Rybin? Then read on..
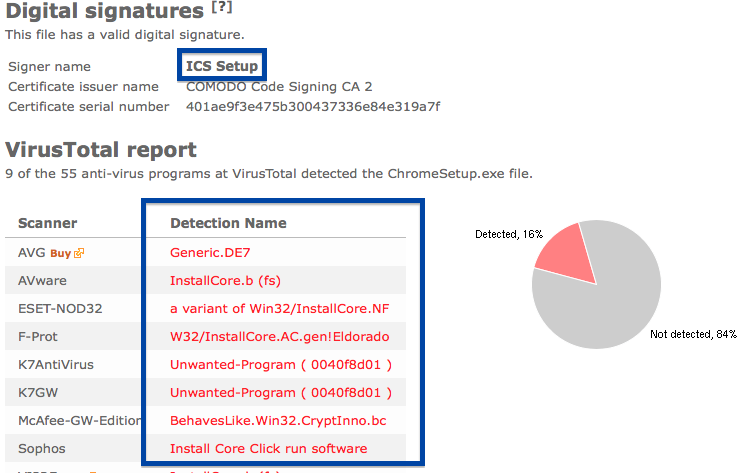
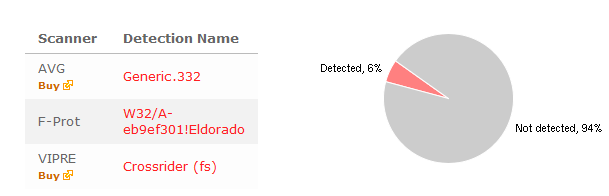
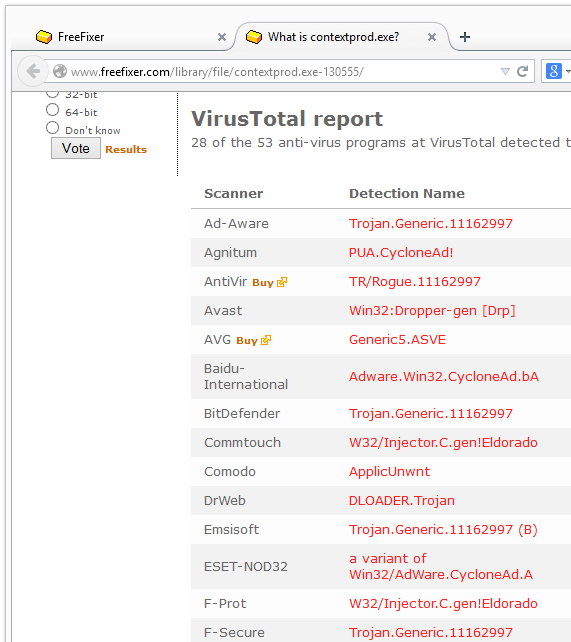
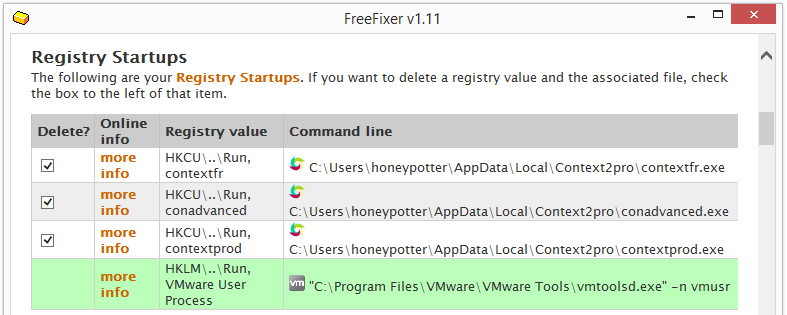
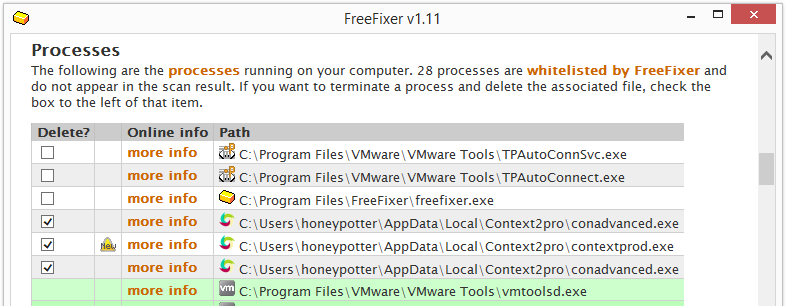
I found this Stepan Rybin file while reviewing some of the submissions to the FreeFixer web site. I thought it looked a little bit like a typical “MultiPlug” adware file and the VirusTotal scan result showed that was the case. Ad-Aware reports WhatsApp.exe as Gen:Variant.Adware.Mikey.7658, Avast calls it Win32:MultiPlug-TP [PUP], Cyren names it W32/S-05e718fa!Eldorado, F-Prot calls it W32/S-05e718fa!Eldorado and Sophos detects it as MultiPlug.
Did you also find a Stepan Rybin download? Do you remember where you downloaded it? Please post the URL in the comments below. I’d like to install this download on my lab machine to have a closer look at it.
Thank you for reading.